網絡掃描:系統識別
我們不僅可以通過相應工具識別目標主機上的服務指紋信息,還可以進行系統指紋信息識別。常見的系統指紋信息有操作系統類型、系統版本和內核版本等。本文介紹系統識別的方法。
1. Nmap系統識別
在Nmap工具中,提供了一些選項可以用來實施系統識別。下面介紹具體的實現方法。
(1)識別操作系統
在Nmap工具中提供了一個-O選項,可以用來識別操作系統。用于識別操作系統的語法格式如下:
nmap -O [host]
其中,-O選項用于識別操作系統類型。注意,這里的選項-O是大寫字母O,不是0。
識別目標主機192.168.33.152的操作系統類型。執行命令如下:
root@daxueba:~# nmap -O 192.168.33.152
Starting Nmap 7.70 ( https://nmap.org ) at 2021-08-02 15:22 CST
Nmap scan report for 192.168.33.152 (192.168.33.152)
Host is up (0.00036s latency).
Not shown: 997 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:FD:58:4B (VMware) #MAC地址
Device type: general purpose #設備類型
Running: Linux 3.X|4.X #運行的系統
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 #操作系統中央處理單元
OS details: Linux 3.2 - 4.9 #操作系統詳細信息
Network Distance: 1 hop #網絡距離,即從源到目標經過的網絡節點
OS detection performed. Please report any incorrect results at https://nmap.
org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1.86 seconds
從以上輸出信息中可以看到,目標主機的操作系統類型為Linux,內核版本為3.2。如果Nmap不能夠判斷出目標操作系統的話,將會提供指紋信息給Nmap的系統數據庫。例如,識別目標主機10.10.1.11的操作系統。執行命令如下:
root@daxueba:~# nmap -O 10.10.1.11
Starting Nmap 7.70 ( https://nmap.org ) at 2021-08-02 15:29 CST
……
No exact OS matches for host (If you know what OS is running on it, see http://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=5.00%D=12/16%OT=3001%CT=1%CU=32781%PV=Y%DS=1%G=Y%M=00204A%TM=4B29
OS:4048%P=i686-pc-windows-windows)SEQ(CI=I%II=I%TS=U)OPS(O1=M400%O2=%O3=%O4
OS:=%O5=%O6=)OPS(O1=M400%O2=M400%O3=%O4=%O5=%O6=)OPS(O1=%O2=M400%O3=M400%O4
OS:=%O5=%O6=)OPS(O1=%O2=%O3=M400%O4=%O5=%O6=)OPS(O1=M400%O2=%O3=M400%O4=%O5
OS:=%O6=)WIN(W1=7FF%W2=0%W3=0%W4=0%W5=0%W6=0)WIN(W1=7FF%W2=7FF%W3=0%W4=0%W5
OS:=0%W6=0)WIN(W1=0%W2=7FF%W3=7FF%W4=0%W5=0%W6=0)WIN(W1=0%W2=0%W3=7FF%W4=0%
OS:W5=0%W6=0)WIN(W1=7FF%W2=0%W3=7FF%W4=0%W5=0%W6=0)ECN(R=Y%DF=Y%T=40%W=0%O=
OS:%CC=N%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T1(R=Y%DF=Y%T=40%S=O%A=O
OS:%F=AS%RD=0%Q=)T1(R=Y%DF=Y%T=40%S=Z%A=S+%F=AR%RD=0%Q=)T2(R=Y%DF=Y%T=40%W=
OS:0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=
OS:)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=
OS:S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF
OS:=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=Y%T=40%IPL=38%UN=0%RIPL=G
OS:%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=S%T=40%CD=S)
以上輸出信息就是Nmap向數據庫提交的指紋信息,這些指紋信息是自動生成的,并且標識了目標系統的操作系統。
(2)指定識別的操作系統
當掃描多個主機時,可以使用--osscan-limit選項來指定識別特定主機的操作系統類型。這樣,使用該選項進行操作系統識別可以節約大量的時間。指定識別主機的操作系統類型語法格式如下:
nmap -O --osscan-limit [host]
其中,--osscan-limit選項表示針對指定的目標進行操作系統檢測。如果發現一個打開和關閉的TCP端口時,操作系統檢測會更有效。使用該選項,Nmap只對滿足這個條件的主機進行操作系統檢測。這樣可以節約時間,特別是在使用-P0掃描多個主機時。該選項僅在使用-O或-A進行操作系統檢測時起作用。
使用Nmap針對指定的目標進行操作系統檢測。執行命令如下:
root@daxueba:~# nmap -P0 192.168.1.0/24 -O --osscan-limit
Starting Nmap 7.70 ( https://nmap.org ) at 2021-08-02 16:02 CST
Nmap scan report for 192.168.1.1 (192.168.1.1)
Host is up (0.00073s latency).
Not shown: 994 closed ports
PORT STATE SERVICE
21/tcp open ftp
80/tcp open http
445/tcp open microsoft-ds
5678/tcp open rrac
8080/tcp open http-proxy
52869/tcp open unknown
MAC Address: 70:85:40:53:E0:35 (Unknown)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9 #操作系統詳細信息
Network Distance: 1 hop
Nmap scan report for kdkdahjd61y369j (192.168.1.3)
Host is up (0.000085s latency).
All 1000 scanned ports on kdkdahjd61y369j (192.168.1.3) are filtered
MAC Address: 1C:6F:65:C8:4C:89 (Giga-byte Technology)
Nmap scan report for test-pc (192.168.1.5)
Host is up (0.00047s latency).
Not shown: 982 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
902/tcp open iss-realsecure
912/tcp open apex-mesh
1433/tcp open ms-sql-s
2383/tcp open ms-olap4
5357/tcp open wsdapi
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49157/tcp open unknown
49158/tcp open unknown
MAC Address: 00:0C:29:21:8C:96 (VMware)
Device type: general purpose
Running: Microsoft Windows 7|2008|8.1
OS CPE: cpe:/o:microsoft:windows_7::- cpe:/o:microsoft:windows_7::sp1
cpe:/o:microsoft:windows_server_2008::sp1 cpe:/o:microsoft:windows_server_
2008:r2 cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows_8.1
OS details: Microsoft Windows 7 SP0 - SP1, Windows Server 2008 SP1, Windows
Server 2008 R2, Windows 8, or Windows 8.1 Update 1 #操作系統詳細信息
Network Distance: 1 hop
Nmap scan report for 192.168.1.6 (192.168.1.6)
Host is up (0.00057s latency).
Not shown: 977 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
23/tcp open telnet
25/tcp open smtp
53/tcp open domain
80/tcp open http
111/tcp open rpcbind
139/tcp open netbios-ssn
445/tcp open microsoft-ds
512/tcp open exec
513/tcp open login
514/tcp open shell
1099/tcp open rmiregistry
1524/tcp open ingreslock
2049/tcp open nfs
2121/tcp open ccproxy-ftp
3306/tcp open mysql
5432/tcp open postgresql
5900/tcp open vnc
6000/tcp open X11
6667/tcp open irc
8009/tcp open ajp13
8180/tcp open unknown
MAC Address: 00:0C:29:3E:84:91 (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33 #操作系統詳細信息
Network Distance: 1 hop
Nmap scan report for kali (192.168.1.9)
Host is up (0.00093s latency).
All 1000 scanned ports on kali (192.168.1.9) are closed
MAC Address: 00:0C:29:6C:C4:92 (VMware)
Nmap scan report for daxueba (192.168.1.4)
Host is up (0.000010s latency).
All 1000 scanned ports on daxueba (192.168.1.4) are closed
OS detection performed. Please report any incorrect results at
https://nmap.org/submit/ .
Nmap done: 256 IP addresses (6 hosts up) scanned in 7.64 seconds
從以上輸出信息可以看到,如果探測到目標主機上存在開放的端口,則推測出了其操作系統類型;如果目標主機上不存在開放的端口,則無法推測其操作系統類型。
(3)推測操作系統
當Nmap無法確定所探測的操作系統時,會盡可能地提供最相近的匹配。為了對目標系統推測得更準確,可以使用--osscan-guess或--fuzzy選項來實現。語法格式如下:
nmap -O --osscan-guess;--fuzzy [host]
其中,--osscan-guess;--fuzzy選項用于推測操作系統檢測結果,將以百分比的方式給出對操作系統信息的猜測。當Nmap無法確定所檢測的操作系統時,會盡可能地提供最相近的匹配。Nmap默認進行這種匹配,使用任意一個選項將使得Nmap的推測更加有效。
推測目標主機www.163.com的操作系統類型。執行命令如下:
root@daxueba:~# nmap -O --osscan-guess www.163.com
Starting Nmap 7.70 ( https://nmap.org ) at 2021-08-02 16:08 CST
Nmap scan report for www.163.com (124.163.204.105)
Host is up (0.015s latency).
Other addresses for www.163.com (not scanned): 2408:8726:5100::4f
rDNS record for 124.163.204.105: 105.204.163.124.in-addr.arpa
Not shown: 955 closed ports
PORT STATE SERVICE
80/tcp open http
81/tcp open hosts2-ns
82/tcp open xfer
84/tcp open ctf
88/tcp open kerberos-sec
135/tcp filtered msrpc
139/tcp filtered netbios-ssn
443/tcp open https
445/tcp filtered microsoft-ds
……省略部分內容
Device type: general purpose|firewall|media device|phone|broadband router security-misc
Running (JUST GUESSING): Linux 3.X|2.6.X|4.X (92%), IPCop 2.X (91%), Tiandy
embedded (91%), Google Android 5.X (90%), D-Link embedded (90%), Draytek
embedded (89%)
OS CPE: cpe:/o:linux:linux_kernel:3.2 cpe:/o:linux:linux_kernel:2.6.32
cpe:/o:ipcop:ipcop:2.0 cpe:/o:linux:linux_kernel:4.9 cpe:/o:google:
android:5.0.1 cpe:/h:dlink:dsl-2890al cpe:/o:linux:linux_kernel:2.6.25.20
cpe:/h:draytek:vigor_2960
Aggressive OS guesses: Linux 3.2 (92%), IPCop 2.0 (Linux 2.6.32) (91%), Linux
2.6.32 (91%), Linux 4.9 (91%), Tiandy NVR (91%), Android 5.0.1 (90%), Linux
3.18 (90%), D-Link DSL-2890AL ADSL router (90%), OpenWrt Kamikaze 8.09 (Linux
2.6.25.20) (90%), Linux 2.6.18 - 2.6.22 (89%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 9 hops
OS detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 5.65 seconds
以上輸出信息顯示了目標主機可能使用的操作系統列表。這里列舉可能的系統類型,并以百分比形式顯示每種類型的概率。從輸出結果顯示的比例中可以看到,目標主機的操作系統類型可能是Linux 3.2。
2. Ping系統識別
Ping是Windows、UNIX和Linux系統下的一個命令,使用該命令可以檢查網絡是否連通。如果目標主機正確響應的話,在響應包中將包括有對應的TTL值。TTL是Time To Live(生成時間)的縮寫,該字段指定IP包被路由器丟棄之前允許通過的最大網段數量。其中,不同操作系統類型響應的TTL值不同。所以我們可以使用Ping命令進行系統識別。下面介紹使用Ping命令實施系統識別的方法。
為了能夠快速地確定一個目標系統的類型,下面給出了一個操作系統初始TTL值列表,如表1所示。
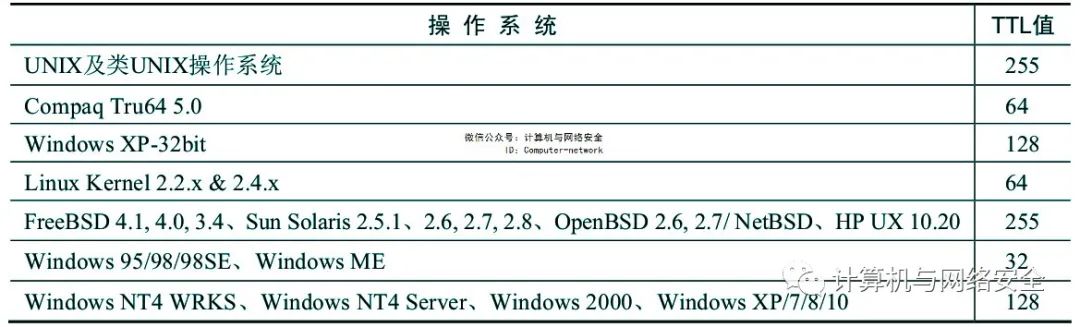
表1 各個操作系統的初始TTL值
使用Ping測試目標主機(192.168.33.152)的操作系統類型(該目標主機的操作系統類型為Linux)。執行命令如下:
root@daxueba:~# ping 192.168.33.152
PING 192.168.33.152 (192.168.33.152) 56(84) bytes of data.
64 bytes from 192.168.33.152: icmp_seq=1 ttl=64 time=0.242 ms
64 bytes from 192.168.33.152: icmp_seq=2 ttl=64 time=0.431 ms
64 bytes from 192.168.33.152: icmp_seq=3 ttl=64 time=0.431 ms
64 bytes from 192.168.33.152: icmp_seq=4 ttl=64 time=0.440 ms
從輸出的信息可以看到,響應包中的TTL值為64。根據前面列出的表格6.1,可以看到這是Linux操作系統。
使用Ping測試目標主機(192.168.33.229)的操作系統類型(該目標主機的操作系統類型為Windows 7)。執行命令如下:
root@daxueba:~# ping 192.168.33.229
PING 192.168.33.229 (192.168.33.229) 56(84) bytes of data.
64 bytes from 192.168.33.229: icmp_seq=1 ttl=128 time=1.57 ms
64 bytes from 192.168.33.229: icmp_seq=2 ttl=128 time=1.01 ms
64 bytes from 192.168.33.229: icmp_seq=3 ttl=128 time=0.276 ms
64 bytes from 192.168.33.229: icmp_seq=4 ttl=128 time=1.52 ms
從輸出的信息可以看到,該響應包中的TTL值為128。由此可以說明,這是一個Windows操作系統。
3. xProbe2系統識別
xProbe2是一款遠程主機操作系統探查工具,該工具通過ICMP協議來獲得指紋。xProbe2通過模糊矩陣統計分析主動探測數據報文對應的ICMP數據報特征,進而探測得到遠端操作系統的類型。下面介紹使用xProbe2工具實施操作系統指紋識別的方法。使用xProbe2工具實施系統識別的語法格式如下:
xProbe2 [host]
使用xProbe2工具對目標主機www.163.com實施系統識別。執行命令如下:
root@Kali:~# xprobe2 www.163.com
Xprobe2 v.0.3 Copyright (c) 2002-2005 fyodor@o0o.nu, ofir@sys-security.com,meder@o0o.nu
[+] Target is www.163.com #目標地址
[+] Loading modules. #正在加載模塊
[+] Following modules are loaded: #被加載的模塊
[x] [1] ping:icmp_ping - ICMP echo discovery module
[x] [2] ping:tcp_ping - TCP-based ping discovery module
[x] [3] ping:udp_ping - UDP-based ping discovery module
[x] [4] infogather:ttl_calc - TCP and UDP based TTL distance calculation
[x] [5] infogather:portscan - TCP and UDP PortScanner
[x] [6] fingerprint:icmp_echo - ICMP Echo request fingerprinting module
[x] [7] fingerprint:icmp_tstamp - ICMP Timestamp request fingerprinting module
[x] [8] fingerprint:icmp_amask - ICMP Address mask request fingerprinting module
[x] [9] fingerprint:icmp_port_unreach - ICMP port unreachable fingerprinting module
[x] [10] fingerprint:tcp_hshake - TCP Handshake fingerprinting module
[x] [11] fingerprint:tcp_rst - TCP RST fingerprinting module
[x] [12] fingerprint:smb - SMB fingerprinting module
[x] [13] fingerprint:snmp - SNMPv2c fingerprinting module
[+] 13 modules registered
[+] Initializing scan engine #初始化掃描引擎
[+] Running scan engine #正在實施掃描
[-] ping:tcp_ping module: no closed/open TCP ports known on 124.163.204.105.
Module test failed
[-] ping:udp_ping module: no closed/open UDP ports known on 124.163.204.105.
Module test failed
[-] No distance calculation. 124.163.204.105 appears to be dead or no ports known
[+] Host: 124.163.204.105 is up (Guess probability: 50%)#主機是活動的
[+] Target: 124.163.204.105 is alive. Round-Trip Time: 0.01503 sec
[+] Selected safe Round-Trip Time value is: 0.03007 sec
[-] fingerprint:tcp_hshake Module execution aborted (no open TCP ports known)
[-] fingerprint:smb need either TCP port 139 or 445 to run
[-] fingerprint:snmp: need UDP port 161 open
[+] Primary guess: #主要猜測
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.19" (Guess
probability: 100%)
[+] Other guesses: #其他猜測
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.20" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.21" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.22" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.23" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.24" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.25" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.26" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.27" (Guess
probability: 100%)
[+] Host 124.163.204.105 Running OS: "Linux Kernel 2.4.28" (Guess
probability: 100%)
[+] Cleaning up scan engine
[+] Modules deinitialized
[+] Execution completed.
從輸出的信息中可以看到,通過xProbe2工具成功解析出了目標主機的IP地址,并且識別出了其操作系統類型。其中,目標主機的IP地址為124.163.204.105,操作系統類型為Linux,內核版本在2.4.19~2.4.28之間。
xProbe2工具在NAT模式下存在Bug,掃描后會出現HP的位置或者直接報錯,具體如下:
root@Kali:~# xprobe2 www.163.com
Xprobe2 v.0.3 Copyright (c) 2002-2005 fyodor@o0o.nu, ofir@sys-security.com,meder@o0o.nu
[+] Target is www.163.com
[+] Loading modules.
[+] Following modules are loaded:
[x] [1] ping:icmp_ping - ICMP echo discovery module
[x] [2] ping:tcp_ping - TCP-based ping discovery module
[x] [3] ping:udp_ping - UDP-based ping discovery module
[x] [4] infogather:ttl_calc - TCP and UDP based TTL distance calculation
[x] [5] infogather:portscan - TCP and UDP PortScanner
[x] [6] fingerprint:icmp_echo - ICMP Echo request fingerprinting module
[x] [7] fingerprint:icmp_tstamp - ICMP Timestamp request fingerprinting module
[x] [8] fingerprint:icmp_amask - ICMP Address mask request fingerprinting module
[x] [9] fingerprint:icmp_port_unreach - ICMP port unreachable
fingerprinting module
[x] [10] fingerprint:tcp_hshake - TCP Handshake fingerprinting module
[x] [11] fingerprint:tcp_rst - TCP RST fingerprinting module
[x] [12] fingerprint:smb - SMB fingerprinting module
[x] [13] fingerprint:snmp - SNMPv2c fingerprinting module
[+] 13 modules registered
[+] Initializing scan engine
[+] Running scan engine
[-] ping:tcp_ping module: no closed/open TCP ports known on 124.163.204.105.
Module test failed
[-] ping:udp_ping module: no closed/open UDP ports known on 124.163.204.105.
Module test failed
[-] No distance calculation. 124.163.204.105 appears to be dead or no ports known
[+] Host: 124.163.204.105 is up (Guess probability: 50%)
[+] Target: 124.163.204.105 is alive. Round-Trip Time: 0.01528 sec
[+] Selected safe Round-Trip Time value is: 0.03056 sec
[-] fingerprint:tcp_hshake Module execution aborted (no open TCP ports known)
[-] fingerprint:smb need either TCP port 139 or 445 to run
[-] fingerprint:snmp: need UDP port 161 open
[+] Primary guess:
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.02 EEPROM G.07.17" (Guess probability: 83%)
[+] Other guesses:
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.02 EEPROM G.07.20" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.02 EEPROM G.08.04" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.19 EEPROM G.07.20" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.19 EEPROM G.08.03" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.07.19 EEPROM G.08.04" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.08.08 EEPROM G.08.04" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.08.21 EEPROM G.08.21" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM H.07.15 EEPROM H.08.20" (Guess probability: 83%)
[+] Host 124.163.204.105 Running OS: "HP JetDirect ROM G.06.00 EEPROM G.06.00" (Guess probability: 83%)
[+] Cleaning up scan engine
[+] Modules deinitialized
[+] Execution completed.
從以上輸出的信息中可以看到,執行結果出錯了(HP JetDirect ROM G.07.02 EEPROM G.07.17)。
在Kali Linux的新版本中,xProbe2工具運行后,測試的結果中操作系統類型顯示為亂碼。具體如下:
[+] Primary guess:
[+] Host 192.168.1.8 Running OS: ????U (Guess probability: 100%)
[+] Other guesses:
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Host 192.168.1.8 Running OS: ?????U (Guess probability: 100%)
[+] Cleaning up scan engine
[+] Modules deinitialized
[+] Execution completed.
4. p0f系統識別
p0f是一款用于識別遠程操作系統的工具,該工具與前面介紹的其他工具不同,它是一個完全被動地識別操作系統指紋信息的工具,不會直接作用于目標系統。當啟動該工具后,即可監聽網絡中的所有數據包。通過分析監聽到的數據包,即可找出與系統相關的信息。下面介紹使用p0f工具來實施操作系統指紋識別的方法。
使用p0f工具對目標主機實施系統識別。執行命令如下:
1)啟動p0f工具。執行命令如下:
root@daxueba:~# p0f
--- p0f 3.09b by Michal Zalewski ---
[+] Closed 1 file descriptor.
[+] Loaded 322 signatures from '/etc/p0f/p0f.fp'.
[+] Intercepting traffic on default interface 'eth0'.
[+] Default packet filtering configured [+VLAN].
[+] Entered main event loop.
從以上輸出信息中可以看到,p0f工具僅顯示了幾行信息,無法捕獲到其他信息。但是,p0f會一直處于監聽狀態。
2)此時,當有其他主機在網絡中產生數據流量的話,將會被p0f工具監聽到。例如,在另一臺主機上通過瀏覽器訪問一個站點,然后返回到p0f所在的終端,將看到如下信息:
.-[ 192.168.1.4/38934 -> 65.200.22.161/80 (http request) ]- #HTTP請求
| client = 192.168.1.4/38934 #客戶端
| app = Safari 5.1-6 #應用
| lang = English #語言
| params = dishonest #程序
| raw_sig = 1:Host,User-Agent,Accept=[*/*],Accept-Language=[en-US,en;q=0.5],Accept-Encoding=[gzip, deflate],?Cache-Control,Pragma=[no-cache],Connection=[keep-alive]:Accept-Charset,Keep-Alive:Mozilla/5.0 (X11; Linux x86_64; rv:60.0) Gecko/20100101 Firefox/60.0 #數據內容
----
.-[ 192.168.1.4/38934 -> 65.200.22.161/80 (uptime) ]-
| server = 65.200.22.161/80 #服務器
| uptime = 30 days 0 hrs 22 min (modulo 45 days) #時間
| raw_freq = 1048.46 Hz #頻率
----
.-[ 192.168.1.4/38934 -> 65.200.22.161/80 (http response) ]-
| server = 65.200.22.161/80
| app = ???
| lang = none
| params = none
| raw_sig = 1:Content-Type,?Content-Length,?Last-Modified,?ETag,Accept-Ranges=[bytes],Server,X-Amz-Cf-Id=[X7nIiIIBBeQOTeLSHRH3U4SM6xDHfgwK1EaKf8bdyemtuUoR8JK9Xg==],?Cache-Control,Date,Connection=[keep-alive]:Keep-Alive:AmazonS3
----
.-[ 192.168.1.4/32854 -> 52.27.184.151/443 (syn) ]-
| client = 192.168.1.4/32854
| os = Linux 3.11 and newer
| dist = 0
| params = none
| raw_sig = 4:64+0:0:1460:mss*20,7:mss,sok,ts,nop,ws:df,id+:0
----
.-[ 192.168.1.4/32854 -> 52.27.184.151/443 (host change) ]-
| client = 192.168.1.4/32854
| reason = tstamp port
| raw_hits = 0,1,1,1
----
.-[ 192.168.1.4/32854 -> 52.27.184.151/443 (mtu) ]-
| client = 192.168.1.4/32854
| link = Ethernet or modem
| raw_mtu = 1500
----
.-[ 192.168.1.4/32856 -> 52.27.184.151/443 (syn) ]-
| client = 192.168.1.4/32856
| os = Linux 3.11 and newer
| dist = 0
| params = none
| raw_sig = 4:64+0:0:1460:mss*20,7:mss,sok,ts,nop,ws:df,id+:0
----
以上輸出的信息,就是執行監聽到客戶端訪問的數據信息。從以上輸出的信息可以看到,探測到客戶端的操作系統類型為Linux 3.11或更新的內核版本。