測試一下GitHub公開的Windows系統提權漏洞,github連接
https://github.com/apt69/COMahawk/
該漏洞利用項目使用了二個CVE編號,我們使用SHC-Update漏洞數據訂閱分析工具提取CVE-2019-1405和CVE-2019-1322漏洞公開信息。

CVE-2019-1405漏洞時間梳理漏洞創建時間:2019-01-01 0:00:00漏洞披露時間:2019-11-12 19:15:00漏洞修改時間:2023-10-06 17:13:27

CVE-2019-1322漏洞時間梳理漏洞創建時間:2019-01-01 0:00:00漏洞披露時間:2019-10-10 14:15:00漏洞修改時間:2023-10-06 16:21:03
漏洞簡要分析第一個漏洞CVE-2019-1405是COM服務中的一個邏輯錯誤,可讓本地普通用戶以LOCAL SERVICE身份執行任意命令。第二個漏洞CVE-2019-1322是一個簡單的服務配置錯誤,可讓本地SERVICE組中的任何用戶重新配置以SYSTEM權限運行的服務(此漏洞也被其他研究人員發現)。當以上兩個漏洞結合在一起時,就允許本地普通用戶以SYSTEM權限執行任意命令。可以發現漏洞創建時間都是在一起的。
CVE-2019-1405影響版本[ "Windows 7 for 32-bit Systems Service Pack 1", "Windows 7 for x64-based Systems Service Pack 1", "Windows 8.1 for 32-bit systems", "Windows 8.1 for x64-based systems", "Windows RT 8.1", "Windows 10 for 32-bit Systems", "Windows 10 for x64-based Systems", "Windows 10 Version 1607 for 32-bit Systems", "Windows 10 Version 1607 for x64-based Systems", "Windows 10 Version 1709 for 32-bit Systems", "Windows 10 Version 1709 for x64-based Systems", "Windows 10 Version 1803 for 32-bit Systems", "Windows 10 Version 1803 for x64-based Systems", "Windows 10 Version 1803 for ARM64-based Systems", "Windows 10 Version 1809 for 32-bit Systems", "Windows 10 Version 1809 for x64-based Systems", "Windows 10 Version 1809 for ARM64-based Systems", "Windows 10 Version 1709 for ARM64-based Systems", "Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Core installation)", "Windows Server 2008 R2 for Itanium-Based Systems Service Pack 1", "Windows Server 2008 R2 for x64-based Systems Service Pack 1", "Windows Server 2008 for 32-bit Systems Service Pack 2 (Core installation)", "Windows Server 2012", "Windows Server 2012 (Core installation)", "Windows Server 2012 R2", "Windows Server 2012 R2 (Core installation)", "Windows Server 2016", "Windows Server 2016 (Core installation)", "Windows Server version 1803 (Core Installation)", "Windows Server 2019", "Windows Server 2019 (Core installation)", "Windows Server 2008 for Itanium-Based Systems Service Pack 2", "Windows Server 2008 for 32-bit Systems Service Pack 2", "Windows Server 2008 for x64-based Systems Service Pack 2", "Windows Server 2008 for x64-based Systems Service Pack 2 (Core installation)", "Windows 10 Version 1903 for 32-bit Systems ", "Windows 10 Version 1903 for x64-based Systems ", "Windows 10 Version 1903 for ARM64-based Systems ", "Windows Server, version 1903 (Server Core installation) "]CVE-2019-1322影響版本[ "Windows 10 Version 1803 for 32-bit Systems", "Windows 10 Version 1803 for x64-based Systems", "Windows 10 Version 1803 for ARM64-based Systems", "Windows 10 Version 1809 for 32-bit Systems", "Windows 10 Version 1809 for x64-based Systems", "Windows 10 Version 1809 for ARM64-based Systems", "Windows Server version 1803 (Core Installation)", "Windows Server 2019", "Windows Server 2019 (Core installation)", "Windows 10 Version 1903 for 32-bit Systems ", "Windows 10 Version 1903 for x64-based Systems ", "Windows 10 Version 1903 for ARM64-based Systems ", "Windows Server, version 1903 (Server Core installation) "]
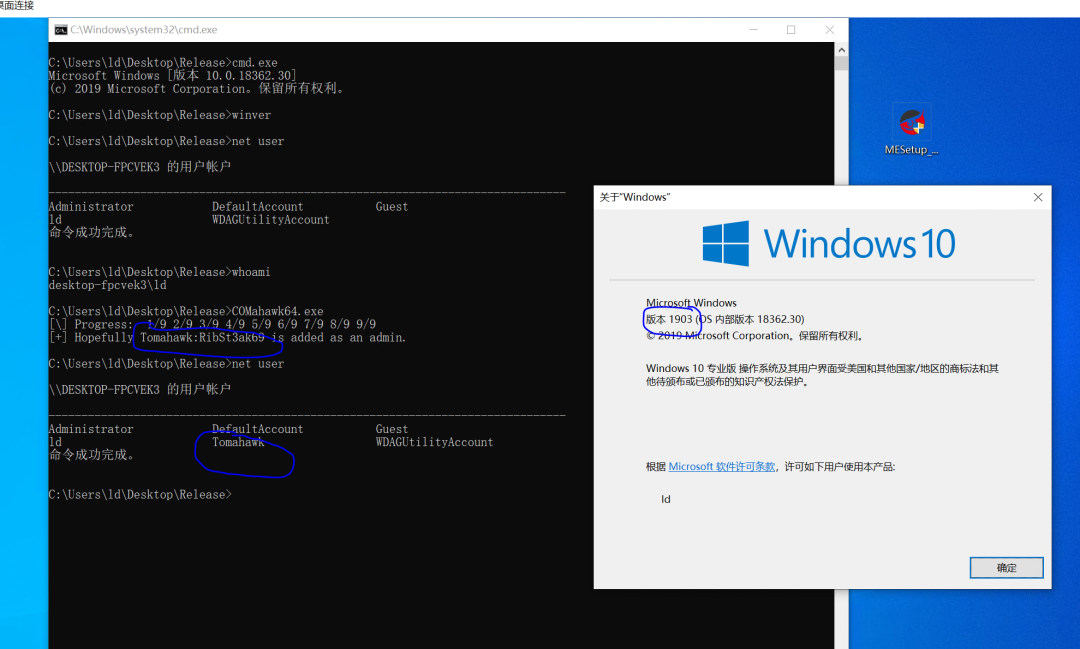
測試目標只要符合這上面的二個CVE編號影響版本條件,就可以利用成功,安裝部署好復雜之眼EDR,測試的是Windows10版本1903符合利用條件,漏洞利用成功低權限用戶成功添加Tomahawk賬號,RibSt3ak69密碼。
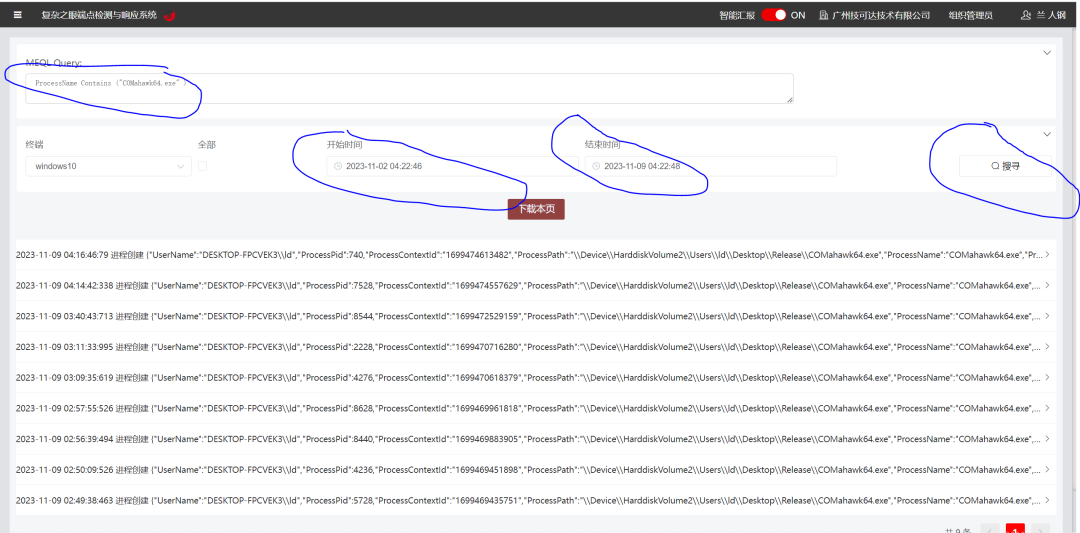
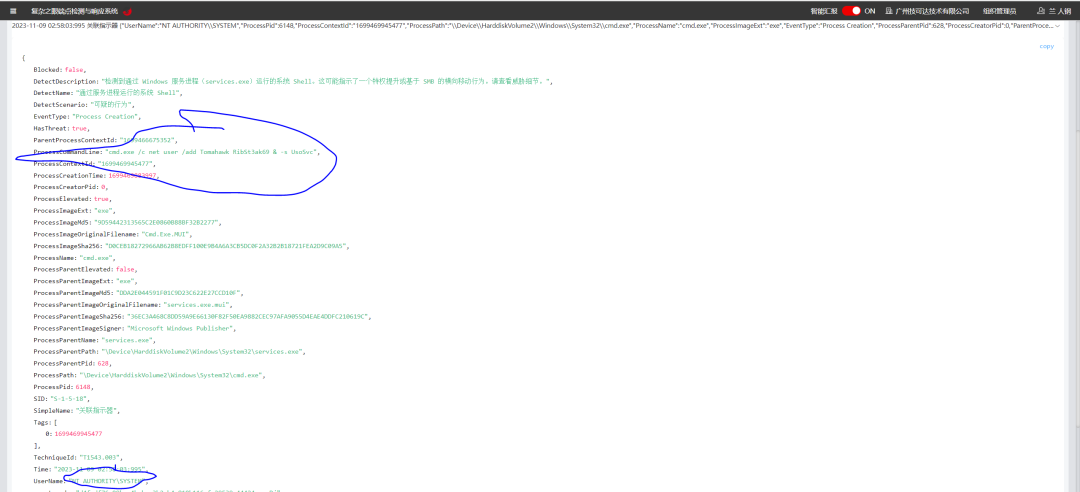
通過復雜之眼EDR查看觸發告警,下方是CVE-2019-1405和CVE-2019-1322漏洞利用活動細節,可以看到持久化的告警添加賬號。

COMahawk64.exe是CVE-2019-1405和CVE-2019-1322漏洞利用程序,可以看到執行時間和執行次數。可以看到使用事件獵手根據時間線去排查尋找該漏洞利用IOA攻擊指標。
這是搭建的模擬環境真實業務生產環境,復雜之眼開啟主動防御可以攔截CVE-2019-1405和CVE-2019-1322利用活動。
 FreeBuf
FreeBuf
 007bug
007bug
 cayman
cayman
 上官雨寶
上官雨寶
 007bug
007bug
 007bug
007bug
 007bug
007bug
 007bug
007bug
 上官雨寶
上官雨寶
 007bug
007bug
 FreeBuf
FreeBuf

