komo簡介
Komo是一個綜合資產收集和漏洞掃描工具,并且支持進度記錄,通過多種方式對子域進行獲取,收集域名,郵箱,子域名存活探測,域名指紋識別,域名反查ip,ip端口掃描,web服務鏈接爬取并發送給xray掃描,對web服務進行POC掃描,web弱口令掃描,對主機進行主機POC掃描,常見端口弱口令掃描。
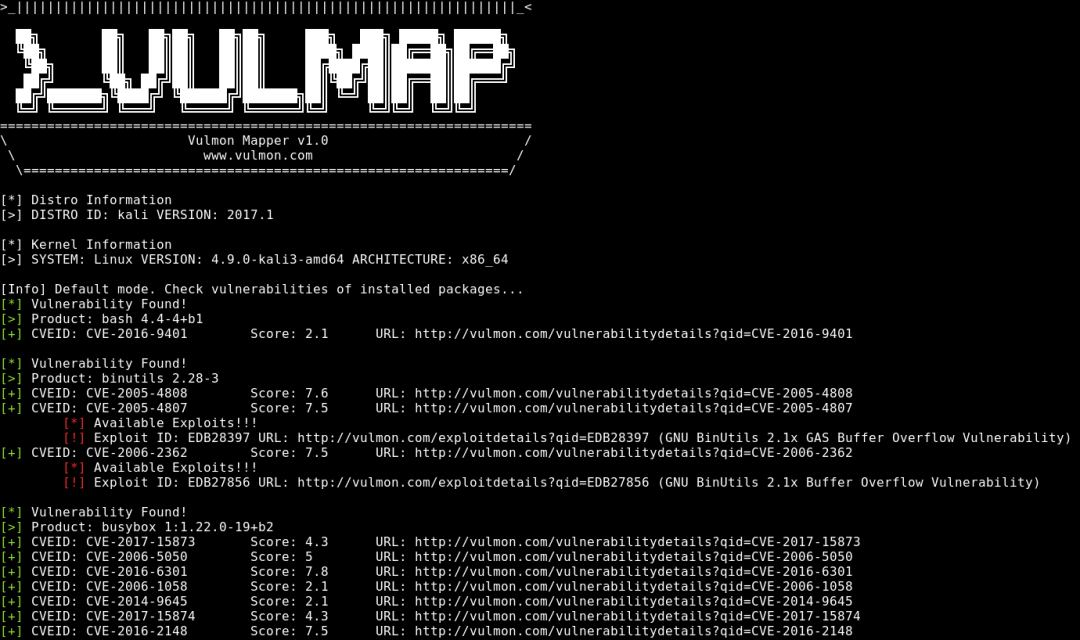
Komo集成了oneforall,subfinder,ksubdomain,amass,ctfr,emailall,httpx,naabu,TxPortMap,ehole,goon3,crawlergo,rad,hakrawler,gau,gospider,URLfinder,vscan,nuclei,afrog,vulmap,SweetBabyScan,xray等20多款工具,全自動化、智能化工具。本工具依托各工具特色,進行模塊化構建。

配置
配置文件config/config.yaml
部分配置講解
修改有runtime字段的工具的runtime字段,設置工具的運行時間,如果超時則kill掉,推薦設置600-1200s
crawlergo:
toolname: crawlergo
runtime: 900
rad:
toolname: rad
runtime: 900
修改xray的監聽端口
other:
xray:
toolname: xray
listenport: 7777 #修改監聽端口
其他配置為以后擴充開發預留配置,暫時不用修改。
初始化
安裝python3(python2暫時不支持)
安裝相應的庫文件pip3 install -r requirements.txt
第一次使用下載所需工具,以及部分工具初始化(goon,vulmap,afrog)
python3 Komo.py install
如果下載失敗,則需要手動去下載對應工具到對應目錄。
下載鏈接
github原始鏈接:
https://github.com/komomon/Komo
附帶工具下載鏈接
https://commondatastorage.googleapis.com/chromium-browser-snapshots/Win_x64/1051001/chrome-win.zip https://github.com/4dogs-cn/TXPortMap/releases/download/v1.1.2/TxPortMap_windows_x64.exe https://github.com/boy-hack/ksubdomain/releases/download/v1.9.5/KSubdomain-windows.tar https://github.com/chaitin/rad/releases/download/0.4/rad_windows_amd64.exe.zip https://github.com/i11us0ry/goon/releases/download/v3.5/goon3_win_amd64.zip https://github.com/inbug-team/SweetBabyScan/releases/download/v0.1.0/SbScanAmd64.exe https://github.com/jaeles-project/gospider/releases/download/v1.1.6/gospider_v1.1.6_windows_x86_64.zip https://github.com/lc/gau/releases/download/v2.1.2/gau_2.1.2_windows_amd64.zip https://github.com/maurosoria/dirsearch/archive/refs/heads/master.zip https://github.com/OWASP/Amass/releases/download/v3.21.2/amass_windows_amd64.zip https://github.com/pingc0y/URLFinder/blob/master/URLFinder-windows64.exe?raw=true https://github.com/projectdiscovery/httpx/releases/download/v1.2.4/httpx_1.2.4_windows_amd64.zip https://github.com/projectdiscovery/naabu/releases/download/v2.1.1/naabu_2.1.1_windows_amd64.zip https://github.com/projectdiscovery/nuclei/releases/download/v2.8.3/nuclei_2.8.3_windows_amd64.zip https://github.com/projectdiscovery/subfinder/releases/download/v2.5.3/subfinder_2.5.3_windows_amd64.zip https://github.com/Qianlitp/crawlergo/releases/download/v0.4.4/crawlergo_win_amd64.exe https://github.com/rverton/webanalyze/releases/download/v0.3.8/webanalyze_0.3.8_Windows_x86_64.tar.gz https://github.com/shmilylty/OneForAll/blob/master/data/ip2location.zip?raw=true https://github.com/shmilylty/OneForAll/blob/master/data/ip2region.db?raw=true https://github.com/shmilylty/OneForAll/blob/master/data/subnames_big.7z?raw=true https://github.com/veo/vscan/releases/download/v2.1.0/vscan_2.1.0_windows_amd64.zip https://github.com/zan8in/afrog/releases/download/v2.1.1/afrog_2.1.1_windows_amd64.zip https://github.com/zhzyker/vulmap/archive/refs/tags/v0.9.zip
Komo 支持多種模式
install:下載所有工具
all: 資產收集+攻擊,多種方式收集域名,收集域名郵箱,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取,將爬取的鏈接發送給xray進行掃描,POC漏洞掃描,反查的ip進行其他端口漏洞掃描,弱口令掃描
all2: 資產收集+攻擊,提供子域名,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取,將爬取的鏈接發送給xray進行掃描,POC漏洞掃描,反查的ip進行其他端口漏洞掃描,弱口令掃描
collect:只資產收集,多種方式收集域名,收集域名郵箱,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取
subdomain: 通過多種方式進行域名收集,dns爬取,爆破,證書獲取,DNS運營商處獲取。
finger: 對收集到的域名或域名文件進行存活探測和指紋識別(Ehole+wapplyzer)
portscan:對反查的ip列表或ip文件進行端口掃描
sensitive:對收集到的存活域名或域名文件進行url爬取
webattack:對收集到的存活域名或域名文件進行url爬取,然后發送給xray進行掃描,同時也調用nuclei,afrog,vulmap,vscan進行漏洞掃描
hostattack:對反查的ip列表或ip文件進行常見服務弱口令掃描和漏洞掃描
install 下載所有工具
功能:根據系統下載所有工具以及部分工具初始化
python3 Komo.py install
all 全掃描
輸入:域名/域名文件
功能:多種方式收集域名,收集域名,郵箱,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取,將爬取的鏈接發送給xray進行掃描,POC漏洞掃描,反查的ip進行其他端口漏洞掃描,弱口令掃描
python3 Komo.py --domain example.com all python3 Komo.py --domains ./domains.txt all
注意:記得使用該模式之前先啟動xray,否則webattack不能完全掃描
xray.exe webscan --listen 127.0.0.1:7777 --html-output 1.html
all2
輸入:子域名/子域名文件
功能:提供子域名,不掃描子域,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取,將爬取的鏈接發送給xray進行掃描,POC漏洞掃描,反查的ip進行其他端口漏洞掃描,弱口令掃描
python3 Komo.py --subdomain aaa.example.com all2 python3 Komo.py --subdomains ./subdomains.txt all2
注意:記得使用該模式之前先啟動xray,否則webattack不能完全掃描
xray.exe webscan --listen 127.0.0.1:7777 --html-output 1.html
collect
輸入:域名/域名文件
功能:全方位資產收集,多種方式收集域名,收集域名,郵箱,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描,web服務鏈接爬取
python3 Komo.py --domain example.com collect python3 Komo.py --domains ./domains.txt collect
collect1
輸入:域名/域名文件
功能:只資產收集,多種方式收集域名,收集域名,域名存活探測,域名反查ip,域名指紋識別
功能比collect 少了端口掃描,web鏈接爬取
python3 Komo.py --domain example.com collect1 python3 Komo.py --domains ./domains.txt collect1
collect2
輸入:域名/域名文件
功能:只資產收集,多種方式收集域名,收集域名,郵箱,域名存活探測,域名反查ip,域名指紋識別,ip端口掃描
功能比collect 少了web鏈接爬取
python3 Komo.py --domain example.com collect2 python3 Komo.py --domains ./domains.txt collect2
subdomain
輸入:域名/域名文件
功能:通過多種方式進行域名收集,dns爬取,爆破,證書獲取,DNS運營商處獲取。
python3 Komo.py --domain example.com subdomain python3 Komo.py --domains ./domains.txt subdomain
finger
輸入:url/url文件
功能:對收集到的域名或域名文件進行存活探測和指紋識別(Ehole+wapplyzer)
python3 Komo.py --url http://example.com finger python3 Komo.py --urls ./urls.txt finger
portscan
輸入:ip/ip文件
功能:對反查的ip列表或ip文件進行端口掃描和端口指紋識別
默認端口掃描列表
21,22,23,25,53,53,69,80,81,88,110,111,111,123,123,135,137,139,161,177,389,427,443,445,465,500,515,520,523,548,623,626,636,873,902,1080,1099,1433,1434,1521,1604,1645,1701,1883,1900,2049,2181,2375,2379,2425,3128,3306,3389,4730,5060,5222,5351,5353,5432,5555,5601,5672,5683,5900,5938,5984,6000,6379,7001,7077,8080,8081,8443,8545,8686,9000,9001,9042,9092,9100,9200,9418,9999,11211,11211,27017,33848,37777,50000,50070,61616 python3 Komo.py --ip 1.1.1.1 portscan python3 Komo.py --ips ./ips.txt portscan
sensitive
輸入:url/url文件
功能:對收集到的存活域名或域名文件進行url爬取(crawlergo,rad,gau,URLFinder,gospider,hakrawler)
python3 Komo.py --url http://example.com sensitive python3 Komo.py --urls ./urls.txt sensitive
webattack
輸入:url/url文件
功能:對url進行爬取,然后發送給xray進行掃描,同時也調用nuclei,afrog,vulmap,vscan進行漏洞掃描
python3 Komo.py --url http://example.com webattack python3 Komo.py --urls ./urls.txt webattack
注意:記得使用該模式之前先啟動xray,否則webattack不能完全掃描
xray.exe webscan --listen 127.0.0.1:7777 --html-output 1.html
webattack2
輸入:url/url文件
功能:只進行poc掃描(nuclei,afrog,vulmap,vscan)
python3 Komo.py --url http://example.com webattack2 python3 Komo.py --urls ./urls.txt webattack2
hostattack
輸入:ip/ip文件
功能:對反查的ip列表或ip文件進行常見服務弱口令掃描和漏洞掃描
python3 Komo.py --ip 1.1.1.1 hostattack python3 Komo.py --ips ./ips.txt hostattack
完整Usage
Komo help summary page
Komo is an automated scanning tool set
mode:
install Download the required tools
all all scan and attack:subdomain, survival detection, finger, portscan, email collect, sensitive(crawl urls), pocscan, Weak password scanning, to_xray
--domain one domain
--domains a domain file
all2 run scan and attack except domain collection: survival detection, finger, portscan, email collect, sensitive(crawl urls), pocscan, Weak password scanning, to_xray
--subdomain one subdomain
--subdomains a subdomain file
collect run all collection modules :subdomain, survival detection, finger, port, email collect, sensitive(crawl urls), pocscan, to_xray
--domain one domain
--domains a domain file
collect1 run collection modules :subdomain, survival detection, finger
--domain one domain
--domains a domain file
collect2 run collection modules :subdomain, survival detection, finger, portscan
--domain one domain
--domains a domain file
subdomain only collect subdomain
--domain one domain
--domains a domains file
finger only collect the survival URL and fingerprint
--url one url
--urls an urls file
portscan only collect port from ip or ips
--ip one ip
--ips an ips file
sensitive only collect directory with crawl,email
--url one url
--urls an urls file
webattack only attack web from url or urls: pocscan, Weak password scanning, crawl urls to xray
--url one url
--urls an urls file
webattack2 only poc scan from url or urls: pocscan, Weak password scanning
--url one url
--urls an urls file
hostattack only attack ip from ip or ips
--ip one ip
--ips an ips file
attack run webattack and hostattack: crawl url to xray, pocscan, Weak password scanning
Example:
python3 Komo.py install
python3 Komo.py --domain example.com all
python3 Komo.py --domains ./domains.txt all
python3 Komo.py --domain example.com collect
python3 Komo.py --domains ./domains.txt collect
python3 Komo.py --domain example.com collect1
python3 Komo.py --domains ./domains.txt collect1
python3 Komo.py --domain example.com collect2
python3 Komo.py --domains ./domains.txt collect2
python3 Komo.py --domain example.com subdomain
python3 Komo.py --domains ./domains.txt subdomain
python3 Komo.py --subdomain aaa.example.com all2
python3 Komo.py --subdomains ./subdomains.txt all2
python3 Komo.py --url http://example.com finger
python3 Komo.py --urls ./urls.txt finger
python3 Komo.py --url http://example.com sensitive
python3 Komo.py --urls ./urls.txt sensitive
python3 Komo.py --url http://example.com webattack
python3 Komo.py --urls ./urls.txt webattack
python3 Komo.py --url http://example.com webattack2
python3 Komo.py --urls ./urls.txt webattack2
python3 Komo.py --ip example.com portscan
python3 Komo.py --ips ./domains.txt portscan
python3 Komo.py --ip example.com hostattack
python3 Komo.py --ips ./domains.txt hostattack
結果
Komo會將輸出結果記錄到result/{date} 目錄下
該目錄下會有多個文件夾,分別對應各個模塊的輸出:
domain_log
fingerlog
portscan_log
sensitive_log
vulscan_log
result/{date} 根目錄下會有輸出結果文件:
target 為domain或date
{target}.final.subdomains.txt 最終找到的所有子域名
{target}.links.csv 多個工具爬取到的所有link
{target}.many.tools.subdomains.txt 除oneforall之外的其他子域名收集工具收集到的域名
{target}.subdomains.ips.txt 域名反查的ip
{target}.subdomains.with.http.txt 存活的子域名并且帶http(s)
 GoUpSec
GoUpSec
 安全牛
安全牛
 關鍵基礎設施安全應急響應中心
關鍵基礎設施安全應急響應中心
 安全圈
安全圈
 GoUpSec
GoUpSec
 CNCERT國家工程研究中心
CNCERT國家工程研究中心
 黑白之道
黑白之道
 GoUpSec
GoUpSec
 嘶吼專業版
嘶吼專業版
 系統安全運維
系統安全運維
 聚銘網絡
聚銘網絡
 GoUpSec
GoUpSec

